Considerations over a important authentication bypass vulnerability in sure Fortinet home equipment heightened this week with the discharge of proof-of-concept (PoC) exploit code and a giant uptick in vulnerability scans for the flaw.
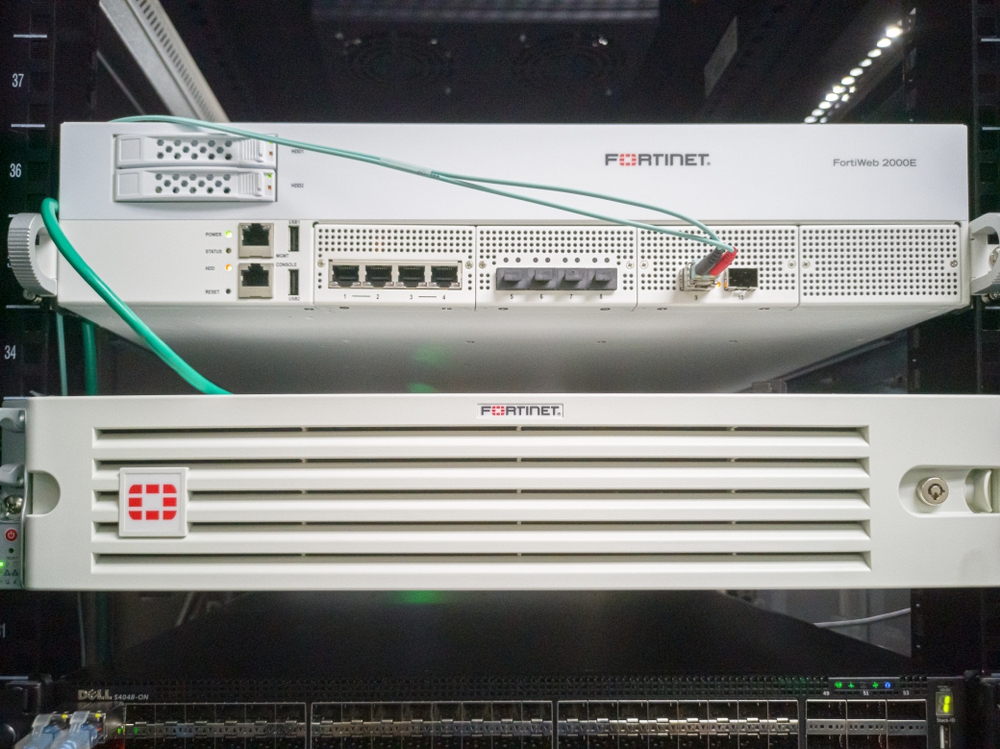
The bug (CVE-2022-40684) is current in a number of variations of Fortinet’s FortiOS, FortiProxy and FortiSwitchManager applied sciences. It permits an unauthenticated attacker to realize administrative entry to affected merchandise by way of specifically crafted HTTPS and HTTP requests, and doubtlessly use that as entry level to the remainder of the community.
Bharat Jogi, director of vulnerability menace analysis at Qualys says researchers on the firm have noticed mass scans being carried out by varied menace actors to determine Web going through weak programs for compromise.
“They’re compromising these programs to create a super_admin consumer which offers them with full entry and management,” Jogi says. “As soon as this degree of entry is achieved, they’ve the flexibility to delete any hint of their profitable exploitation try, making it tough for organizations to trace compromised belongings of their surroundings.”
If this flaw is efficiently exploited, an attacker would have full entry to the group’s inner programs that had been beforehand protected by Fortinet’s firewalls, he says. “Having a compromised firewall is like laying out a purple carpet for menace actors to walk proper into your group’s surroundings,” Jogi notes.
Added to CISA’s Recognized Exploited Vulnerabilities Catalog
The US Cybersecurity and Infrastructure Safety Company (CISA) earlier this week added the vulnerability to its Recognized Exploited Vulnerabilities catalog. Federal govt department businesses—that are required to remediate vulnerabilities within the catalog inside particular deadlines—have till Nov. 1 to handle it. Although the deadline applies solely to federal businesses, safety consultants have beforehand famous how it’s a good suggestion for all organizations to observe the vulnerabilities within the catalog and observe CISA’s deadline for implementing fixes.
Fortinet privately notified prospects of the affected merchandise in regards to the vulnerability final Friday, together with directions to right away replace to patched variations of the know-how the corporate had simply launched. It suggested corporations that might not replace for any purpose to right away disable Web-facing HTTPS administration till they might improve to the patched variations.
“As a result of potential to take advantage of this concern remotely, Fortinet is strongly recommending all prospects with the weak variations to carry out an instantaneous improve,” Fortinet mentioned in its non-public notification, a copy of which was posted on Twitter the identical day.
Fortinet adopted up with a public vulnerability advisory on Monday describing the flaw and warning prospects of potential exploit exercise. The corporate mentioned it was conscious of situations the place attackers had exploited the vulnerability to obtain the configuration file from affected programs and so as to add a malicious super_admin account referred to as “fortigate-tech-support”.
Since then, penetration testing from Horizon3.ai has launched proof-of-concept code for exploiting the vulnerability together with a technical deep dive of the flaw. A template for scanning for the vulnerability has additionally change into out there on GitHub.
Exacerbating the issues is the comparatively low bar for exploiting the flaw. “This vulnerability is extraordinarily straightforward for an attacker to take advantage of. All that’s required is entry to the administration interface on a weak system,” Zach Hanley, chief assault engineer at Horizon3.ai, tells Darkish Studying
Enhance in Scanning Exercise for the Flaw
Qualys is not the one firm observing elevated vulnerability scanning for the flaw. James Horseman, exploit developer at Horizon3.ai says public information from GreyNoise—which tracks Web scanning exercise hitting safety instruments—exhibits the variety of distinctive IPs utilizing the exploit has grown from the only digits a couple of days in the past, to over forty as of Oct. 14.
“We anticipate the variety of distinctive IPs utilizing this exploit to quickly enhance within the coming days,” Horseman says. It isn’t onerous for attackers to search out weak programs, he provides: A Shodan seek for occasion exhibits greater than 100,000 Fortinet programs worldwide.
“Not all of those can be weak, however a big proportion can be,” Horseman says.
Johannes Ullrich, dean of analysis on the SANS Institute, says he has noticed scans related to an older FortiGate vulnerability (CVE-2018-13379,) hitting SANS’ honeypots within the days following disclosure of the brand new bug. He says there are two theories why that is perhaps taking place.
One in every of them is that an attacker could have tried to catch as many units as potential that had not but been patched for the previous vulnerability. Given the eye the brand new vulnerability has gotten it’s possible the previous vulnerability will get patched as effectively now, he says.
“Or the attacker was looking for Fortinet units to take advantage of utilizing the brand new vulnerability as soon as it’s out there,” he theorizes. “The previous vulnerability scanner they’d sitting on the shelf should work to determine Fortinet units.”
A Widespread Attacker Goal
Considerations over vulnerabilities in Fortinet merchandise are usually not new. The corporate’s applied sciences—and people of others promoting comparable equipment—have been often focused by attackers attempting to realize an preliminary foothold on course community.
Final November. The FBI, CISA and others issued an advisory warning of Iranian superior persistent menace actors exploiting vulnerabilities in Fortinet and Microsoft merchandise. An identical alert in April 2021 warned of attackers exploiting flaws in FortiOS to interrupt into a number of authorities, business, and know-how providers.
“These weak units are sometimes edge units, so an attacker may doubtlessly use this vulnerability to realize entry to a corporation’s inner networks to launch additional assaults,” Hanley says.
Fortinet itself has really useful that organizations which might be in a position to, should replace to the newly patched variations of FortiOS, FortiProxy and FortiSwitch Supervisor. For organizations that can’t instantly replace, Fortinet has offered steerage on tips on how to disable the HTTP/HTTPS interface or restrict IP addresses that may attain the administrate interface of the affected merchandise.
Hanley says organizations generally could not be capable to patch because of the potential downtime related to updating a tool. “Nevertheless, a corporation ought to be capable to apply [the] workaround to forestall this vulnerability from being exploited on unpatched machines by following Fortinet’s steerage.”
Qualys’ Jogi provides, “It is usually essential to assessment any makes an attempt of exploit to determine programs which will have already been compromised. If a corporation is unable to patch their programs, then they need to disable the system admin interface instantly.”