[ad_1]
If you’ve ever owned a site identify, the possibilities are good that sooner or later you’ve obtained a snail mail letter which seems to be a invoice for a site or website-related providers. In actuality, these deceptive missives attempt to trick individuals into paying for ineffective providers they by no means ordered, don’t want, and possibly won’t ever obtain. Here’s a take a look at the latest incarnation of this rip-off — DomainNetworks — and a few clues about who could also be behind it.
The DomainNetworks mailer could reference a site that’s or was at one level registered to your identify and handle. Although the letter consists of the phrases “marketing services” within the higher proper nook, the remainder of the missive is deceptively designed to appear like a invoice for providers already rendered.
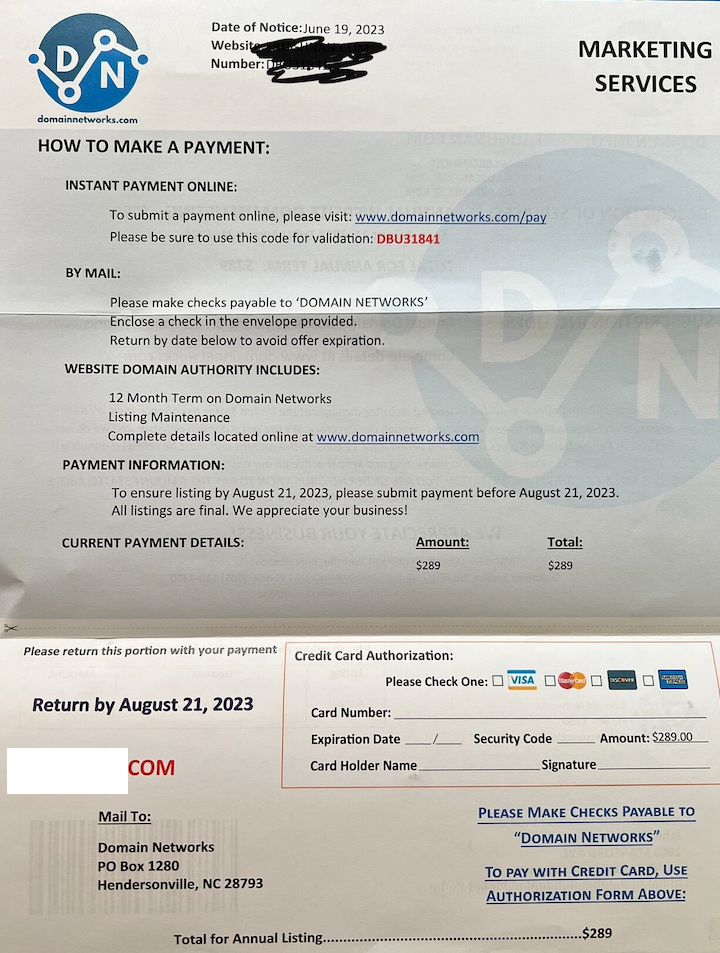
DomainNetworks claims that itemizing your area with their promotion providers will end in elevated site visitors to your website. This is a doubtful declare for an organization that seems to be a whole fabrication, as we’ll see in a second. But fortunately, the proprietors of this enterprise weren’t so troublesome to trace down.
The web site Domainnetworks[.]com says it’s a enterprise with a put up workplace field in Hendersonville, N.C., and one other handle in Santa Fe, N.M. There are just a few random, non-technology companies tied to the telephone quantity listed for the Hendersonville handle, and the New Mexico handle was utilized by a number of no-name hosting firms.
However, there may be little related to those addresses and telephone numbers that get us any nearer to discovering out who’s operating Domainnetworks[.]com. And neither entity seems to be an lively, official firm of their supposed state of residence, a minimum of based on every state’s Secretary of State database.
The Better Business Bureau itemizing for DomainNetworks provides it an “F” ranking, and consists of greater than 100 opinions by individuals indignant at receiving one in all these scams by way of snail mail. Helpfully, the BBB says DomainNetworks beforehand operated below a distinct identify: US Domain Authority LLC.
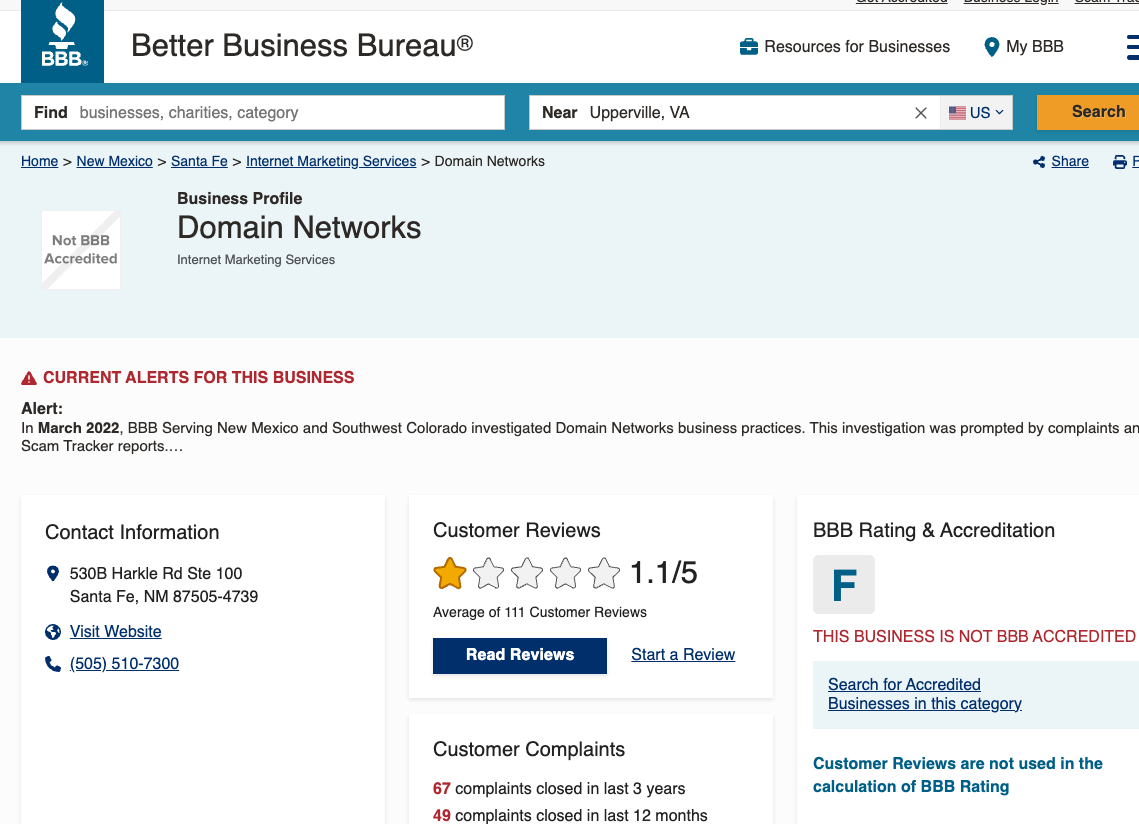
DomainNetworks has an “F” status with the Better Business Bureau.
Copies of snail mail rip-off letters from US Domain Authority posted on-line present that this entity used the area usdomainauthority[.]com, registered in May 2022. The Usdomainauthority mailer additionally featured a Henderson, NC handle, albeit at a distinct put up workplace field.
Usdomainauthority[.]com is now not on-line, and the positioning appears to have blocked its pages from being listed by the Wayback Machine at archive.org. But looking on a protracted snippet of textual content from DomainNetworks[.]com about refund requests reveals that this textual content was discovered on only one different lively web site, based on publicwww.com, a service that indexes the HTML code of present web sites and makes it searchable.
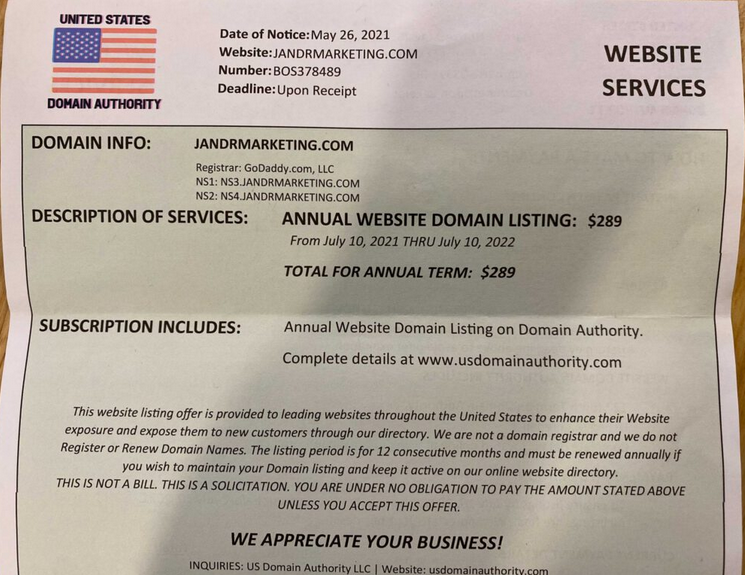
A misleading snail mail solicitation from DomainCommunity’s earlier iteration — US Domain Authority. Image: Joerussori.com
That different web site is a site registered in January 2023 referred to as thedomainsvault[.]com, and its registration particulars are likewise hidden behind privateness providers. Thedomainsvault’s “Frequently Asked Questions” web page is sort of just like the one on the DomainNetworks web site; each start with the query of why the corporate is sending a mailer that appears like a invoice for area providers.
Thedomainsvault[.]com consists of no helpful details about the entity or individuals who function it; clicking the “Contact-us” hyperlink on the positioning brings up a web page with placeholder Lorem Ipsum textual content, a contact kind, and a telephone variety of 123456789.
However, looking passive DNS information at DomainInstruments.com for thedomainsvault[.]com reveals that sooner or later whoever owns the area instructed incoming e mail to be despatched to ubsagency@gmail.com.
The first consequence that presently pops up when trying to find “ubsagency” in Google is ubsagency[.]com, which says it belongs to a Las Vegas-based Search Engine Optimization (web optimization) and digital advertising and marketing concern generically named each United Business Service and United Business Services. UBSagency’s web site is hosted on the similar Ann Arbor, Mich. primarily based internet hosting agency (A2 Hosting Inc) as thedomainsvault[.]com.
UBSagency’s LinkedIn web page says the corporate has workplaces in Vegas, Half Moon Bay, Calif., and Renton, Wash. But as soon as once more, not one of the addresses listed for these workplaces reveal any apparent clues about who runs UBSagency. And as soon as once more, none of those entities seem to exist as official companies of their claimed state of residence.
Searching on ubsagency@gmail.com in Constella Intelligence reveals the handle was used someday earlier than February 2019 to create an account below the identify “SammySam_Alon” on the inside adorning website Houzz.com. In January 2019, Houzz acknowledged {that a} knowledge breach uncovered account info on an undisclosed variety of prospects, together with consumer IDs, one-way encrypted passwords, IP addresses, metropolis and ZIP codes, in addition to Facebook info.
SammySam_Alon registered at Houzz utilizing an Internet handle in Huntsville, Ala. (68.35.149.206). Constella says this handle was related to the e-mail tropicglobal@gmail.com, which is also tied to a number of different “Sammy” accounts at totally different shops on-line.
Constella additionally says a extremely distinctive password re-used by tropicglobal@gmail.com throughout quite a few websites was utilized in reference to only a few different e mail accounts, together with shenhavgroup@gmail.com, and distributorinvoice@mail.com.
The shenhavgroup@gmail.com handle was used to register a Twitter account for a Sam Orit Alon in 2013, whose account says they’re affiliated with the Shenhav Group. According to DomainInstruments, shenhavgroup@gmail.com was answerable for registering roughly two dozen domains, together with the now-defunct unitedbusinessservice[.]com.
Constella additional finds that the handle distributorinvoice@mail.com was used to register an account at whmcs.com, a hosting platform that suffered a breach of its consumer database a number of years again. The identify on the WHMCS account was Shmuel Orit Alon, from Kidron, Israel.
UBSagency additionally has a Facebook web page, or perhaps “had” is the operative phrase as a result of somebody seems to have defaced it. Loading the Facebook web page for UBSagency reveals a number of of the pictures have been overlaid or changed with a message from somebody who’s actually dissatisfied with Sam Alon.
“Sam Alon is a LIAR, THIEF, COWARD AND HAS A VERY SMALL D*CK,” reads one of many messages:

The present Facebook profile web page for UBSagency features a emblem that’s just like the DomainNetworks emblem.
The emblem within the UBSagency profile picture features a graphic of what seems to be a magnifying glass with a line that zig-zags by means of bullet factors inside and out of doors the circle, a singular sample that’s remarkably just like the emblem for DomainNetworks:

The logos for DomainNetworks (left) and UBSagency.
Constella additionally discovered that the identical Huntsville IP handle utilized by Sam Alon at Houzz was related to one more Houzz account, this one for somebody named “Eliran.”
The UBSagency Facebook web page options a number of messages from an Eliran “Dani” Benz, who’s referred to by commenters as an worker or accomplice with UBSagency. The final check-in on Benz’s profile is from a seaside at Rishon Letziyon in Israel earlier this yr.
Neither Mr. Alon nor Mr. Benz responded to a number of requests for remark.
It could also be troublesome to imagine that anybody would pay an bill for a site identify or web optimization service they by no means ordered. However, there may be loads of proof that these phony payments usually get processed by administrative personnel at organizations that find yourself paying the requested quantity as a result of they assume it was owed for some providers already supplied.
In 2018, KrebsOnSecurity printed How Internet Savvy are Your Leaders?, which examined public information to indicate that dozens of cities, cities, college districts and even political campaigns throughout the United States bought snookered into paying these rip-off area invoices from an identical rip-off firm referred to as WebListings Inc.
In 2020, KrebsOnSecurity featured a deep dive into who was seemingly behind the WebListings rip-off, which had been sending out these snail mail rip-off letters for over a decade. That investigation revealed the rip-off’s connection to a multi-level advertising and marketing operation run out of the U.Ok., and to 2 brothers dwelling in Scotland.
[ad_2]
