Operating in ‘kernel-space’ – essentially the most privileged layer of an working system, with direct entry to reminiscence, {hardware}, useful resource administration, and storage – is vitally necessary for safety merchandise. It permits them to observe ‘user-space’ – the non-privileged atmosphere the place functions run – and defend in opposition to malware that executes in that atmosphere, even when it tries to evade detection. But kernel entry additionally permits safety merchandise to counter extra insidious threats throughout the kernel itself. As we’ve reported beforehand, for instance, some risk actors use BYOVD (Bring Your Own Vulnerable Driver) assaults, or try and get their very own malicious drivers cryptographically signed, in an effort to entry kernel-space and benefit from that elevated degree of entry.
However, from a safety standpoint, working in kernel-space comes with its personal dangers. A incorrect step on this atmosphere – equivalent to a nasty replace to a kernel driver – could cause outages. If the driving force in query begins at boot time, when the working system first hundreds, that may result in extended impacts, doubtlessly requiring affected hosts to be began in a restoration mode to mitigate the issue and permit the machines besides usually.
Sophos’ Intercept X Advanced product makes use of 5 kernel drivers as of launch 2024.2. All drivers are extensively examined* with relevant flags enabled and disabled, and shipped with new flags disabled. (Sophos Intercept X and Sophos Central use function flags to progressively allow new options. Feature flags are deployed by Sophos Central. New options are sometimes ‘guarded’ by function flags – turned off until the flag is enabled – in order that the function might be rolled out progressively and doubtlessly revised earlier than wider enablement.)
In this text, within the pursuits of transparency, we’ll discover what these drivers are, what they do, after they begin, how they’re signed, and what their inputs are. We’ll additionally discover a few of the safeguards we put in place round these drivers to attenuate the chance of disruption (equivalent to staged rollouts, as talked about above; we offer an instance of this later within the article), and the choices accessible to prospects in terms of configuring them. It’s additionally value noting that Intercept X Advanced and all its elements, together with the kernel drivers, has been a part of an exterior bug bounty program since December 14, 2017; we welcome scrutiny through exterior bug bounty submissions, and we foster a tradition of collaboration with the analysis neighborhood.
* ‘Testing’ refers to a spread of inner testing, together with Microsoft-provided instruments and verifiers
The following desk gives an at-a-glance overview of the 5 kernel drivers that are a part of Intercept X Advanced launch 2024.2.
| Driver | Version | Type | Start Type | Signed By Microsoft? | Signature | Description |
| SophosEL.sys | 3.2.0.1150
|
Kernel Driver | Early-Launch Boot Start | Yes | ELAMP* | Sophos ELAM driver: can forestall execution of malicious boot begin drivers |
| SophosED.sys | 3.3.0.1727
|
File System Driver | Boot Start | Yes | WHCP+ | The important Sophos anti-malware driver |
| Sntp.sys | 1.15.1121
|
Network Filter Driver | System Start | Yes | WHCP+ | Sophos Network Threat Protection driver |
| Hmpalert.sys | 3.9.4.990
|
File System Driver | System Start
|
Yes | WHCP+ | Sophos HitmanPro.Alert driver |
| SophosZtnaTap.sys | 9.24.6.3
|
Network Filter Driver | On Demand | Yes | WHCP+ | Sophos Zero Trust Network Access (ZTNA) Tap driver |
Table 1: An overview of the kernel drivers in Intercept X Advanced2024.2
* Microsoft Windows Early Launch Anti-malware Publisher
+ Microsoft Windows Hardware Compatibility Publisher
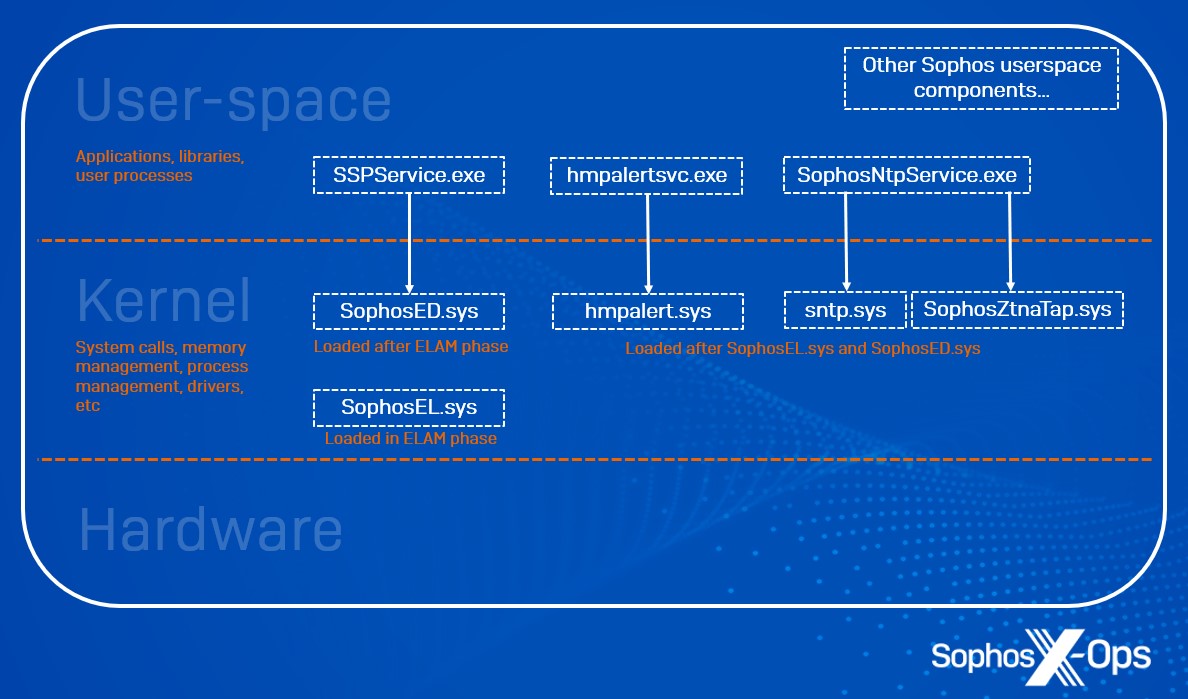
Figure 1: A conceptual depiction of user-space/kernel boundaries and the place Intercept X Advanced elements function
What it does: SophosEL.sys is the Sophos Early Launch Anti-Malware (ELAM) driver.
Inputs: This driver has one enter – a blocklist of known-bad drivers which should be prevented from executing as boot begin drivers at machine startup. This blocklist, situated on the registry key under, is ready by Sophos user-space risk detection logic when it detects a malicious driver. At the following boot cycle, SophosEL.sys ensures that this driver just isn’t loaded.
| Input | Description | Protection |
| HKLMSYSTEMCurrentControlSetServicesSophos ELAMConfig | Blocklist of known-bad drivers | DACLs; Sophos Tamper Protected |
Customer choices: Customers can configure remediation and allowed gadgets within the Threat Protection coverage from Sophos Central.
Additional measures: Any Microsoft or Sophos-signed driver is exempt from cleanup/blocking.
What it does: SophosED.sys (Endpoint Defense) is a boot begin driver, began throughout ELAM processing and earlier than many different kernel drivers are loaded, Windows user-space is initialized, and the system drive is mounted. It has three broad tasks:
- Providing tamper safety for the Sophos set up and configuration
- Exposing system exercise occasions to Sophos user-space elements for cover and detection
- Recording low-level system exercise occasions to the Sophos Event Journals for after-the-fact forensics and evaluation
Inputs: Since SophosED.sys begins earlier than the filesystem is accessible, its whole configuration is supplied by its service key. Note that each one the under inputs are below HKLMSYSTEMCurrentControlSetServicesSophos Endpoint Defense.
Filter driver altitudes inputs
SophosED.sys registers with Windows as a Mini-Filter driver at a number of altitudes (a novel identifier that defines a driver’s place on the ‘stack’ of drivers, with ‘lower’ drivers being nearer to reveal steel) allotted and authorized by Microsoft.
| Input | Description | Protection |
| HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseInstances | Multiple altitudes allotted by Microsoft | DACLs; Sophos Tamper Protected |
Tamper Protection inputs
Sophos Tamper Protection is configured by a mix of buyer insurance policies, Sophos function flags, and signed manifests constructed into the agent.
| Input | Description | Protection |
| HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseTamperProtectionConfig | Customer coverage (On/Off, configuration password*) | DACLs; Sophos Tamper Protected |
| HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseTamperProtectionElements
HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseTamperProtectionProviders |
Manifest of protected keys, folders, companies and many others | Signed; verified by driver earlier than loading |
* The configuration password is hashed with PBKDF2-SHA512 and a salt
System Activity Events inputs
The Sophos Central Threat Protection coverage helps a number of configuration choices, which Sophos user-space processes write to the SophosED.sys registry key, in order that they’re accessible when the driving force is loaded.
| Input | Description | Protection |
| HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseScanningConfig | Customer coverage (On/Off, exclusions, and plenty extra) | DACLs; Sophos Tamper Protected |
| HKLMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseEndpointFlags | Sophos function flags (numerous) | DACLs; Sophos Tamper Protected |
Event Journal inputs
| Input | Description | Protection |
| HLKMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseEventJournalConfig | Customer coverage (exclusions, disk limits) | DACLs; Sophos Tamper Protected |
| HLKMSYSTEMCurrentControlSetServicesSophos Endpoint DefenseEventJournalFeatures | If a subkey exists with a DWORD worth Enabled =1, occasion journals are enabled | DACLs; Sophos Tamper Protected |
Customer choices: Customers can configure disk limits and handle exclusions in Sophos Central Threat Protection coverage.
Additional measures: If a driver facility is accessible (based mostly on a mix of Customer Policy plus Sophos flag), then Sophos user-space processes can configure numerous parameters at runtime:
- A bitmask of mitigations to use per-process
- What occasions to allow or disable for every course of
- The period of time the driving force ought to anticipate a response from user-space (or whether or not it must be an asynchronous notification).
What it does: Sntp.sys (Sophos Network Threat Protection) is a kernel driver that registers for numerous Windows Filtering Platform occasions to intercept and doubtlessly modify community stream information. Depending on options enabled by Sophos Central Threat Protection and Web Control insurance policies, completely different filters and callouts are registered.
Inputs: Feature configuration is communicated to the driving force from a number of of the next consumer mode processes:
- SophosNtpService.exe
- SophosInternetFilter.exe
- SophosIPS.exe
- SSPService.exe
User-space processes talk with the driving force through the Windows Driver Framework, utilizing IOCTLs, Read, and Write. Communications to and from the driving force are protected, solely accepting connections from approved and genuine Sophos processes.
Customer choices: The filter driver intercepts community site visitors by browser and non-browser processes based mostly on the insurance policies outlined in Sophos Central. Processing of the intercepted site visitors is carried out in user-space by SophosInternetFilter.exe and SophosIPS.exe, which can ship modified content material again to the driving force (for instance, to show a block web page for malicious content material).
Additional measures: Customers can add particular person websites to their enable or block checklist in Sophos Central.
What it does: Hmpalert.sys enforces Sophos CryptoGuard, which detects and prevents bulk encryption of recordsdata by ransomware. It additionally configures what exploit mitigations are enforced as processes are executed.
Inputs: Hmpalert.sys has a lot of inputs, together with a number of registry subkeys and IOCTLS.
| Input | Description | Protection |
| HKLMSYSTEMCurrentControlSetServiceshmpalert | Software configuration | DACLs; Sophos Tamper Protected |
| HKLM SYSTEMCurrentControlSetServiceshmpalertConfig | Customer coverage | DACLs; Sophos Tamper Protected |
| HKLM SYSTEMCurrentControlSetServicesSophos Endpoint DefenseEndpointFlags | Sophos function flags (numerous) | DACLs; Sophos Tamper Protected |
Customer choices: Customers can allow/disable exploit mitigations and handle exclusions in Sophos Central Threat Protection coverage.
Additional measures: N/A
What it does: SophosZtnaTap.sys is a Sophos-built OpenVPN TAP driver. If the client deploys the Sophos Zero Trust Network Access (ZTNA) agent, the driving force intercepts DNS lookups for managed functions, and redirects site visitors for these functions to the relevant Sophos ZTNA gateways. ZTNA functions and gateways are configured by Sophos Central insurance policies and saved within the registry.
Inputs: Inputs into SophosZtnaTap.sys are through a registry subkey.
| Input | Description | Protection |
| HKLMSOFTWARESophosManagementPolicyNetworkPerimeter | Customer coverage (ZTNA Applications, Gateways, and certificates) | DACLs; Sophos Tamper Protected |
Customer choices: Customers can handle their ZTNA-protected functions and gateways from Sophos Central.
Additional measures: N/A
Sophos CryptoGuard has protected in opposition to bulk encryption on everlasting disks for over a decade. Intercept X model 2024.1.1 launched a brand new function, CryptoGuard ExFAT, which extends this safety to ExFAT partitions (sometimes discovered on detachable USB drives).
CryptoGuard ExFAT growth and testing came about in September 2023 by March 2024. This function was guarded by the flag ‘hmpa.cryptoguard-exfat.available.’
Sophos Engineering ran the software program internally with the flag enabled (our ‘Dogfood release’) beginning March 22, 2024.
Intercept X model 2024.1.1 was launched to Sophos, then to prospects utilizing our gradual software program deployment course of, between May 21, 2024 by June 6, 2024. At this stage the function was nonetheless dormant for everybody other than Sophos engineers.
The ’hmpa.cryptoguard-exfat.accessible’ flag was enabled utilizing our gradual flag enablement course of, between June 10, 2024 by June 26, 2024.
Customers can choose a hard and fast software program model (Endpoint Software Management: Fixed-term assist, Long-term assist). This locks the software program and flags till the client selects a unique software program bundle. Customers who use the ‘Sophos recommended’ choice obtain new software program periodically. Aside from software program rollouts, additionally they obtain gradual feature-flag enablements for brand new options within the software program, as with a standard software program launch. Sophos has developed this course of to enhance stability and keep away from enabling new occasions globally for all prospects.
Kernel drivers are elementary to the Intercept X Advanced product – and to sturdy Windows endpoint safety, usually – however we additionally acknowledge that working in kernel-space just isn’t with out its dangers.
In this text, we’ve walked by the kernel drivers in Intercept X Advanced (as of launch 2024.02), what they do, how they’re signed, what their inputs are, the management prospects have over their administration, and extra safeguards we’ve put in place – together with gradual, phased rollouts of latest options, and exemptions to attenuate the chance of disruption.
While no safeguard can ever remove threat altogether, we wished to share the main points of our drivers within the pursuits of transparency, and to clarify in depth how we strategy the complicated downside of making an attempt to guard our prospects from threats, in as secure a way as attainable.