[ad_1]
Chrome 106 added help for implementing key pins on Android by default, bringing Android to parity with Chrome on desktop platforms. But what is vital pinning anyway?
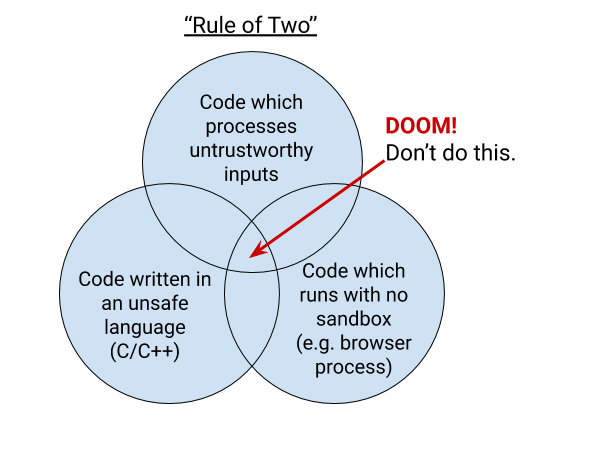
One of the explanations Chrome implements key pinning is the “rule of two”. This rule is a part of Chrome’s holistic safe growth course of. It says that when you’re writing code for Chrome, you’ll be able to choose not more than two of: code written in an unsafe language, processing untrustworthy inputs, and operating with no sandbox. This weblog submit explains how key pinning and the rule of two are associated.
The Rule of Two
Chrome is primarily written within the C and C++ languages, that are weak to reminiscence security bugs. Mistakes with pointers in these languages can result in reminiscence being misinterpreted. Chrome invests in an ever-stronger multi-process structure constructed on sandboxing and web site isolation to assist defend in opposition to reminiscence security issues. Android-specific options might be written in Java or Kotlin. These languages are memory-safe within the frequent case. Similarly, we’re engaged on including help to write Chrome code in Rust, which can also be memory-safe.
Much of Chrome is sandboxed, however the sandbox nonetheless requires a core high-privilege “broker” course of to coordinate communication and launch sandboxed processes. In Chrome, the dealer is the browser course of. The browser course of is the supply of reality that enables the remainder of Chrome to be sandboxed and coordinates communication between the remainder of the processes.
If an attacker is ready to craft a malicious enter to the browser course of that exploits a bug and permits the attacker to attain distant code execution (RCE) within the browser course of, that might successfully give the attacker full management of the sufferer’s Chrome browser and probably the remainder of the system. Conversely, if an attacker achieves RCE in a sandboxed course of, similar to a renderer, the attacker’s capabilities are extraordinarily restricted. The attacker can’t attain exterior of the sandbox except they will moreover exploit the sandbox itself.
Without sandboxing, which limits the actions an attacker can take, and with out reminiscence security, which removes the power of a bug to disrupt the supposed management movement of this system, the rule of two requires that the browser course of doesn’t deal with untrustworthy inputs. The relative dangers between sandboxed processes and the browser course of are why the browser course of is simply allowed to parse reliable inputs and particular IPC messages.
Trustworthy inputs are outlined extraordinarily strictly: A “trustworthy source” signifies that Chrome can show that the information comes from Google. Effectively, which means that in conditions the place the browser course of wants entry to knowledge from exterior sources, it have to be learn from Google servers. We can cryptographically show that knowledge got here from Google servers if that knowledge comes from:
The part updater and the variations framework are providers particular to Chrome used to ship data-only updates and configuration data. These providers each use uneven cryptography to authenticate their knowledge, and the general public key used to confirm knowledge despatched by these providers is shipped in Chrome.
However, Chrome is a feature-filled browser with many various use instances, and many various options past simply updating itself. Certain options, similar to Sign-In and the Discover Feed, want to speak with Google. For options like this, that communication might be thought-about reliable if it comes from a pinned HTTPS server.
When Chrome connects to an HTTPS server, the server says “a 3rd party you trust (a certification authority; CA) has vouched for my identity.” It does this by presenting a certificates issued by a trusted certification authority. Chrome verifies the certificates earlier than persevering with. The fashionable internet essentially has plenty of CAs, all of whom can present authentication for any web site. To additional be sure that the Chrome browser course of is speaking with a reliable Google server we wish to confirm one thing extra: whether or not a particular CA is vouching for the server. We do that by constructing a map of websites → anticipated CAs straight into Chrome. We name this key pinning. We name the map the pin set.
What is Key Pinning?
Key pinning was born as a protection in opposition to actual assaults seen within the wild: attackers who can trick a CA to difficulty a seemingly-valid certificates for a server, after which the attacker can impersonate that server. This occurred to Google in 2011, when the DigiNotar certification authority was compromised and used to difficulty malicious certificates for Google providers. To defend in opposition to this threat, Chrome accommodates a pin set for all Google properties, and we solely take into account an HTTPS enter reliable if it’s authenticated utilizing a key on this pin set. This protects in opposition to malicious certificates issuance by third events.
Key pinning might be brittle, and isn’t well worth the dangers. Allowing the pin set to get outdated can result in locking customers out of an internet site or different providers, probably completely. Whenever pinning, it’s essential to have safety-valves similar to not implementing pinning (i.e. failing open) when the pins have not been up to date lately, together with a “backup” key pin, and having fallback mechanisms for bootstrapping. It’s arduous for particular person websites to handle all of those mechanisms, which is why dynamic pinning over HTTPS (HPKP) was deprecated. Key pinning remains to be an essential device for some use instances, nevertheless, the place there’s high-privilege communication that should occur between a shopper and server which might be operated by the identical entity, similar to internet browsers, computerized software program updates, and bundle managers.
Security Benefits of Key Pinning in Chrome, Now on Android
By pinning in Chrome, we are able to shield customers from CA compromise. We take steps to forestall an out-of-date pinset from unnecessarily blocking customers from accessing Google or Google’s providers. As each a browser vendor and web site operator, nevertheless, we have now further instruments to make sure we hold our pin units updated—if we use a brand new key or a brand new area, we are able to add it to the pin set in Chrome on the similar time. In our unique implementation of pinning, the pin set is straight compiled into Chrome and updating the pin set requires updating your complete Chrome binary. To guarantee that customers of previous variations of Chrome can nonetheless discuss to Google, pinning is not enforced if Chrome detects that it’s greater than 10 weeks previous.
Historically, Chrome enforced the age restrict by evaluating the present time to the construct timestamp within the Chrome binary. Chrome didn’t implement pinning on Android as a result of the construct timestamp on Android wasn’t at all times reflective of the age of the Chrome pinset, which meant that the possibility of a false constructive pin mismatch was greater.
Without implementing pins on Android, Chrome was limiting the methods engineers may construct options that adjust to the rule of two. To take away this limitation, we constructed an improved mechanism for distributing the built-in pin set to Chrome installs, together with Android gadgets. Chrome nonetheless accommodates a built-in pin set compiled into the binary. However, we now moreover distribute the pin set by way of the part updater, which is a mechanism for Chrome to dynamically push out data-only updates to all Chrome installs with out requiring a full Chrome replace or restart. The part accommodates the most recent model of the built-in pin set, in addition to the certificates transparency log listing and the contents of the Chrome Root Store. This signifies that even when Chrome is outdated, it may nonetheless obtain updates to the pin set. The part additionally consists of the timestamp the pin listing was final up to date, fairly than counting on construct timestamp. This drastically reduces the false constructive threat of enabling key pinning on Android.
After we moved the pin set to part updater, we had been in a position to do a sluggish rollout of pinning enforcement on Android. We decided that the false constructive threat was now consistent with desktop platforms, and enabled key pinning enforcement by default since Chrome 106, launched in September 2022.
This change has been completely invisible to customers of Chrome. While not all the modifications we make in Chrome are flashy, we’re continuously working behind the scenes to maintain Chrome as safe as attainable and we’re excited to deliver this safety to Android.
[ad_2]