[ad_1]
Suspected Russian menace actors have been focusing on Eastern European customers within the crypto trade with pretend job alternatives as bait to put in information-stealing malware on compromised hosts.
The attackers “use a number of extremely obfuscated and under-development customized loaders so as to infect these concerned within the cryptocurrency trade with Enigma stealer,” Trend Micro researchers Aliakbar Zahravi and Peter Girnus mentioned in a report this week.
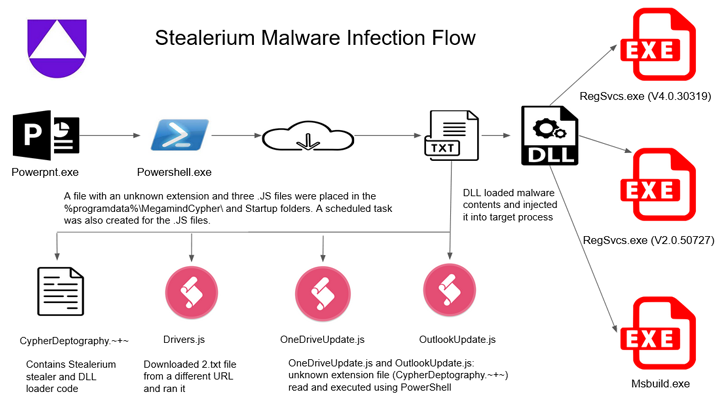
Enigma is claimed to be an altered model of Stealerium, an open supply C#-based malware that acts as a stealer, clipper, and keylogger.
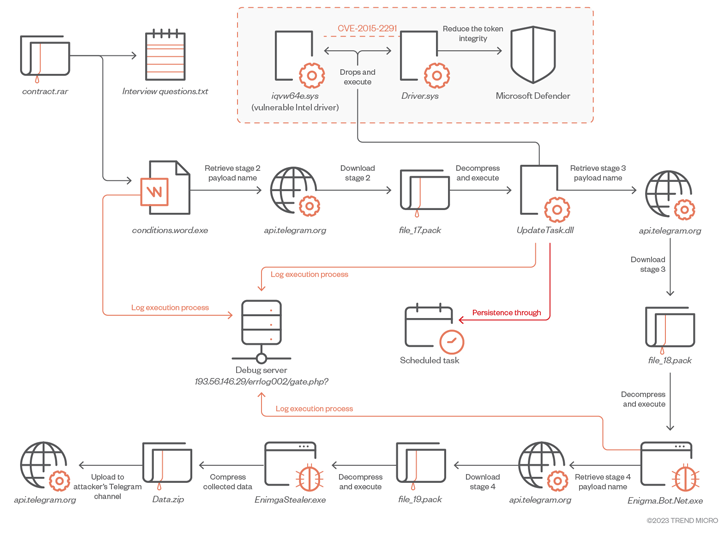
The intricate an infection journey begins with a rogue RAR archive file that is distributed through phishing or social media platforms. It accommodates two paperwork, one in every of which is a .TXT file that features a set of pattern interview questions associated to cryptocurrency.
The second file is a Microsoft Word doc that, whereas serving as a decoy, is tasked with launching the first-stage Enigma loader, which, in flip, downloads and executes an obfuscated secondary-stage payload via Telegram.
“To obtain the subsequent stage payload, the malware first sends a request to the attacker-controlled Telegram channel […] to acquire the file path,” the researchers mentioned. “This method permits the attacker to constantly replace and eliminates reliance on fastened file names.”
The second-stage downloader, which is executed with elevated privileges, is designed to disable Microsoft Defender and set up a third-stage by deploying a legitimately signed kernel mode Intel driver that is weak to CVE-2015-2291 in a method known as Bring Your Own Vulnerable Driver (BYOVD).
It’s value noting that the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the vulnerability to its Known Exploited Vulnerabilities (KEV) catalog, citing proof of energetic exploitation within the wild.
The third-stage payload in the end paves the way in which for downloading Enigma Stealer from an actor-controlled Telegram channel. The malware, like different stealers, comes with options to reap delicate data, document keystrokes, and seize screenshots, all of which is exfiltrated again via Telegram.
Bogus job gives are a tried-and-tested tactic employed by North Korea-backed Lazarus Group in its assaults focusing on the crypto sector. The adoption of this modus operandi by Russian menace actors “demonstrates a persistent and profitable assault vector.”
The findings come as Uptycs launched particulars of an assault marketing campaign that leverages the Stealerium malware to siphon private information, together with credentials for cryptocurrency wallets reminiscent of Armory, Atomic Wallet, Coinomi, Electrum, Exodus, Guarda, Jaxx Liberty, and Zcash, amongst others.
Joining Enigma Stealer and Stealerium in focusing on cryptocurrency wallets is one more malware dubbed Vector Stealer that additionally comes with capabilities to steal .RDP recordsdata, enabling the menace actors to hold out RDP hijacking for distant entry, Cyble mentioned in a technical write-up.
Attack chains documented by the cybersecurity companies present that the malware households are delivered via Microsoft Office attachments containing malicious macros, suggesting that miscreants are nonetheless counting on the strategy regardless of Microsoft’s makes an attempt to shut the loophole.
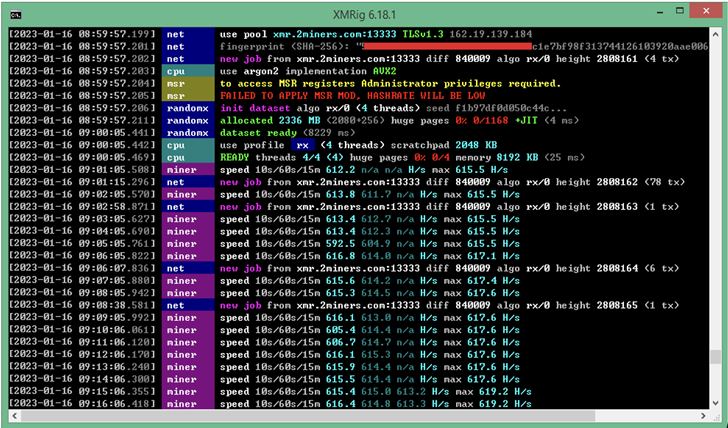
An identical technique has additionally been put to make use of to deploy a Monero crypto miner in opposition to the backdrop of a cryptojacking and phishing marketing campaign aimed toward Spanish customers, in response to Fortinet FortiGuard Labs.
The improvement can also be the most recent in a protracted listing of assaults which can be aimed toward stealing victims’ cryptocurrency property throughout platforms.
This includes a “quickly evolving” Android banking trojan known as TgToxic, which plunders credentials and funds from crypto wallets in addition to financial institution and finance apps. The ongoing malware marketing campaign, energetic since July 2022, is directed in opposition to cell customers in Taiwan, Thailand, and Indonesia.
“When the sufferer downloads the pretend app from the web site given by the menace actor, or if sufferer tries to ship a direct message to the menace actor via messaging apps reminiscent of WhatsApp or Viber, the cybercriminal deceives the consumer into registering, putting in the malware, and enabling the permissions it wants,” Trend Micro mentioned.
The rogue apps, apart from abusing Android’s accessibility companies to hold out the unauthorized fund transfers, can also be notable for benefiting from professional automation frameworks like Easyclick and Auto.js to carry out clicks and gestures, making it the second Android malware after PixPirate to include such workflow IDEs.
But social engineering campaigns have additionally gone past social media phishing and smishing by establishing convincing touchdown pages that imitate well-liked crypto companies with the aim of transferring Ethereum and NFTs from the hacked wallets.
This, in response to Recorded Future, is achieved by injecting a crypto drainer script into the phishing web page which lures victims into connecting their wallets with profitable gives to mint non-fungible tokens (NFTs).
Such ready-made phishing pages are being bought on darknet boards as a part of what’s known as a phishing-as-a-service (PhaaS) scheme, allowing different actors to lease out these packages and swiftly enact malicious operations at scale.
“‘Crypto drainers’ are malicious scripts that perform like e-skimmers and are deployed with phishing strategies to steal victims’ crypto property,” the corporate mentioned in a report printed final week, describing the scams as efficient and rising in reputation.
“The use of professional companies on crypto drainer phishing pages could enhance the chance that the phishing web page will go an in any other case savvy consumer’s ‘rip-off litmus check.’ Once crypto wallets have been compromised, no safeguards exist to forestall the illicit switch of property to attackers’ wallets.”
The assaults come at a time when legal teams have stolen a record-breaking $3.8 billion from crypto companies in 2022, with a lot of the spike attributed to North Korean state-sponsored hacking crews.
[ad_2]