Social networks are continually battling inauthentic bot accounts that ship direct messages to customers selling rip-off cryptocurrency funding platforms. What follows is an interview with a Russian hacker chargeable for a collection of aggressive crypto spam campaigns that lately prompted a number of massive Mastodon communities to briefly halt new registrations. According to the hacker, their spam software program has been in personal use till the previous couple of weeks, when it was launched as open supply code.

Renaud Chaput is a contract programmer engaged on modernizing and scaling the Mastodon undertaking infrastructure — together with joinmastodon.org, mastodon.on-line, and mastodon.social. Chaput stated that on May 4, 2023, somebody unleashed a spam torrent concentrating on customers on these Mastodon communities through “private mentions,” a sort of direct messaging on the platform.
The messages stated recipients had earned an funding credit score at a cryptocurrency buying and selling platform referred to as moonxtrade[.]com. Chaput stated the spammers used greater than 1,500 Internet addresses throughout 400 suppliers to register new accounts, which then adopted standard accounts on Mastodon and despatched personal mentions to the followers of these accounts.
Since then, the identical spammers have used this technique to promote greater than 100 totally different crypto investment-themed domains. Chaput stated that at one level final week the quantity of bot accounts being registered for the crypto spam marketing campaign began overwhelming the servers that deal with new signups at Mastodon.social.
“We suddenly went from like three registrations per minute to 900 a minute,” Chaput stated. “There was nothing in the Mastodon software to detect that activity, and the protocol is not designed to handle this.”

One of the crypto funding rip-off messages promoted within the spam campaigns on Mastodon this month.
Seeking to achieve a brief deal with on the spam wave, Chaput stated he briefly disabled new account registrations on mastodon.social and mastondon.on-line. Shortly after that, those self same servers got here below a sustained distributed denial-of-service (DDoS) assault.
Chaput stated whoever was behind the DDoS was undoubtedly not utilizing point-and-click DDoS instruments, like a booter or stresser service.
“This was three hours non-stop, 200,000 to 400,000 requests per second,” Chaput stated of the DDoS. “At first, they were targeting one path, and when we blocked that they started to randomize things. Over three hours the attack evolved several times.”
Chaput says the spam waves have died down since they retrofitted mastodon.social with a CAPTCHA, these squiggly letter and quantity mixtures designed to stymie automated account creation instruments. But he’s anxious that different Mastodon situations might not be as well-staffed and may be simple prey for these spammers.
“We don’t know if this is the work of one person, or if this is [related to] software or services being sold to others,” Chaput instructed KrebsOnSecurity. “We’re really impressed by the scale of it — using hundreds of domains and thousands of Microsoft email addresses.”
Chaput stated a evaluate of their logs signifies most of the newly registered Mastodon spam accounts had been registered utilizing the identical 0auth credentials, and {that a} area widespread to these credentials was quot[.]pw.
A DIRECT QUOT
The area quot[.]pw has been registered and deserted by a number of events since 2014, however the latest registration knowledge obtainable via DomainTools.com exhibits it was registered in March 2020 to somebody in Krasnodar, Russia with the e-mail tackle edgard011012@gmail.com.
This electronic mail tackle can also be related to accounts on a number of Russian cybercrime boards, together with “__edman__,” who had a historical past of promoting “logs” — massive quantities of knowledge stolen from many bot-infected computer systems — in addition to making a gift of entry to hacked Internet of Things (IoT) units.
In September 2018, a person by the identify “ципа” (phonetically “Zipper” in Russian) registered on the Russian hacking discussion board Lolzteam utilizing the edgard0111012@gmail.com tackle. In May 2020, Zipper instructed one other Lolzteam member that quot[.]pw was their area. That person marketed a service referred to as “Quot Project” which stated they might be employed to write down programming scripts in Python and C++.
“I make Telegram bots and other rubbish cheaply,” reads one February 2020 gross sales thread from Zipper.
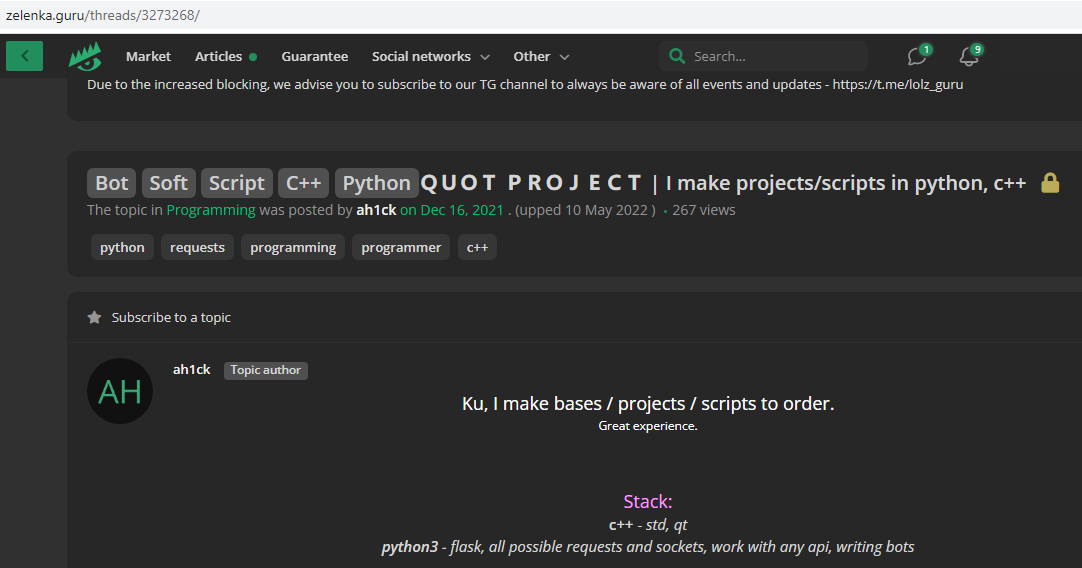
Quotpw/Ahick/Edgard/ципа promoting his coding providers on this Google-translated discussion board posting.
Clicking the “open chat in Telegram” button on Zipper’s Lolzteam profile web page launched a Telegram prompt message chat window the place the person Quotpw responded nearly instantly. Asked in the event that they had been conscious their area was getting used to handle a spam botnet that was pelting Mastodon situations with crypto rip-off spam, Quotpw confirmed the spam was powered by their software program.
“It was made for a limited circle of people,” Quotpw stated, noting that they lately launched the bot software program as open supply on GitHub.
Quotpw went on to say the spam botnet was powered by effectively greater than the a whole bunch of IP addresses tracked by Chaput, and that these techniques had been principally residential proxies. A residential proxy typically refers to a pc or cellular system operating some sort of software program that permits the system for use as a pass-through for Internet site visitors from others.
Very usually, this proxy software program is put in surreptitiously, akin to via a “Free VPN” service or cellular app. Residential proxies can also check with households protected by compromised residence routers operating factory-default credentials or outdated firmware.
Quotpw maintains they’ve earned greater than $2,000 sending roughly 100,000 personal mentions to customers of various Mastodon communities over the previous few weeks. Quotpw stated their conversion charge for a similar bot-powered direct message spam on Twitter is normally a lot larger and extra worthwhile, though they conceded that current changes to Twitter’s anti-bot CAPTCHA have put a crimp of their Twitter earnings.
“My partners (I’m programmer) lost time and money while ArkoseLabs (funcaptcha) introduced new precautions on Twitter,” Quotpw wrote in a Telegram reply. “On Twitter, more spam and crypto scam.”
Asked whether or not they felt in any respect conflicted about spamming individuals with invites to cryptocurrency scams, Quotpw stated of their hometown “they pay more for such work than in ‘white’ jobs” — referring to legit programming jobs that don’t contain malware, botnets, spams and scams.
“Consider salaries in Russia,” Quotpw stated. “Any spam is made for profit and brings illegal money to spammers.”
THE VIENNA CONNECTION
Shortly after edgard011012@gmail.com registered quot[.]pw, the WHOIS registration data for the area had been modified once more, to msr-sergey2015@yandex.ru, and to a cellphone quantity in Austria: +43.6607003748.
Constella Intelligence, an organization that tracks breached knowledge, finds that the tackle msr-sergey2015@yandex.ru has been related to accounts on the cellular app website aptoide.com (person: CoolappsforAndroid) and vimeworld.ru that had been created from totally different Internet addresses in Vienna, Austria.
A search in Skype on that Austrian cellphone quantity exhibits it belongs to a Sergey Proshutinskiy who lists his location as Vienna, Austria. The very first outcome that comes up when one searches that uncommon identify in Google is a LinkedIn profile for a Sergey Proshutinskiy from Vienna, Austria.
Proshutinskiy’s LinkedIn profile says he’s a Class of 2024 pupil at TGM, which is a Christian mission college in Austria. His resume additionally says he’s an information science intern at Mondi Group, an Austrian producer of sustainable packaging and paper.
Mr. Proshutinskiy didn’t reply to requests for remark.
Quotpw denied being Sergey, and stated Sergey was a buddy who registered the area as a birthday current and favor final yr.
“Initially, I bought it for 300 rubles,” Quotpw defined. “The extension cost 1300 rubles (expensive). I waited until it expired and forgot to buy it. After that, a friend (Sergey) bought [the] domain and transferred access rights to me.”
“He’s not even an information security specialist,” Quotpw stated of Sergey. “My friends do not belong to this field. None of my friends are engaged in scams or other black [hat] activities.”
It could appear unlikely that somebody would go to all this bother to spam Mastodon customers over a number of weeks utilizing a powerful variety of assets — all for simply $2,000 in revenue. But it’s doubtless that whoever is definitely operating the assorted crypto rip-off platforms marketed by Quotpw’s spam messages pays handsomely for any investments generated by their spam.
According to the FBI, monetary losses from cryptocurrency funding scams dwarfed losses for all different forms of cybercrime in 2022, rising from $907 million in 2021 to $2.57 billion final yr.
