[ad_1]
KrebsOnSecurity final week was hit by a close to file distributed denial-of-service (DDoS) assault that clocked in at greater than 6.3 terabits of knowledge per second (a terabit is one trillion bits of knowledge). The temporary assault seems to have been a take a look at run for an enormous new Internet of Things (IoT) botnet able to launching crippling digital assaults that few internet locations can stand up to. Read on for extra concerning the botnet, the assault, and the obvious creator of this international menace.

For reference, the 6.3 Tbps assault final week was ten instances the scale of the assault launched towards this web site in 2016 by the Mirai IoT botnet, which held KrebsOnSecurity offline for practically 4 days. The 2016 assault was so giant that Akamai – which was offering pro-bono DDoS safety for KrebsOnSecurity on the time — requested me to depart their service as a result of the assault was inflicting issues for his or her paying clients.
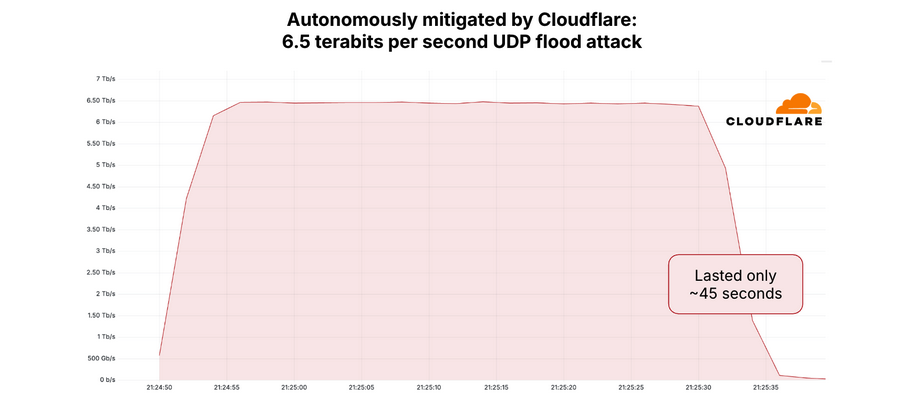
Since the Mirai assault, KrebsOnSecurity.com has been behind the safety of Project Shield, a free DDoS protection service that Google gives to web sites providing information, human rights, and election-related content material. Google Security Engineer Damian Menscher informed KrebsOnSecurity the May 12 assault was the most important Google has ever dealt with. In phrases of sheer dimension, it’s second solely to a really related assault that Cloudflare mitigated and wrote about in April.
After evaluating notes with Cloudflare, Menscher mentioned the botnet that launched each assaults bears the fingerprints of Aisuru, a digital siege machine that first surfaced lower than a 12 months in the past. Menscher mentioned the assault on KrebsOnSecurity lasted lower than a minute, hurling giant UDP knowledge packets at random ports at a charge of roughly 585 million knowledge packets per second.
“It was the type of attack normally designed to overwhelm network links,” Menscher mentioned, referring to the throughput connections between and amongst numerous Internet service suppliers (ISPs). “For most companies, this size of attack would kill them.”
The Aisuru botnet includes a globally-dispersed assortment of hacked IoT units, together with routers, digital video recorders and different programs which might be commandeered through default passwords or software program vulnerabilities. As documented by researchers at QiAnXin XLab, the botnet was first recognized in an August 2024 assault on a big gaming platform.
Aisuru reportedly went quiet after that publicity, solely to reappear in November with much more firepower and software program exploits. In a January 2025 report, XLab discovered the brand new and improved Aisuru (a.ok.a. “Airashi“) had included a beforehand unknown zero-day vulnerability in Cambium Networks cnPilot routers.
NOT FORKING AROUND
The individuals behind the Aisuru botnet have been peddling entry to their DDoS machine in public Telegram chat channels which might be intently monitored by a number of safety companies. In August 2024, the botnet was rented out in subscription tiers starting from $150 per day to $600 per week, providing assaults of as much as two terabits per second.
“You may not attack any measurement walls, healthcare facilities, schools or government sites,” learn a discover posted on Telegram by the Aisuru botnet house owners in August 2024.
Interested events have been informed to contact the Telegram deal with “@yfork” to buy a subscription. The account @yfork beforehand used the nickname “Forky,” an id that has been posting to public DDoS-focused Telegram channels since 2021.
According to the FBI, Forky’s DDoS-for-hire domains have been seized in a number of legislation enforcement operations through the years. Last 12 months, Forky mentioned on Telegram he was promoting the area stresser[.]greatest, which noticed its servers seized by the FBI in 2022 as a part of an ongoing worldwide legislation enforcement effort aimed toward diminishing the provision of and demand for DDoS-for-hire companies.
“The operator of this service, who calls himself ‘Forky,’ operates a Telegram channel to advertise features and communicate with current and prospective DDoS customers,” reads an FBI seizure warrant (PDF) issued for stresser[.]greatest. The FBI warrant said that on the identical day the seizures have been introduced, Forky posted a hyperlink to a narrative on this weblog that detailed the area seizure operation, including the remark, “We are buying our new domains right now.”
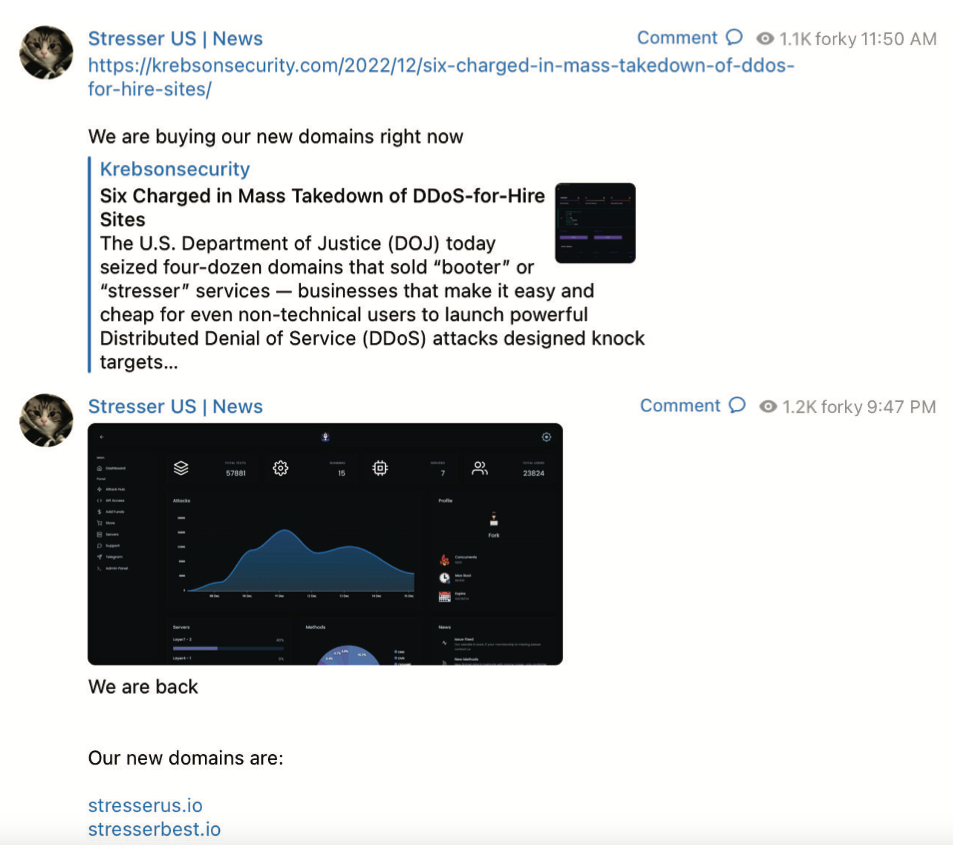
A screenshot from the FBI’s seizure warrant for Forky’s DDoS-for-hire domains exhibits Forky asserting the resurrection of their service at new domains.
Approximately ten hours later, Forky posted once more, together with a screenshot of the stresser[.]greatest consumer dashboard, instructing clients to make use of their saved passwords for the previous web site on the brand new one.
A evaluation of Forky’s posts to public Telegram channels — as listed by the cyber intelligence companies Unit 221B and Flashpoint — reveals a 21-year-old particular person who claims to reside in Brazil [full disclosure: Flashpoint is currently an advertiser on this blog].
Since late 2022, Forky’s posts have often promoted a DDoS mitigation firm and ISP that he operates referred to as botshield[.]io. The Botshield web site is related to a enterprise entity registered within the United Kingdom referred to as Botshield LTD, which lists a 21-year-old girl from Sao Paulo, Brazil because the director. Internet routing data point out Botshield (AS213613) at present controls a number of hundred Internet addresses that have been allotted to the corporate earlier this 12 months.
Domaintools.com reviews that botshield[.]io was registered in July 2022 to a Kaike Southier Leite in Sao Paulo. A LinkedIn profile by the identical identify says this particular person is a community specialist from Brazil who works in “the planning and implementation of robust network infrastructures, with a focus on security, DDoS mitigation, colocation and cloud server services.”
MEET FORKY

Image: Jaclyn Vernace / Shutterstock.com.
In his posts to public Telegram chat channels, Forky has hardly tried to hide his whereabouts or id. In numerous chat conversations listed by Unit 221B, Forky may very well be seen speaking about on a regular basis life in Brazil, typically remarking on the extraordinarily low or excessive costs in Brazil for a spread of products, from laptop and networking gear to narcotics and meals.
Reached through Telegram, Forky claimed he was “not involved in this type of illegal actions for years now,” and that the venture had been taken over by different unspecified builders. Forky initially informed KrebsOnSecurity he had been out of the botnet scene for years, solely to concede this wasn’t true when offered with public posts on Telegram from late final 12 months that clearly confirmed in any other case.
Forky denied being concerned within the assault on KrebsOnSecurity, however acknowledged that he helped to develop and market the Aisuru botnet. Forky claims he’s now merely a workers member for the Aisuru botnet workforce, and that he stopped operating the botnet roughly two months in the past after beginning a household. Forky additionally mentioned the lady named as director of Botshield is said to him.
Forky provided equivocal, evasive responses to quite a lot of questions concerning the Aisuru botnet and his enterprise endeavors. But on one level he was crystal clear:
“I have zero fear about you, the FBI, or Interpol,” Forky mentioned, asserting that he’s now virtually completely targeted on their internet hosting enterprise — Botshield.
Forky declined to debate the make-up of his ISP’s clientele, or to make clear whether or not Botshield was extra of a internet hosting supplier or a DDoS mitigation agency. However, Forky has posted on Telegram about Botshield efficiently mitigating giant DDoS assaults launched towards different DDoS-for-hire companies.
DomainTools finds the identical Sao Paulo road deal with within the registration data for botshield[.]io was used to register a number of different domains, together with cant-mitigate[.]us. The e mail deal with within the WHOIS data for that area is forkcontato@gmail.com, which DomainTools says was used to register the area for the now-defunct DDoS-for-hire service stresser[.]us, one of many domains seized in the FBI’s 2023 crackdown.
On May 8, 2023, the U.S. Department of Justice introduced the seizure of stresser[.]us, together with a dozen different domains providing DDoS companies. The DOJ mentioned ten of the 13 domains have been reincarnations of companies that have been seized throughout a prior sweep in December, which focused 48 high stresser companies (also referred to as “booters”).
Forky claimed he may discover out who attacked my web site with Aisuru. But when pressed a day in a while the query, Forky mentioned he’d come up empty-handed.
“I tried to ask around, all the big guys are not retarded enough to attack you,” Forky defined in an interview on Telegram. “I didn’t have anything to do with it. But you are welcome to write the story and try to put the blame on me.”
THE GHOST OF MIRAI
The 6.3 Tbps assault final week induced no seen disruption to this web site, partially as a result of it was so temporary — lasting roughly 45 seconds. DDoS assaults of such magnitude and brevity usually are produced when botnet operators want to take a look at or display their firepower for the advantage of potential patrons. Indeed, Google’s Menscher mentioned it’s possible that each the May 12 assault and the marginally bigger 6.5 Tbps assault towards Cloudflare final month have been merely assessments of the identical botnet’s capabilities.
In some ways, the risk posed by the Aisuru/Airashi botnet is paying homage to Mirai, an progressive IoT malware pressure that emerged in the summertime of 2016 and efficiently out-competed just about all different IoT malware strains in existence on the time.
As first revealed by KrebsOnSecurity in January 2017, the Mirai authors have been two U.S. males who co-ran a DDoS mitigation service — whilst they have been promoting much more profitable DDoS-for-hire companies utilizing essentially the most highly effective botnet on the planet.
Less than per week after the Mirai botnet was utilized in a days-long DDoS towards KrebsOnSecurity, the Mirai authors revealed the supply code to their botnet in order that they might not be the one ones in possession of it within the occasion of their arrest by federal investigators.
Ironically, the leaking of the Mirai supply is exactly what led to the eventual unmasking and arrest of the Mirai authors, who went on to serve probation sentences that required them to seek the advice of with FBI investigators on DDoS investigations. But that leak additionally quickly led to the creation of dozens of Mirai botnet clones, a lot of which have been harnessed to gas their very own highly effective DDoS-for-hire companies.
Menscher informed KrebsOnSecurity that as counterintuitive as it might sound, the Internet as an entire would most likely be higher off if the supply code for Aisuru turned public information. After all, he mentioned, the individuals behind Aisuru are in fixed competitors with different IoT botnet operators who’re all striving to commandeer a finite variety of susceptible IoT units globally.
Such a improvement would virtually definitely trigger a proliferation of Aisuru botnet clones, he mentioned, however not less than then the general firepower from every particular person botnet could be significantly diminished — or not less than inside vary of the mitigation capabilities of most DDoS safety suppliers.
Barring a supply code leak, Menscher mentioned, it will be good if somebody revealed the total listing of software program exploits being utilized by the Aisuru operators to develop their botnet so shortly.
“Part of the reason Mirai was so dangerous was that it effectively took out competing botnets,” he mentioned. “This attack somehow managed to compromise all these boxes that nobody else knows about. Ideally, we’d want to see that fragmented out, so that no [individual botnet operator] controls too much.”
[ad_2]