[ad_1]
Cybersecurity researchers have found the real-world id of the risk actor behind Golden Chickens malware-as-a-service, who goes by the net persona “badbullzvenom.”
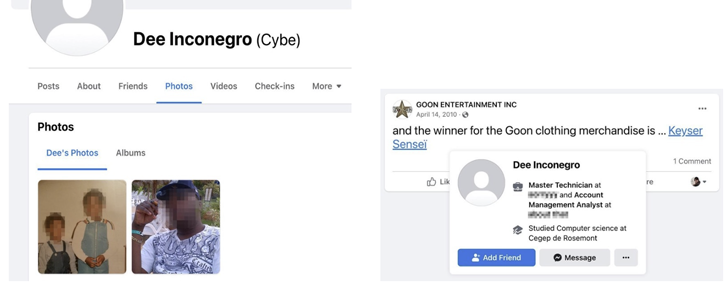
eSentire’s Threat Response Unit (TRU), in an exhaustive report revealed following a 16-month-long investigation, stated it “discovered a number of mentions of the badbullzvenom account being shared between two folks.”
The second risk actor, often called Frapstar, is alleged to establish themselves as “Chuck from Montreal,” enabling the cybersecurity agency to piece collectively the prison actor’s digital footprint.
This consists of his actual title, photos, house handle, the names of his mother and father, siblings, and associates, alongside together with his social media accounts and his pursuits. He can be stated to be the only proprietor of a small enterprise that is run from his own residence.
Golden Chickens, also referred to as Venom Spider, is a malware-as-a-service (MaaS) supplier that is linked to quite a lot of instruments akin to Taurus Builder, software program to create malicious paperwork; and More_eggs, a JavaScript downloader that is used to serve further payloads.
The risk actor’s cyber arsenal has been put to make use of by different distinguished cybercriminal teams like Cobalt Group (aka Cobalt Gang), Evilnum, and FIN6, all of that are estimated to have collectively brought about losses totaling $1.5 billion.
Past More_eggs campaigns, some courting again to 2017, have concerned spear-phishing enterprise professionals on LinkedIn with bogus job gives that give risk actors distant management over the sufferer’s machine, leveraging it to reap info or deploy extra malware.
Last yr, in a reversal of types, the identical ways had been employed to strike company hiring managers with resumes laden with malware as an an infection vector.
The earliest documented file of Frapster’s exercise goes again to May 2015, when Trend Micro described the person as a “lone prison” and a luxurious automobile fanatic.
“‘Chuck,’ who makes use of a number of aliases for his underground discussion board, social media, and Jabber accounts, and the risk actor claiming to be from Moldova, have gone to nice lengths to disguise themselves,” eSentire researchers Joe Stewart and Keegan Keplinger stated.
“They have additionally taken nice pains to obfuscate the Golden Chickens malware, attempting to make it undetectable by most AV corporations, and limiting prospects to utilizing Golden Chickens for ONLY focused assaults.”
It’s suspected that Chuck is without doubt one of the two risk actors working the badbullzvenom account on the Exploit.in underground discussion board, with the opposite social gathering presumably positioned in Moldova or Romania, eSentire famous.
The Canadian cybersecurity firm stated it additional uncovered a brand new assault marketing campaign focusing on e-commerce corporations, tricking recruiters into downloading a rogue Windows shortcut file from a web site that masquerades as a resume.
The shortcut, a malware dubbed VenomLNK, serves as an preliminary entry vector to drop More_eggs or TerraLoader, which subsequently acts as a conduit to deploy completely different modules, specifically TerraRecon (for sufferer profiling), TerraStealer (for info theft), and TerraCrypt (for ransomware extortion).
“The malware suite remains to be actively being developed and is being and offered to different risk actors,” the researchers concluded, urging organizations to be looking out for potential phishing makes an attempt.
[ad_2]