[ad_1]
Authored by SangRyol Ryu and Yukihiro Okutomi
McAfee’s Mobile Research workforce lately analyzed new malware focusing on cellular fee customers in Japan. The malware which was distributed on the Google Play retailer pretends to be a professional cellular safety app, however it’s in reality a fee fraud malware stealing passwords and abusing reverse proxy focusing on the cellular fee companies. McAfee researchers notified Google of the malicious apps, スマホ安心セキュリティ, or ‘Smartphone Anshin Security’, package deal title ‘com.z.cloud.px.app’ and ‘com.z.px.appx’. The purposes are now not obtainable on Google Play. Google Play Protect has additionally taken steps to guard customers by disabling the apps and offering a warning. McAfee Mobile Security merchandise detect this risk as Android/ProxySpy.
How Do Victims Install This Malware?
The malware actor continues to publish malicious apps on the Google Play Store with numerous developer accounts. According to the data posted on Twitter by Yusuke Osumi, Security Researcher at Yahoo! Japan, the attacker sends SMS messages from abroad with a Google Play hyperlink to lure customers to put in the malware. To entice extra customers, the message entices customers to replace safety software program.
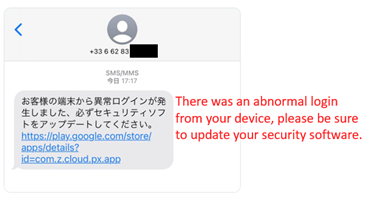
A SMS message from France (from Twitter publish by Yusuke)

Malware on Google Play
The Mobile Research workforce additionally discovered that the malware actor makes use of Google Drive to distribute the malware. In distinction to putting in an utility after downloading an APK file, Google Drive permits customers to put in APK recordsdata with out leaving any footprint and makes the set up course of less complicated. Once the person clicks the hyperlink, there are only some extra touches required to run the applying. Only three clicks are sufficient if customers have beforehand allowed the set up of unknown apps on Google Drive.
Following notification from McAfee researchers, Google has eliminated identified Google Drive recordsdata related to the malware hashes listed on this weblog publish.
What does this malware seem like?
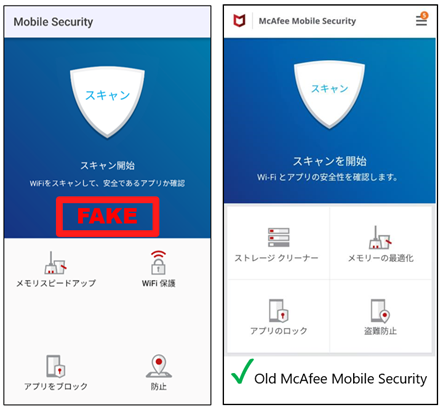
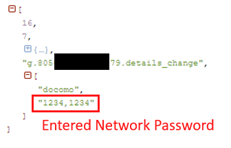
When a person installs and launches this malware, it asks for the Service password. Cleverly, the malware exhibits incorrect password messages to gather the extra exact passwords. Of course, it doesn’t matter whether or not the password is right or not. It is a approach of getting the Service password. The Service password is used for the fee service which gives simple on-line fees. The person can begin this fee service by setting a Service password. The cost might be paid together with the cell phone invoice. After the password exercise, the malware exhibits faux cellular safety display screen. Interestingly, the structure of the exercise is related to our previous McAfee Mobile Security. All buttons look real, however these are all faux.
The Network password is used for the NTT DOCOMO fee service which gives simple on-line funds. NTT DOCOMO cellular community customers can begin this fee service by simply setting 4-digits password known as a Network password. The cost might be paid together with the cell phone invoice. When it is advisable to pay on-line, you may merely do the fee course of by coming into the 4-digits password.
After the password exercise, the malware exhibits a faux cellular safety display screen. Interestingly, the structure of the exercise is just like our previous McAfee Mobile Security. All buttons look real, however these are all faux.
How does this malware work?
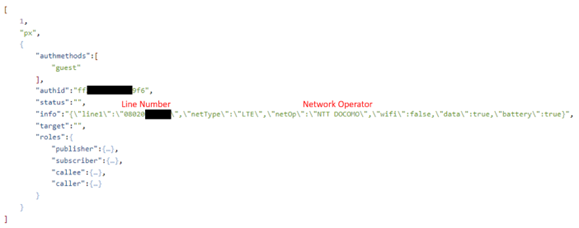
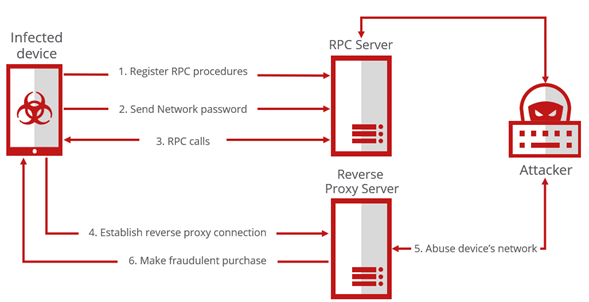
There is a local library named ‘libmyapp.so’ loaded throughout the app execution written in Golang. The library, when loaded, tries to hook up with the C2 server utilizing a Web Socket. Web Application Messaging Protocol (WAMP) is used to speak and course of Remote Procedure Calls (RPC). When the connection is made, the malware sends out community info together with the telephone quantity. Then, it registers the consumer’s process instructions described within the desk under. The internet socket connection is stored alive and takes the corresponding motion when the command is acquired from the server like an Agent. And the socket is used to ship the Service password out to the attacker when the person enters the Service password on the exercise.
| RPC Function title | Description |
| connect_to | Create reverse proxy and connect with distant server |
| disconnect | Disconnect the reverse proxy |
| get_status | Send the reverse proxy standing |
| get_info | Send line quantity, connection sort, operator, and so forth |
| toggle_wifi | Set the Wi-Fi ON/OFF |
| show_battery_opt | Show dialog to exclude battery optimization for background work |
Registered RPC capabilities description
To make a fraudulent buy by utilizing leaked info, the attacker wants to make use of the person’s community. The RPC command ‘toggle_wifi’ can change the connection state to Wi-Fi or mobile community, and ‘connect_to’ will present a reverse proxy to the attacker. A reverse proxy can permit connecting the host behind a NAT (Network Address Translation) or a firewall. Via the proxy, the attacker can ship buy requests by way of the person’s community.
Conclusion
It is an fascinating level that the malware makes use of a reverse proxy to steal the person’s community and implement an Agent service with WAMP. McAfee Mobile Research Team will proceed to search out this sort of risk and shield our prospects from cellular threats. It is recommended to be extra cautious when coming into a password or confidential info into untrusted purposes.
IoCs (Indicators of Compromise)
193[.]239[.]154[.]23
91[.]204[.]227[.]132
ruboq[.]com
| SHA256 | Package Name | Distribution |
| 5d29dd12faaafd40300752c584ee3c072d6fc9a7a98a357a145701aaa85950dd | com.z.cloud.px.app | Google Play |
| e133be729128ed6764471ee7d7c36f2ccb70edf789286cc3a834e689432fc9b0 | com.z.cloud.px.app | Other |
| e7948392903e4c8762771f12e2d6693bf3e2e091a0fc88e91b177a58614fef02 | com.z.px.appx | Google Play |
| 3971309ce4a3cfb3cdbf8abde19d46586f6e4d5fc9f54c562428b0e0428325ad | com.z.cloud.px.app2 | Other |
| 2ec2fb9e20b99f60a30aaa630b393d8277949c34043ebe994dd0ffc7176904a4 | com.jg.rc.papp | Google Drive |
| af0d2e5e2994a3edd87f6d0b9b9a85fb1c41d33edfd552fcc64b43c713cdd956 | com.de.rc.seee | Google Drive |
[ad_2]
