[ad_1]
A current IcedID malware assault enabled the menace actor to compromise the Active Directory area of an unnamed goal lower than 24 hours after gaining preliminary entry.
“Throughout the assault, the attacker adopted a routine of recon instructions, credential theft, lateral motion by abusing Windows protocols, and executing Cobalt Strike on the newly compromised host,” Cybereason researchers mentioned in a report revealed this week.
IcedID, additionally recognized by the title BokBot, began its life as a banking trojan in 2017 earlier than evolving right into a dropper for different malware, becoming a member of the likes of Emotet, TrickBot, Qakbot, Bumblebee, and Raspberry Robin.
Attacks involving the supply of IcedID have leveraged a wide range of strategies, particularly within the wake of Microsoft’s choice to dam macros from Office information downloaded from the online.
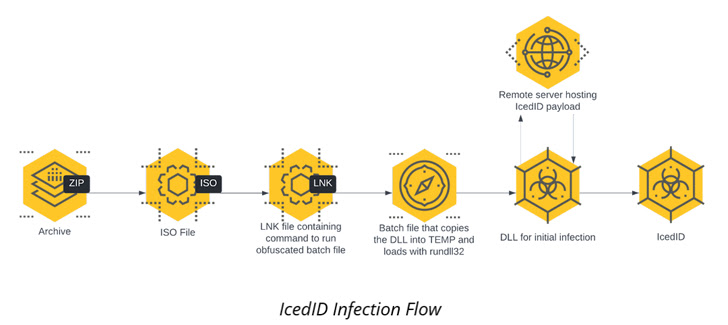
The intrusion detailed by Cybereason isn’t any totally different in that the an infection chain begins with an ISO picture file contained inside a ZIP archive that culminates within the execution of the IcedID payload.
The malware then establishes persistence on the host through a scheduled activity and communicates with a distant server to obtain further payloads, together with Cobalt Strike Beacon for follow-on reconnaissance exercise.
It additionally carries out lateral motion throughout the community and executes the identical Cobalt Strike Beacon in all these workstations, after which proceeds to put in Atera agent, a reliable distant administration device, as a redundant distant entry mechanism.
“Utilizing IT instruments like this enables attackers to create a further ‘backdoor’ for themselves within the occasion their preliminary persistence mechanisms are found and remediated,” the researchers mentioned. “These instruments are much less more likely to be detected by antivirus or EDR and are additionally extra more likely to be written off as false positives.”
The Cobalt Strike Beacon is additional used as a conduit to obtain a C# device dubbed Rubeus for credential theft, in the end allowing the menace actor to maneuver laterally to a Windows Server with area admin privileges.
The elevated permissions are then weaponized to stage a DCSync assault, permitting the adversary to simulate the habits of a site controller (DC) and retrieve credentials from different area controllers.
Other instruments used as a part of the assault embody a reliable utility named netscan.exe to scan the community for lateral motion in addition to the rclone file syncing software program to exfiltrate directories of curiosity to the MEGA cloud storage service.
The findings come as researchers from Team Cymru shed extra mild on the BackConnect (BC) protocol utilized by IcedID to ship further performance put up compromise, together with a VNC module that gives a remote-access channel.
“In the case of BC, there seems to be two operators managing the general course of inside distinct roles,” the researchers famous final month, including “a lot of the exercise […] happens in the course of the typical working week.”
The improvement additionally follows a report from Proofpoint in November 2022 {that a} resurgence in Emotet exercise has been linked to the distribution of a brand new model of IcedID.
[ad_2]