[ad_1]
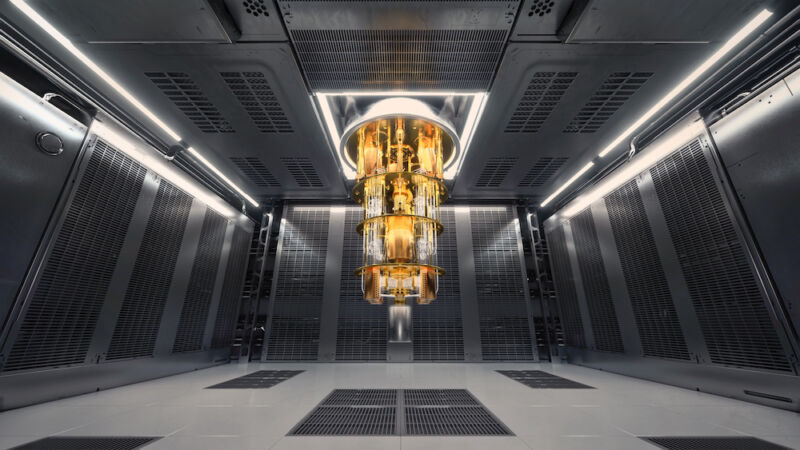
Getty Images
The FIDO2 business normal adopted 5 years in the past supplies probably the most safe recognized option to log in to web sites as a result of it doesn’t depend on passwords and has probably the most safe type of built-in two-factor authentication. Like many current safety schemes in the present day, although, FIDO faces an ominous if distant risk from quantum computing, which someday will trigger the at present rock-solid cryptography the usual makes use of to fully crumble.
Over the previous decade, mathematicians and engineers have scrambled to go off this cryptopocalypse with the arrival of PQC—quick for post-quantum cryptography—a category of encryption that makes use of algorithms proof against quantum-computing assaults. This week, researchers from Google introduced the launch of the primary implementation of quantum-resistant encryption to be used in the kind of safety keys which might be the fundamental constructing blocks of FIDO2.
The finest recognized implementation of FIDO2 is the passwordless type of authentication: passkeys. So far, there are not any recognized methods passkeys might be defeated in credential phishing assaults. Dozens of web sites and providers now permit customers to log in utilizing passkeys, which use cryptographic keys saved in safety keys, smartphones, and different gadgets.
“While quantum attacks are still in the distant future, deploying cryptography at Internet scale is a massive undertaking which is why doing it as early as possible is vital,” Elie Bursztein and Fabian Kaczmarczyck, cybersecurity and AI analysis director, and software program engineer, respectively, at Google wrote. “In particular, for security keys this process is expected to be gradual as users will have to acquire new ones once FIDO has standardized post-quantum cryptography resilient cryptography and this new standard is supported by major browser vendors.”
The path to PQC is fraught with dangers. RSA and different encryption algorithms have been in use for many years with no recognized methods for them to be damaged. Over the years, that monitor report has led to confidence that they’re secure to be used. PQC algorithms are of their infancy, and that has rightly led to concern that they’ll’t but be trusted. A living proof: a PQC algorithm referred to as SIKE. Last 12 months, after advancing as a fourth-round candidate in a program run by the US Department of Commerce’s National Institute of Standards and Technology, SIKE was fully and spectacularly damaged by a single classical laptop.
The PQC algorithm used within the implementation of FIDO2 safety keys takes a extra cautious strategy. It combines the elliptic curve digital signature algorithm—believed to be unbreakable by classical computing however simply damaged with quantum computing—with a PQC algorithm often called Crystals-Dilithium. Crystals-Dilithium is now considered one of three PQC algorithms chosen by NIST to be used with digital signatures.
The explicit Dilithium used within the lately launched digital key implementation seems to unravel quite a lot of issues. First, for it to be damaged, an attacker must defeat each the ECDSA encryption and the PCQ encryption that underpins its safety. And second, the keys it makes use of are tiny in comparison with many different PQC algorithms in circulation now. In this week’s put up, the Google researchers wrote:
Our proposed implementation depends on a hybrid strategy that mixes the battle examined ECDSA signature algorithm and the lately standardized quantum resistant signature algorithm, Dilithium. In collaboration with ETH, we developed this novel hybrid signature schema that provides one of the best of each worlds. Relying on a hybrid signature is essential because the safety of Dilithium and different lately standardized quantum resistant algorithms haven’t but stood the check of time and up to date assaults on Rainbow (one other quantum resilient algorithm) display the necessity for warning. This cautiousness is especially warranted for safety keys as most can’t be upgraded – though we’re working towards it for OpenSK. The hybrid strategy can be utilized in different post-quantum efforts like Chrome’s assist for TLS.
On the technical aspect, a big problem was to create a Dilithium implementation sufficiently small to run on safety keys’ constrained {hardware}. Through cautious optimization, we had been capable of develop a Rust reminiscence optimized implementation that solely required 20 KB of reminiscence, which was small enough sufficient. We additionally hung out making certain that our implementation signature velocity was effectively throughout the anticipated safety keys specification. That stated, we imagine bettering signature velocity additional by leveraging {hardware} acceleration would permit for keys to be extra responsive.
Moving ahead, we hope to see this implementation (or a variant of it), being standardized as a part of the FIDO2 key specification and supported by main net browsers in order that customers’ credentials might be protected towards quantum assaults. If you have an interest in testing this algorithm or contributing to safety key analysis, head to our open supply implementation OpenSK.
The safety of RSA and different conventional types of uneven encryption relies on mathematical issues which might be simple to confirm the reply to however arduous to calculate. RSA, for example, depends on the issue of factorizing prime numbers. Finding the primes for the quantity 27,919,645,564,169,759 is difficult, however as soon as somebody is informed the primes are 48,554,491 and 575,016,749 it takes a couple of seconds to confirm (due to Boot.dev for the instance).
A factorization methodology often called Shor’s algorithm makes it theoretically doable to unravel these kind of issues. That, in flip, means sure demise for lots of the cryptographic schemes now defending encrypted net classes, banking and medical knowledge, and different secrets and techniques. The solely factor holding again this doomsday situation is the large quantity of quantum computing assets required.
While classical computer systems can’t run Shor’s algorithm effectively sufficient to interrupt RSA keys in use in the present day, quantum computer systems with enough energy will be capable to clear up them in a matter of eight hours. No one is aware of when that day will come, although one skilled within the area stated lately it gained’t be in our lifetime. Still, because the Google researchers identified, adopting any PQC schemes shall be gradual, so it is smart to start work sooner somewhat than later.
[ad_2]
