[ad_1]

Getty Images
Google has quietly resubmitted a disclosure of a essential code-execution vulnerability affecting hundreds of particular person apps and software program frameworks after its earlier submission left readers with the mistaken impression that the menace affected solely the Chrome browser.
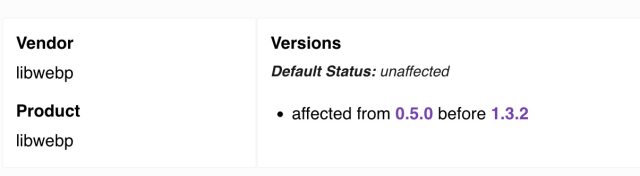
The vulnerability originates within the libwebp code library, which Google created in 2010 for rendering photographs in webp, a then new format that resulted in recordsdata that had been as much as 26 % smaller as in comparison with PNG photographs. Libwebp is included into nearly each app, working system, or different code library that renders webp photographs, most notably the Electron framework utilized in Chrome and plenty of different apps that run on each desktop and cell units.
Two weeks in the past, Google issued a safety advisory for what it stated was a heap buffer overflow in WebP in Chrome. Google’s formal description, tracked as CVE-2023-4863, scoped the affected vendor as “Google” and the software program affected as “Chrome,” though any code that used libwebp was weak. Critics warned that Google’s failure to notice that hundreds of different items of code had been additionally weak would lead to pointless delays in patching the vulnerability, which permits attackers to execute malicious code when customers do nothing greater than view a booby-trapped webp picture.
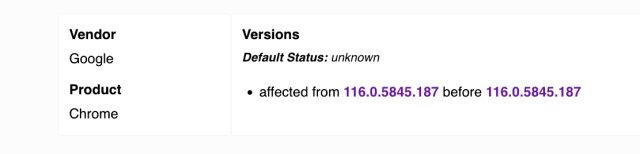
On Monday, Google submitted a brand new disclosure that’s tracked as CVE-2023-5129. The new entry appropriately lists libwebp because the affected vendor and affected software program. It additionally bumps up the severity score of the vulnerability, from 8.8 out of a doable 10 to 10.
The lack of completeness within the first CVE Google assigned goes effectively past being a mere educational failing. More than two weeks after the vulnerability got here to gentle, a bunch of software program stays unpatched. The most evident instance is Microsoft Teams.
The vulnerability description in Google’s new submission gives significantly extra element. The description within the previous submission was:
Heap buffer overflow in WebP in Google Chrome previous to 116.0.5845.187 allowed a distant attacker to carry out an out of bounds reminiscence write through a crafted HTML web page. (Chromium safety severity: Critical)
The new description is:
With a specifically crafted WebP lossless file, libwebp might write information out of bounds to the heap. The ReadHuffmanCodes() operate allocates the HuffmanCode buffer with a measurement that comes from an array of precomputed sizes: kTableSize. The color_cache_bits worth defines which measurement to make use of. The kTableSize array solely takes into consideration sizes for 8-bit first-level desk lookups however not second-level desk lookups. libwebp permits codes which can be as much as 15-bit (MAX_ALLOWED_CODE_LENGTH). When BuildHuffmanTable() makes an attempt to fill the second-level tables it might write information out-of-bounds. The OOB write to the undersized array occurs in ReplicateValue.
Whether it’s tracked as CVE-2023-4863 or CVE-2023-5129, the vulnerability within the libwebp is critical. Before utilizing apps, customers ought to be certain that the variations of Electron they use are v22.3.24, v24.8.3, or v25.8.1.
[ad_2]
