[ad_1]
Cybercriminals are promoting tons of of hundreds of credential units stolen with the assistance of a cracked model of Acunetix, a strong business net app vulnerability scanner, new analysis finds. The cracked software program is being resold as a cloud-based assault software by at the very least two completely different providers, one among which KrebsOnSecurity traced to an info know-how agency based mostly in Turkey.

Araneida Scanner.
Cyber risk analysts at Silent Push stated they lately obtained stories from a accomplice group that recognized an aggressive scanning effort towards their web site utilizing an Internet tackle beforehand related to a marketing campaign by FIN7, a infamous Russia-based hacking group.
But on nearer inspection they found the tackle contained an HTML title of “Araneida Customer Panel,” and located they may search on that textual content string to search out dozens of distinctive addresses internet hosting the identical service.
It quickly grew to become obvious that Araneida was being resold as a cloud-based service utilizing a cracked model of Acunetix, permitting paying clients to conduct offensive reconnaissance on potential goal web sites, scrape consumer information, and discover vulnerabilities for exploitation.
Silent Push additionally realized Araneida bundles its service with a sturdy proxy providing, in order that buyer scans seem to return from Internet addresses which can be randomly chosen from a big pool of obtainable visitors relays.
The makers of Acunetix, Texas-based utility safety vendor Invicti Security, confirmed Silent Push’s findings, saying somebody had discovered the way to crack the free trial model of the software program in order that it runs with out a legitimate license key.
“We have been playing cat and mouse for a while with these guys,” stated Matt Sciberras, chief info safety officer at Invicti.
Silent Push stated Araneida is being marketed by an eponymous consumer on a number of cybercrime boards. The service’s Telegram channel boasts almost 500 subscribers and explains the way to use the software for malicious functions.
In a “Fun Facts” listing posted to the channel in late September, Araneida stated their service was used to take over greater than 30,000 web sites in simply six months, and that one buyer used it to purchase a Porsche with the fee card information (“dumps”) they bought.
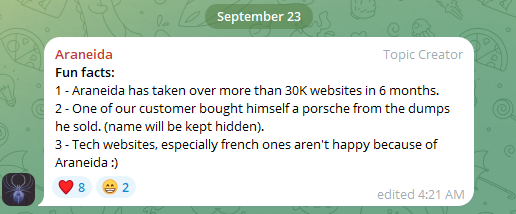
Araneida Scanner’s Telegram channel bragging about how clients are utilizing the service for cybercrime.
“They are constantly bragging with their community about the crimes that are being committed, how it’s making criminals money,” stated Zach Edwards, a senior risk researcher at Silent Push. “They are also selling bulk data and dumps which appear to have been acquired with this tool or due to vulnerabilities found with the tool.”
Silent Push additionally discovered a cracked model of Acunetix was powering at the very least 20 cases of the same cloud-based vulnerability testing service catering to Mandarin audio system, however they had been unable to search out any apparently associated gross sales threads about them on the darkish net.
Rumors of a cracked model of Acunetix being utilized by attackers surfaced in June 2023 on Twitter/X, when researchers first posited a connection between noticed scanning exercise and Araneida.
According to an August 2023 report (PDF) from the U.S. Department of Health and Human Services (HHS), Acunetix (presumably a cracked model) is amongst a number of instruments utilized by APT 41, a prolific Chinese state-sponsored hacking group.
THE TURKISH CONNECTION
Silent Push notes that the web site the place Araneida is being bought — araneida[.]co — first got here on-line in February 2023. But a evaluate of this Araneida nickname on the cybercrime boards reveals they’ve been lively within the prison hacking scene since at the very least 2018.
A search within the risk intelligence platform Intel 471 reveals a consumer by the identify Araneida promoted the scanner on two cybercrime boards since 2022, together with Breached and Nulled. In 2022, Araneida instructed fellow Breached members they could possibly be reached on Discord on the username “Ornie#9811.”
According to Intel 471, this similar Discord account was marketed in 2019 by an individual on the cybercrime discussion board Cracked who used the monikers “ORN” and “ori0n.” The consumer “ori0n” talked about in a number of posts that they could possibly be reached on Telegram on the username “@sirorny.”
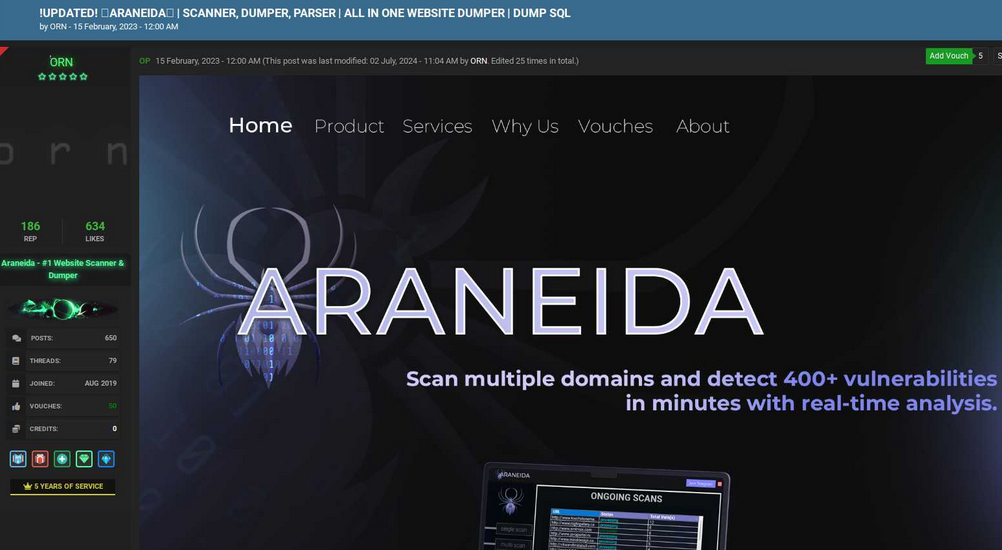
Orn promoting Araneida Scanner in Feb. 2023 on the discussion board Cracked. Image: Ke-la.com.
The Sirorny Telegram id additionally was referenced as some extent of contact for a present consumer on the cybercrime discussion board Nulled who’s promoting web site improvement providers, and who references araneida[.]co as one among their initiatives. That consumer, “Exorn,” has posts relationship again to August 2018.
In early 2020, Exorn promoted an internet site known as “orndorks[.]com,” which they described as a service for automating the scanning for web-based vulnerabilities. A passive DNS lookup on this area at DomainTools.com reveals that its e-mail information pointed to the tackle ori0nbusiness@protonmail.com.
Constella Intelligence, an organization that tracks info uncovered in information breaches, finds this e-mail tackle was used to register an account at Breachforums in July 2024 underneath the nickname “Ornie.” Constella additionally finds the identical e-mail registered on the web site netguard[.]codes in 2021 utilizing the password “ceza2003” [full disclosure: Constella is currently an advertiser on KrebsOnSecurity].
A search on the password ceza2003 in Constella finds roughly a dozen e-mail addresses that used it in an uncovered information breach, most of them that includes some variation on the identify “altugsara,” together with altugsara321@gmail.com. Constella additional finds altugsara321@gmail.com was used to create an account on the cybercrime neighborhood RaidForums underneath the username “ori0n,” from an Internet tackle in Istanbul.
According to DomainTools, altugsara321@gmail.com was utilized in 2020 to register the area identify altugsara[.]com. Archive.org’s historical past for that area reveals that in 2021 it featured an internet site for a then 18-year-old Altuğ Şara from Ankara, Turkey.
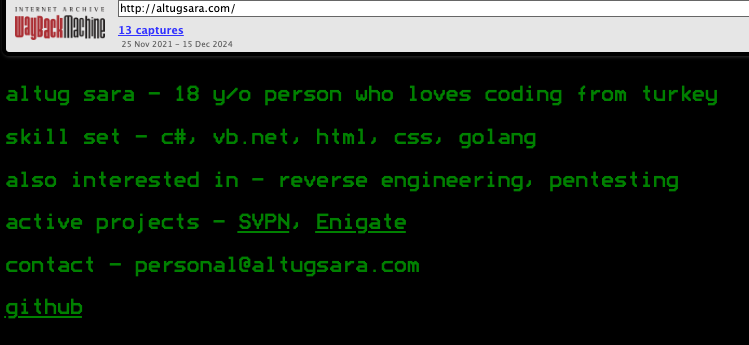
Archive.org’s recollection of what altugsara dot com seemed like in 2021.
LinkedIn finds this similar altugsara[.]com area listed within the “contact info” part of a profile for an Altug Sara from Ankara, who says he has labored the previous two years as a senior software program developer for a Turkish IT agency known as Bilitro Yazilim.
Neither Altug Sara nor Bilitro Yazilim responded to requests for remark.
Invicti’s web site states that it has places of work in Ankara, however the firm’s CEO stated none of their workers acknowledged both identify.
“We do have a small team in Ankara, but as far as I know we have no connection to the individual other than the fact that they are also in Ankara,” Invicti CEO Neil Roseman instructed KrebsOnSecurity.
Researchers at Silent Push say regardless of Araneida utilizing a seemingly infinite provide of proxies to masks the true location of its customers, it’s a pretty “noisy” scanner that can kick off a big quantity of requests to numerous API endpoints, and make requests to random URLs related to completely different content material administration programs.
What’s extra, the cracked model of Acunetix being resold to cybercriminals invokes legacy Acunetix SSL certificates on lively management panels, which Silent Push says supplies a stable pivot for locating a few of this infrastructure, notably from the Chinese risk actors.
Further studying: Silent Push’s analysis on Araneida Scanner.
[ad_2]
