There are two major methods to get better encrypted knowledge in a ransomware assault: restoring from backups and paying the ransom. Compromising a company’s backups permits adversaries to limit their sufferer’s skill to get better encrypted knowledge and dial-up the strain to pay the ransom.
This evaluation explores the influence of backup compromise on the enterprise and operational outcomes of a ransomware assault. It additionally shines gentle on the frequency of profitable backup compromise throughout a variety of industries.
The findings are based mostly on a vendor-agnostic survey commissioned by Sophos of two,974 IT/cybersecurity professionals whose organizations had been hit by ransomware within the final 12 months. Conducted by unbiased analysis company Vanson Bourne in early 2024, the examine displays respondents’ experiences over the earlier 12 months.
Executive abstract
The evaluation makes clear that monetary and operational implications of getting backups compromised in a ransomware assault are immense. When attackers reach compromising backups, a company is sort of twice as prone to pay the ransom and incurs an general restoration invoice that’s eight occasions increased than for these whose backups are usually not impacted.
Detecting and stopping malicious actors earlier than your backups are compromised lets you cut back significantly the influence of a ransomware assault in your group. Investing in stopping backup compromise each elevates your ransomware resilience whereas additionally reducing the general Total Cost of Ownership (TCO) of cybersecurity.
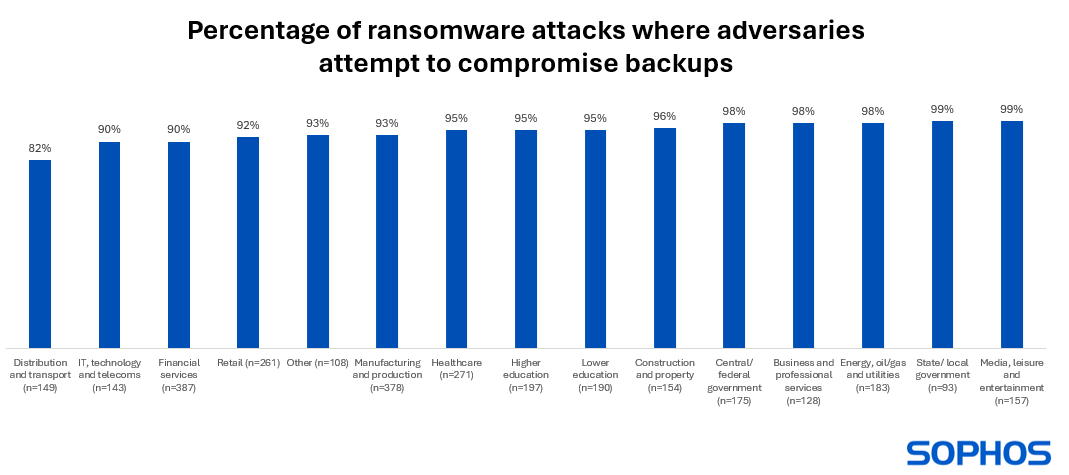
Learning 1: Ransomware actors virtually at all times try to compromise your backups
94% of organizations hit by ransomware up to now 12 months mentioned that the cybercriminals tried to compromise their backups in the course of the assault. This rose to 99% in each state and native authorities, and the media, leisure and leisure sector. The lowest price of tried compromise was reported by distribution and transport, nonetheless even right here greater than eight in ten (82%) organizations hit by ransomware mentioned the attackers tried to entry their backups.
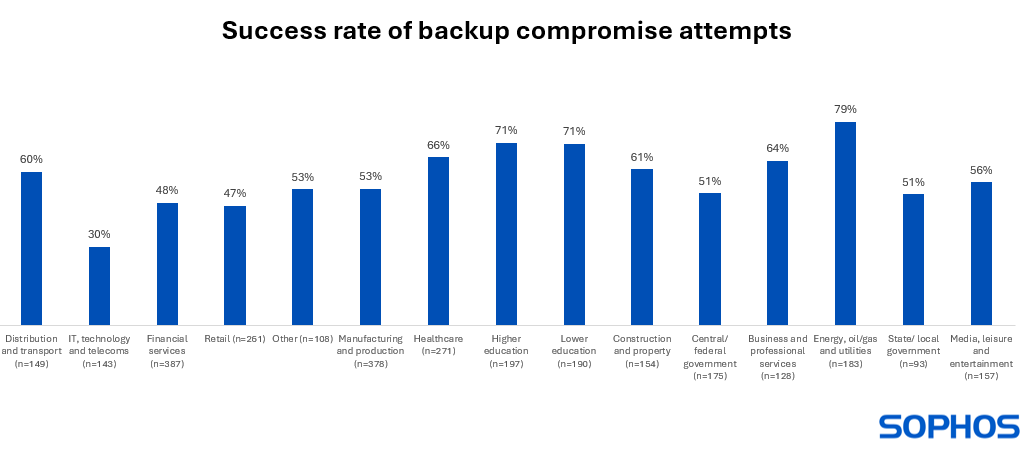
Learning 2: Backup compromise success price varies tremendously by business
Across all sectors, 57% of backup compromise makes an attempt have been profitable, that means that adversaries have been in a position to influence the ransomware restoration operations of over half of their victims. Interestingly, the evaluation revealed appreciable variation in adversary success price by sector:
- Attackers have been more than likely to efficiently compromise their victims’ backups within the vitality, oil/gasoline, and utilities (79% success price) and schooling (71% success price) sectors
- Conversely, IT, know-how and telecoms (30% success price) and retail (47% success price) reported the bottom charges of profitable backup compromise
There are a number of potential causes behind the differing success charges. It could also be that IT, telecoms and know-how had stronger backup safety in place to start out with so was higher ready to withstand the assault. They may additionally be simpler at detecting and stopping tried compromise earlier than the attackers may succeed. Conversely, the vitality, oil/gasoline and utilities sector might have skilled the next proportion of very superior assaults. Whatever the trigger, the influence may be appreciable.
Learning 3: Ransom calls for and funds double when backups are compromised
Data encryption
Organizations whose backups have been compromised have been 63% extra prone to have knowledge encrypted than those who didn’t: 85% of organizations with compromised backups mentioned that the attackers have been in a position to encrypt their knowledge in contrast with 52% of these whose backups weren’t impacted. The increased encryption price could also be indicative of weaker general cyber resilience which leaves organizations much less in a position to defend towards all phases of the ransomware assault.
Ransom demand
Victims whose backups have been compromised obtained ransom calls for that have been, on common, greater than double that of these whose backups weren’t impacted, with the median ransom calls for coming in at $2.3M (backups compromised) and $1M (backups not compromised) respectively. It is probably going that adversaries really feel that they’re in a stronger place in the event that they compromise backups and so are in a position to demand the next fee.
Ransom fee price
Organizations whose backups have been compromised have been virtually twice as prone to pay the ransom to get better encrypted knowledge than these whose backups weren’t impacted (67% vs. 36%).
Ransom fee quantity
The median ransom fee by organizations whose backups have been compromised was $2M, virtually double that of these whose backups remained intact ($1.062M). They have been additionally much less in a position to negotiate down the ransom fee, with these whose backups have been compromised paying, on common, 98% of the sum demanded. Those whose backups weren’t compromised have been in a position to cut back the fee to 82% of the demand.
Learning 4: Ransomware restoration prices are 8X increased when backups are compromised
Not all ransomware assaults lead to a ransom being paid. Even after they do, ransom funds are simply a part of the general restoration prices when coping with a ransomware assault. Ransomware-led outages ceaselessly have a substantial influence on day-to-day enterprise transactions whereas the duty of restoring IT programs is usually advanced and costly.
The median general ransomware restoration prices for organizations whose backups have been compromised ($3M) got here in eight occasions increased than that of organizations whose backups weren’t impacted ($375K). There are doubtless a number of causes behind this distinction, not least the extra work that’s usually wanted to revive from decrypted knowledge somewhat than well-prepared backups. It may additionally be that weaker backup safety is indicative of much less strong defenses and higher ensuing rebuilding work wanted.
Those whose backups have been compromised additionally skilled significantly longer restoration time with simply 26% totally recovered inside every week in contrast with 46% of these whose backups weren’t impacted.
Recommendations
Backups are a key a part of a holistic cyber threat discount technique. If your backups are accessible on-line, it is best to assume that adversaries will discover them. Organizations could be smart to:
- Take common backups and retailer in a number of areas. Be certain so as to add MFA (multi-factor authentication) to your cloud backup accounts to assist stop attackers from gaining entry.
- Practice recovering from backups. The extra fluent you’re within the restoration course of, the faster and simpler it will likely be to get better from an assault.
- Secure your backups. Monitor for and reply to suspicious exercise round your backups as it might be an indicator that adversaries try to compromise them.
How Sophos can assist
Sophos MDR: Over 500 specialists monitoring and defending your group
Sophos MDR is a 24/7 expert-led managed detection and response service that makes a speciality of stopping superior assaults that know-how alone can’t stop. It extends your IT/safety workforce with over 500 specialists who monitor your atmosphere, detecting, investigating, and responding to suspicious actions and alerts.
Sophos MDR analysts leverage telemetry from the safety instruments you already use – together with your backup and restoration resolution – to detect and neutralize assaults earlier than injury is completed. With a mean risk response time of simply 38 minutes, Sophos MDR works sooner than your subsequent risk.
Sophos XDR: Enabling IT groups to detect and reply to assaults
In-house groups can use Sophos XDR to get the visibility, insights, and instruments they should detect, examine, and reply to multi-stage threats, throughout all key assault vectors, within the shortest time. With Sophos XDR you’ll be able to leverage telemetry out of your backup and restoration resolution, in addition to your wider safety stack, to shortly see and reply to assaults.