Particulars have emerged a couple of beforehand undocumented and totally undetectable (FUD) PowerShell backdoor that good points its stealth by disguising itself as a part of a Home windows replace course of.
“The covert self-developed software and the related C2 instructions appear to be the work of a complicated, unknown risk actor who has focused roughly 100 victims,” Tomer Bar, director of safety analysis at SafeBreach, mentioned in a brand new report.
Attributed to an unnamed risk actor, assault chains involving the malware start with a weaponized Microsoft Phrase doc that, per the corporate, was uploaded from Jordan on August 25, 2022.
Metadata related to the lure doc signifies that the preliminary intrusion vector is a LinkedIn-based spear-phishing assault, which in the end results in the execution of a PowerShell script through a bit of embedded macro code.
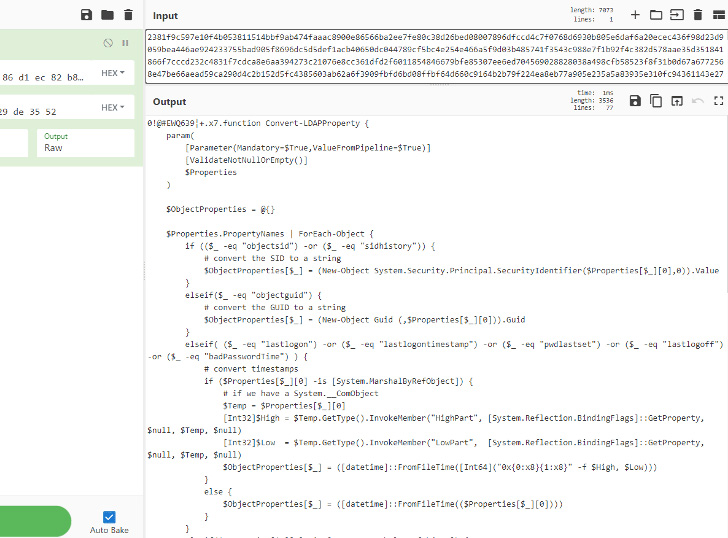
The PowerShell script (Script1.ps1) is designed to hook up with a distant command-and-control (C2) server and retrieve a command to be launched on the compromised machine via a second PowerShell script (temp.ps1).
However an operational safety error made by the actor by utilizing a trivial incremental identifier to uniquely establish every sufferer (i.e., 0, 1, 2, and so forth.) allowed for reconstructing the instructions issued by the C2 server.
A number of the notable instructions issued encompass exfiltrating the record of operating processes, enumerating information in particular folders, launching whoami, and deleting information underneath the general public consumer folders.
As of writing, 32 safety distributors and 18 anti-malware engines flag the decoy doc and the PowerShell scripts as malicious, respectively.
The findings come as Microsoft has taken steps to dam Excel 4.0 (XLM or XL4) and Visible Primary for Functions (VBA) macros by default throughout Workplace apps, prompting risk actors to pivot to various supply strategies.