[ad_1]
Every day, private information, comparable to location info, photographs, or textual content queries are handed between your machine and distant, cloud-based companies. Your information is encrypted when in transit and at relaxation, however as potential assault vectors develop extra subtle, information should even be protected throughout use by the service, particularly for software program techniques that deal with personally identifiable person information.
Toward this aim, Google’s Project Oak is a analysis effort that depends on the confidential computing paradigm to construct an infrastructure for processing delicate person information in a safe and privacy-preserving method: we guarantee information is protected throughout transit, at relaxation, and whereas in use. As an assurance that the person information is actually protected, we’ve open sourced Project Oak code, and have launched a clear launch course of to present publicly inspectable proof that the appliance was constructed from that supply code.
This weblog submit introduces Oak’s clear launch course of, which depends on the SLSA framework to generate cryptographic proof of the origin of Oak’s confidential computing stack, and along with Oak’s distant attestation course of, permits customers to cryptographically confirm that their private information was processed by a reliable software in a safe setting.
Project Oak just lately collaborated with the SLSA neighborhood to create a brand new container-based builder that produces Supply-chain Levels for Software Artifacts (SLSA) Build Level 3 provenance. This new container-based builder generates non-forgeable provenance statements that seize particulars about construct course of info that enable customers to carry out automated, rigorous provenance verification.
With this enhanced provenance generated by the container-based builder, you possibly can reply questions like:
-
Was the artifact constructed with a toolchain that I do know and belief?
-
Was the artifact constructed with a command that I belief?
-
Did the construct command use a instrument that was affected by a vulnerability?
-
How can I recreate the artifact?
Project Oak is especially focused on answering these questions on each layer of the confidential computing stack. For occasion, to make sure that a launched binary was constructed utilizing a trusted construct course of (e.g., the construct command didn’t use any doubtlessly malicious instrument), the Oak launch course of compares the construct command towards a set of allow-listed tokens. Similarly, we will confirm that the builder was not tampered with.
Project Oak develops a safe runtime and a distant attestation protocol—methods to detect potential adversaries on distant servers and to guard workloads whereas they’re working. Now, with the addition of the container-based SLSA builder, we’re in a position to full our clear launch course of to guard towards software program provide chain assaults and supply an automatic course of for verifying the integrity and trustworthiness of a distant server, earlier than sending delicate info to it.
Specifically, for every launched model of the Oak safe runtime, the Oak group generates and indicators an endorsement assertion for the binary, utilizing a key accessible solely to the Oak group. The endorsement assertion can solely be generated if the provenance assertion passes verification checks, making certain {that a} potential malicious attacker can’t forge the assertion.
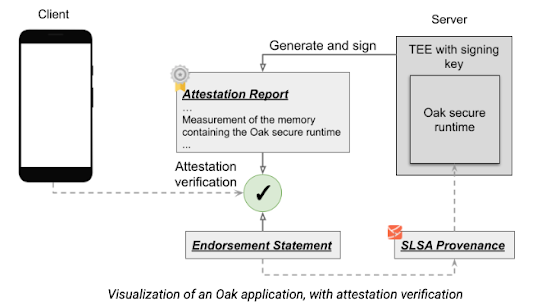
When the consumer establishes a connection to the server, the consumer should confirm the endorsement assertion and the proof of its inclusion in a transparency log, and examine that the binary identities within the attestation report and the endorsement assertion are the identical. This, along with signature verification for the endorsement assertion, ensures three essential factors of belief for the general course of: that the consumer is interacting with the identical publicly endorsed model of the Oak safe runtime that every one different purchasers work together with; the Oak safe runtime is open supply; and that it has a publicly printed non-forgeable SLSA v1.0 provenance with adherence to SLSA Build Track 3. For a extra technical rationalization of the method, see Project Oak’s clear launch course of.
Visualization of an Oak software, with attestation verification
We encourage you to take a look at the clear launch venture as a use case for SLSA. Please attain out to us through our slack channel to discover concepts associated to Oak safe runtimes and distant attestation.
You don’t want to make use of Project Oak to benefit from the brand new SLSA builder instrument. If your venture is open supply, strive one of many SLSA builders to generate non-forgeable provenance on your binaries. We encourage you to containerize your construct and check out the container-based SLSA 3 builder! Using a container picture on your builds improves the reproducibility of your binaries. We additionally suggest including the directions for constructing your container picture (e.g., a Dockerfile) to your GitHub repository, which improves auditability and transparency of your construct course of, and thus the safety of your software program provide chain.
[ad_2]