[ad_1]
Code-signing certificates are supposed to assist authenticate the id of software program publishers, and supply cryptographic assurance {that a} signed piece of software program has not been altered or tampered with. Both of those qualities make stolen or ill-gotten code-signing certificates engaging to cybercriminal teams, who prize their means so as to add stealth and longevity to malicious software program. This submit is a deep dive on “Megatraffer,” a veteran Russian hacker who has virtually cornered the underground marketplace for malware targeted code-signing certificates since 2015.
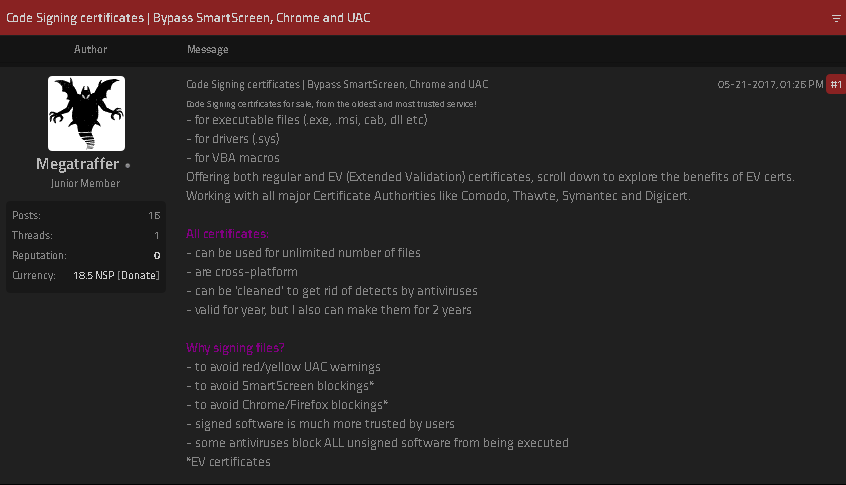
A evaluation of Megatraffer’s posts on Russian crime boards exhibits this person started peddling particular person stolen code-signing certs in 2015 on the Russian-language discussion board Exploit, and shortly expanded to promoting certificates for cryptographically signing purposes and recordsdata designed to run in Microsoft Windows, Java, Adobe AIR, Mac and Microsoft Office.
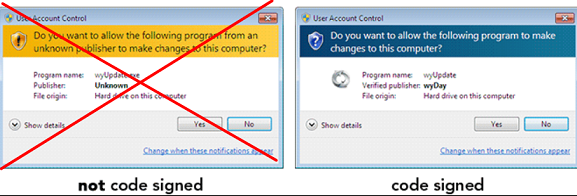
Megatraffer defined that malware purveyors want a certificates as a result of many antivirus merchandise shall be way more involved in unsigned software program, and since signed recordsdata downloaded from the Internet don’t are likely to get blocked by security measures constructed into fashionable internet browsers. Additionally, newer variations of Microsoft Windows will complain with a vibrant yellow or pink alert message if customers attempt to set up a program that isn’t signed.
“Why do I need a certificate?” Megatraffer requested rhetorically of their Jan. 2016 gross sales thread on Exploit. “Antivirus software trusts signed programs more. For some types of software, a digital signature is mandatory.”
At the time, Megatraffer was promoting distinctive code-signing certificates for $700 apiece, and charging greater than twice that quantity ($1,900) for an “extended validation” or EV code-signing cert, which is meant to solely include further id vetting of the certificates holder. According to Megatraffer, EV certificates have been a “must-have” in case you needed to signal malicious software program or {hardware} drivers that will reliably work in newer Windows working techniques.
Part of Megatraffer’s advert. Image: Ke-la.com.
Megatraffer has continued to supply their code-signing providers throughout greater than a half-dozen different Russian-language cybercrime boards, principally within the type of sporadically out there EV and non-EV code-signing certificates from main distributors like Thawte and Comodo.
More lately, it seems Megatraffer has been working with ransomware teams to assist enhance the stealth of their malware. Shortly after Russia invaded Ukraine in February 2022, somebody leaked a number of years of inside chat logs from the Conti ransomware gang, and people logs present Megatraffer was working with the group to assist code-sign their malware between July and October 2020.
WHO IS MEGATRAFFER?
According to cyber intelligence agency Intel 471, Megatraffer has been lively on greater than a half-dozen crime boards from September 2009 to the current day. And on most of those identities, Megatraffer has used the e-mail handle 774748@gmail.com. That similar electronic mail handle is also tied to 2 discussion board accounts for a person with the deal with “O.R.Z.”
Constella Intelligence, an organization that tracks uncovered databases, finds that 774748@gmail.com was utilized in reference to only a handful of passwords, however most steadily the password “featar24“. Pivoting off of that password reveals a handful of electronic mail addresses, together with akafitis@gmail.com.
Intel 471 exhibits akafitis@gmail.com was used to register one other O.R.Z. person account — this one on Verified[.]ru in 2008. Prior to that, akafitis@gmail.com was used as the e-mail handle for the account “Fitis,” which was lively on Exploit between September 2006 and May 2007. Constella discovered the password “featar24” additionally was used along side the e-mail handle spampage@yandex.ru, which is tied to one more O.R.Z. account on Carder[.]su from 2008.
The electronic mail handle akafitis@gmail.com was used to create a Livejournal weblog profile named Fitis that has a big bear as its avatar. In November 2009, Fitis wrote, “I am the perfect criminal. My fingerprints change beyond recognition every few days. At least my laptop is sure of it.”
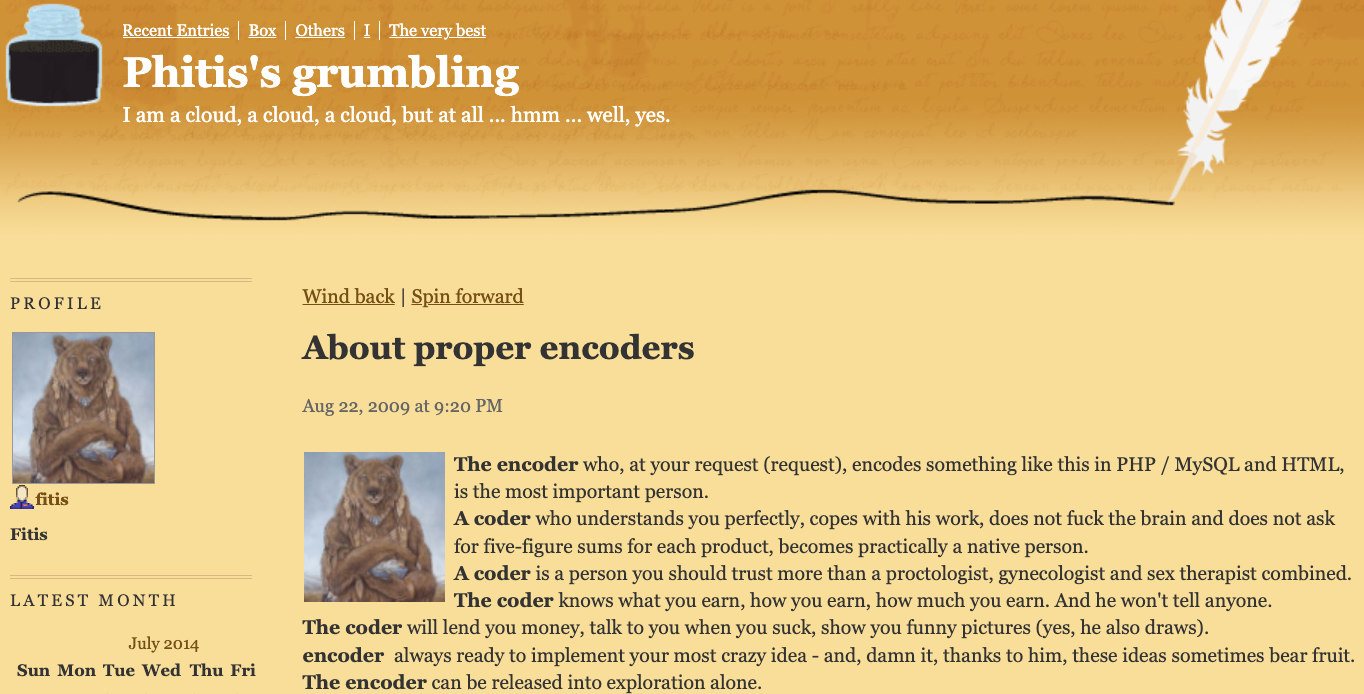
Fitis’s Livejournal account. Image: Archive.org.
Fitis’s real-life id was uncovered in 2010 after two of the most important sponsors of pharmaceutical spam went to warfare with one another, and enormous volumes of inside paperwork, emails and chat data seized from each spam empires have been leaked to this creator. That protracted and public battle fashioned the backdrop of my 2014 e book — “Spam Nation: The Inside Story of Organized Cybercrime, from Global Epidemic to Your Front Door.”
One of the leaked paperwork included a Microsoft Excel spreadsheet containing the actual names, addresses, cellphone numbers, emails, avenue addresses and WebMoney addresses for dozens of prime earners in Spamit — on the time probably the most profitable pharmaceutical spam associates program within the Russian hacking scene and one which employed most of the prime Russian botmasters.
That doc exhibits Fitis was considered one of Spamit’s most prolific recruiters, bringing greater than 75 associates to the Spamit program over a number of years previous to its implosion in 2010 (and incomes commissions on any future gross sales from all 75 associates).
The doc additionally says Fitis obtained paid utilizing a WebMoney account that was created when its proprietor introduced a sound Russian passport for a Konstantin Evgenievich Fetisov, born Nov. 16, 1982 and residing in Moscow. Russian motorcar data present two completely different autos are registered to this individual on the similar Moscow handle.
The most attention-grabbing area identify registered to the e-mail handle spampage@yahoo.com, fittingly sufficient, is fitis[.]ru, which DomainTools.com says was registered in 2005 to a Konstantin E. Fetisov from Moscow.
The Wayback Machine at archive.org has a handful of principally clean pages listed for fitis[.]ru in its early years, however for a short interval in 2007 it seems this web site was inadvertently exposing all of its file directories to the Internet.
One of the uncovered recordsdata — Glavmed.html — is a basic invitation to the notorious Glavmed pharmacy associates program, a now-defunct scheme that paid tens of thousands and thousands of {dollars} to associates who marketed on-line capsule retailers primarily by hacking web sites and manipulating search engine outcomes. Glavmed was operated by the identical Russian cybercriminals who ran the Spamit program.
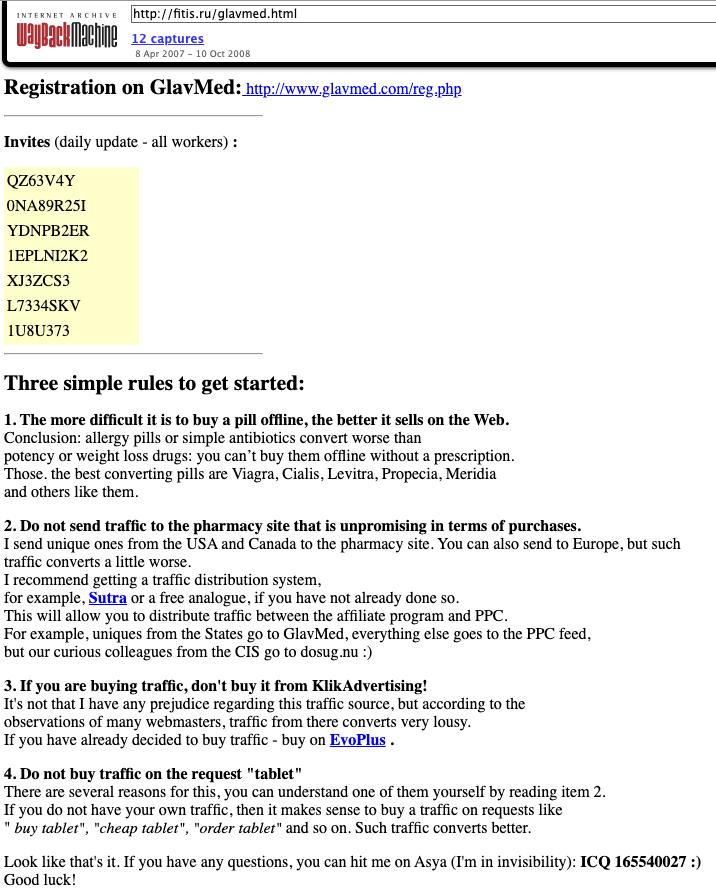
A Google translated advert circa 2007 recruiting for the pharmacy associates program Glavmed, which informed candidates to contact the ICQ quantity utilized by Fitis, a.okay.a. MegaTraffer. Image: Archive.org.
Archive.org exhibits the fitis[.]ru webpage with the Glavmed invitation was constantly up to date with new invite codes. In their message to would-be Glavmed associates, this system administrator requested candidates to contact them on the ICQ quantity 165540027, which Intel 471 discovered was an on the spot messenger handle beforehand utilized by Fitis on Exploit.
The uncovered recordsdata within the archived model of fitis[.]ru embody supply code for malicious software program, lists of compromised web sites used for pharmacy spam, and a handful of what are apparently private recordsdata and images. Among the images is a 2007 picture labeled merely “fitis.jpg,” which exhibits a bespectacled, bearded younger man with a ponytail standing subsequent to what seems to be a newly-married couple at a marriage ceremony.
Mr. Fetisov didn’t reply to requests for remark.
As a veteran organizer of affiliate packages, Fitis didn’t waste a lot time constructing a brand new moneymaking collective after Spamit closed up store. New York City-based cyber intelligence agency Flashpoint discovered that Megatraffer’s ICQ was the contact quantity for Himba[.]ru, a cost-per-acquisition (CPA) program launched in 2012 that paid handsomely for accomplished software kinds tied to a wide range of monetary devices, together with client bank cards, insurance coverage insurance policies, and loans.
“Megatraffer’s entrenched presence on cybercrime forums strongly suggests that malicious means are used to source at least a portion of traffic delivered to HIMBA’s advertisers,” Flashpoint noticed in a menace report on the actor.
Intel 471 finds that Himba was an lively associates program till round May 2019, when it stopping paying its associates.

Fitis’s Himba associates program, circa February 2014. Image: Archive.org.
Flashpoint notes that in September 2015, Megatraffer posted a job advert on Exploit searching for skilled coders to work on browser plugins, installers and “loaders” — mainly distant entry trojans (RATs) that set up communication between the attacker and a compromised system.
“The actor specified that he is looking for full-time, onsite help either in his Moscow or Kiev locations,” Flashpoint wrote.
[ad_2]