[ad_1]
Part 1 and Part 2 of this weblog collection lined native cloud networking and firewall guidelines automation on GCP, and a learn via is advisable for completeness. This last put up of the collection is about enabling exterior entry for cloud sources. More particularly, it would give attention to how prospects can allow exterior connectivity from and to GCP, utilizing both Cloud Native Router or Cisco Cloud Router (CCR) primarily based on Cisco Catalyst 8000v, relying on use case.
By increasing earlier capabilities, Cisco Cloud Network Controller (CNC) will provision routing, automate VPC peering between infra and person VPCs, and BGP IPSec connectivity to exterior networks with just a few steps utilizing the identical coverage mannequin.
Scenario
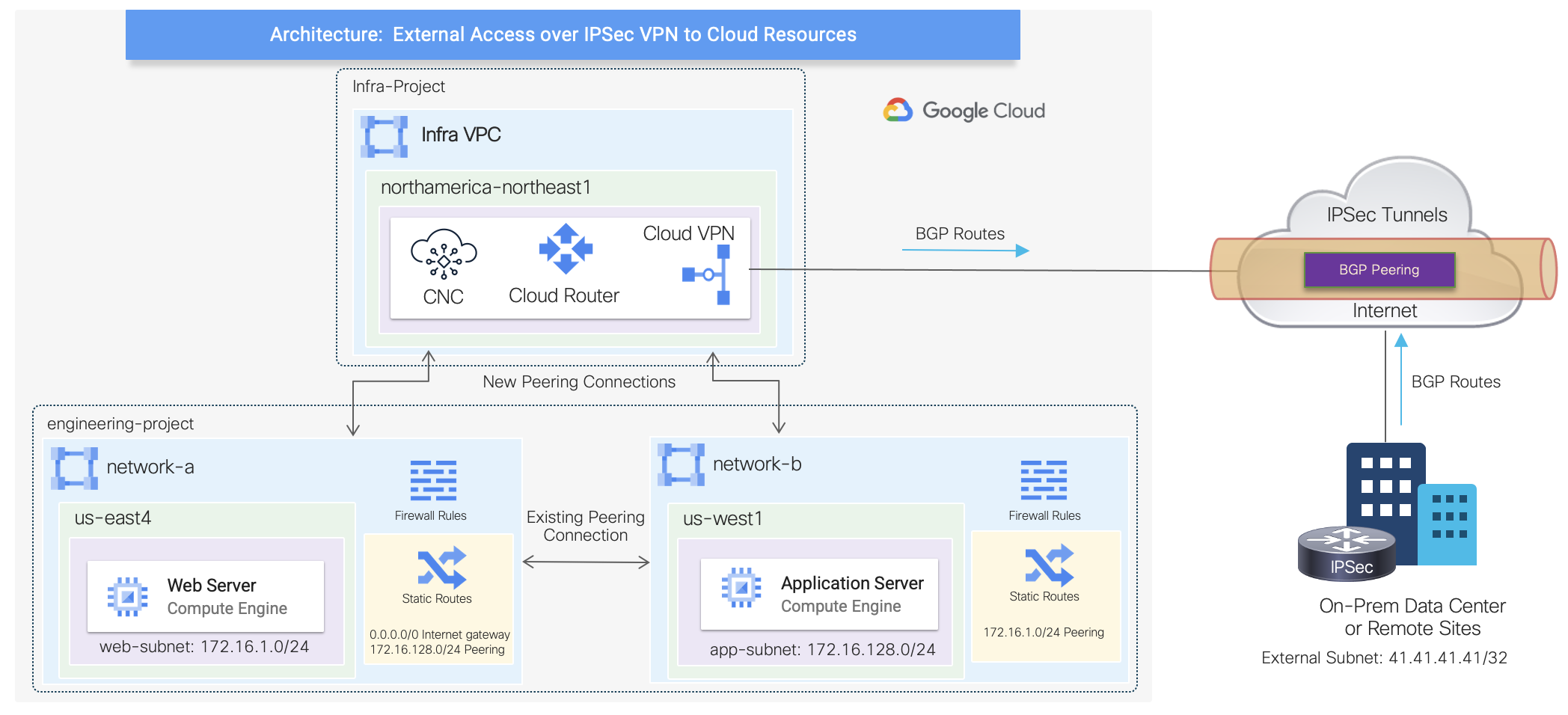
This state of affairs will leverage the present configuration constructed beforehand represented by network-a and network-b VPCs. These person VPCs will likely be peered with the infra VPC in a hub and spoke structure, the place GCP cloud native routers will likely be provisioned to determine BGP IPSec tunnels with an exterior IPSec system. The GCP cloud native routers are composed by the mix of a Cloud Router and a High-availability (HA) Cloud VPN gateway.
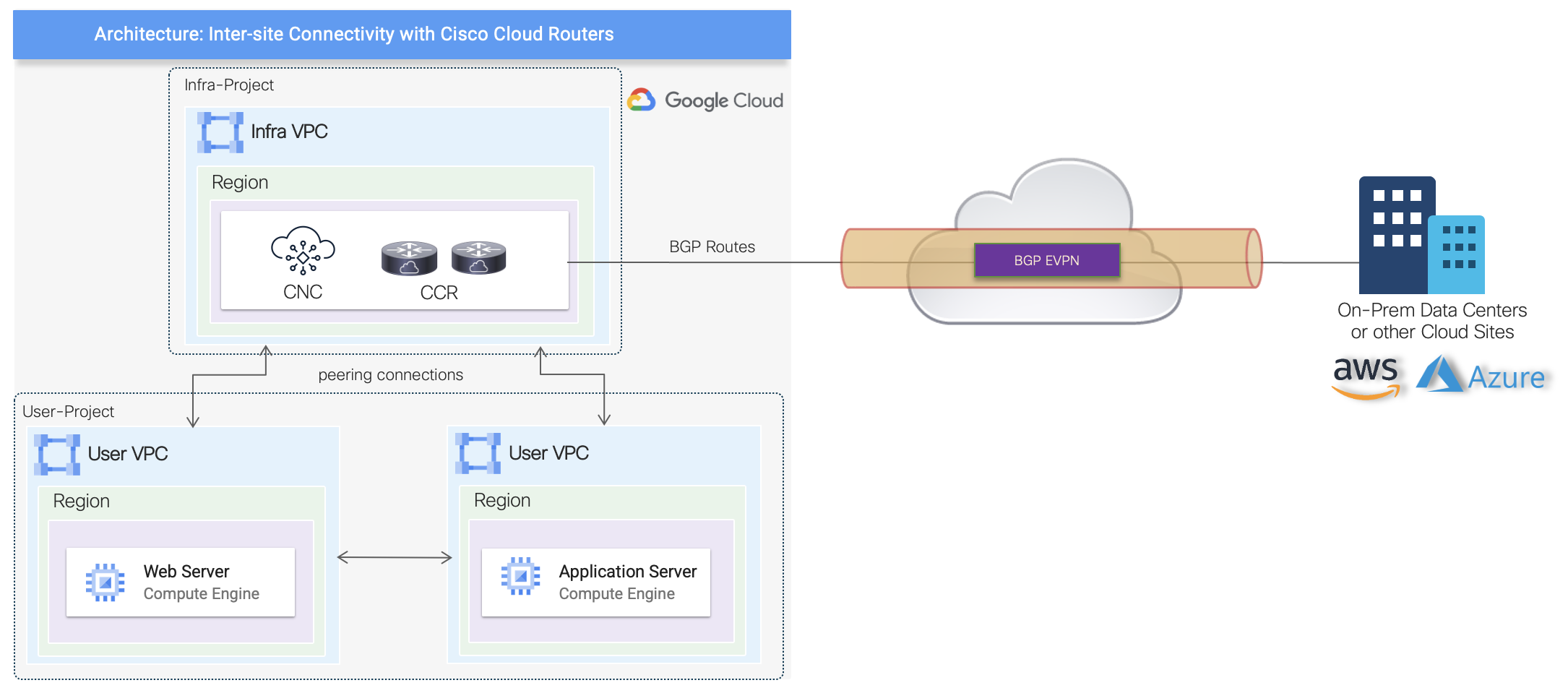
The high-level topology beneath illustrates the extra connections automated by Cisco CNC.
Provisioning Cloud Native Routers
The first step is to allow exterior connectivity underneath Region Management by choosing during which area cloud native routers will likely be deployed. For this state of affairs, they are going to be provisioned in the identical area because the Cisco CNC as depicted on the high-level topology. Additionally, default values will likely be used for the IPSec Tunnel Subnet Pool and BGP AS underneath the Hub Network representing the GCP Cloud Router.
The cloud native routers are being provisioned purposely on a unique area as an instance the flexibility of getting a devoted hub community with exterior entry. However, they might have been deployed on the identical area because the person VPCs.
Note: a quick overview of the Cisco CNC GUI was supplied on Part 1.
Enabling External Networks
The subsequent step is to create an External Network assemble inside the infra tenant. This is the place an exterior VRF can be outlined to characterize exterior networks related to on-premises knowledge facilities or distant websites. Any cloud VRF mapped to current VPC networks can leak routes to this exterior VRF or can get routes from it. In addition to the exterior VRF definition, that is additionally the place VPN settings are entered with the distant IPSec peer particulars.
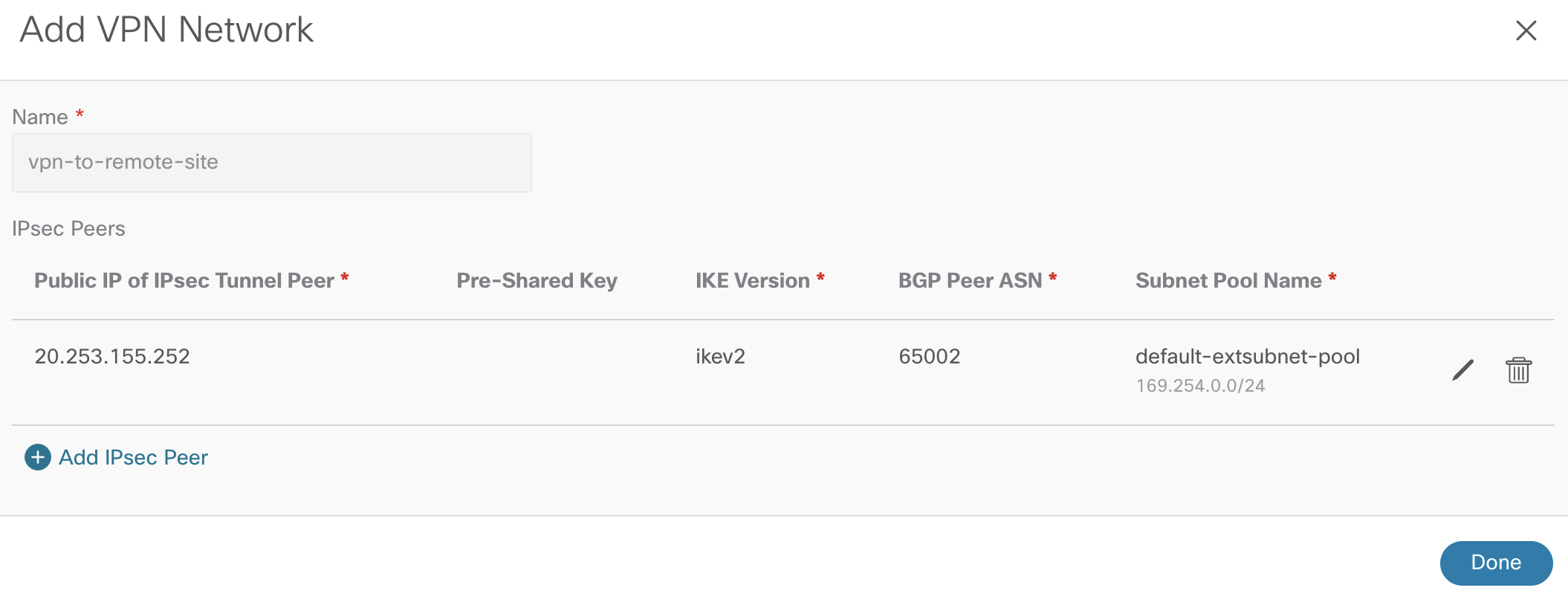
The configuration beneath illustrates the stitching of the exterior VRF and the VPN community inside the area the place the cloud native routers are being provisioned within the backend. For simplicity, the VRF was named as “external-vrf” however in a manufacturing atmosphere, the identify needs to be outlined correctly and aligned to the exterior community as to enhance operations.
The VPN community settings require public IP of the distant IPSec system, IKE model, and BGP AS. As indicated earlier, the default subnet pool is getting used.
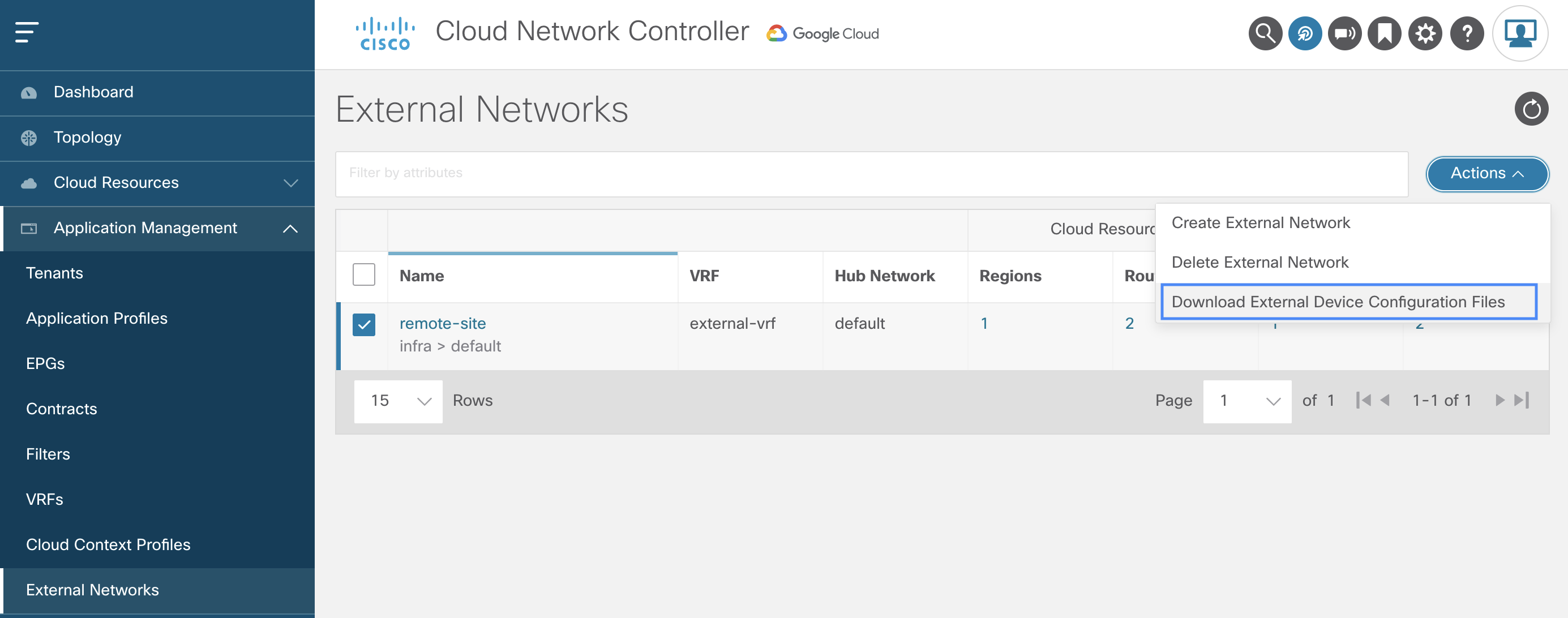
 Once the exterior community is created, Cisco CNC generates a configuration file for the distant IPSec system to determine BGP peering and IPSec tunnels with the GCP cloud native routers. Below is the choice to obtain the configuration file.
Once the exterior community is created, Cisco CNC generates a configuration file for the distant IPSec system to determine BGP peering and IPSec tunnels with the GCP cloud native routers. Below is the choice to obtain the configuration file.
Configuring External IPSec Device
As the configuration file offers a lot of the configuration required for the exterior IPSec system, customization is required solely on tunnel supply interface and routing settings the place relevant to match native community necessities. In this instance, the distant IPSec system is a digital router utilizing interface GigabitEthernet1. For brevity, solely one of many IPSec tunnels config is proven beneath together with all the opposite config generated by Cisco CNC.
vrf definition external-vrf rd 100:1 address-family ipv4 exit-address-family interface Loopback0 vrf forwarding external-vrf ip handle 41.41.41.41 255.255.255.255 crypto ikev2 proposal ikev2-1 encryption aes-cbc-256 aes-cbc-192 aes-cbc-128 integrity sha512 sha384 sha256 sha1 group 24 21 20 19 16 15 14 2 crypto ikev2 coverage ikev2-1 proposal ikev2-1 crypto ikev2 keyring keyring-ifc-3 peer peer-ikev2-keyring handle 34.124.13.142 pre-shared-key 49642299083152372839266840799663038731 crypto ikev2 profile ikev-profile-ifc-3 match handle native interface GigabitEthernet1 match identification distant handle 34.124.13.142 255.255.255.255 identification native handle 20.253.155.252 authentication distant pre-share authentication native pre-share keyring native keyring-ifc-3 lifetime 3600 dpd 10 5 periodic crypto ipsec transform-set ikev-transport-ifc-3 esp-gcm 256 mode tunnel crypto ipsec profile ikev-profile-ifc-3 set transform-set ikev-transport-ifc-3 set pfs group14 set ikev2-profile ikev-profile-ifc-3 interface Tunnel300 vrf forwarding external-vrf ip handle 169.254.0.2 255.255.255.252 ip mtu 1400 ip tcp adjust-mss 1400 tunnel supply GigabitEthernet1 tunnel mode ipsec ipv4 tunnel vacation spot 34.124.13.142 tunnel safety ipsec profile ikev-profile-ifc-3 ip route 34.124.13.142 255.255.255.255 GigabitEthernet1 192.168.0.1 router bgp 65002 bgp router-id 100 bgp log-neighbor-changes address-family ipv4 vrf external-vrf community 41.41.41.41 masks 255.255.255.255 neighbor 169.254.0.1 remote-as 65534 neighbor 169.254.0.1 ebgp-multihop 255 neighbor 169.254.0.1 activate
Verifying External Connectivity standing
Once configuration is utilized, there are a number of methods to confirm BGP peering and IPSec tunnels between GCP and exterior units: by way of CLI on the IPSec system itself and by way of Cisco CNC GUI on the External Connectivity dashboard.
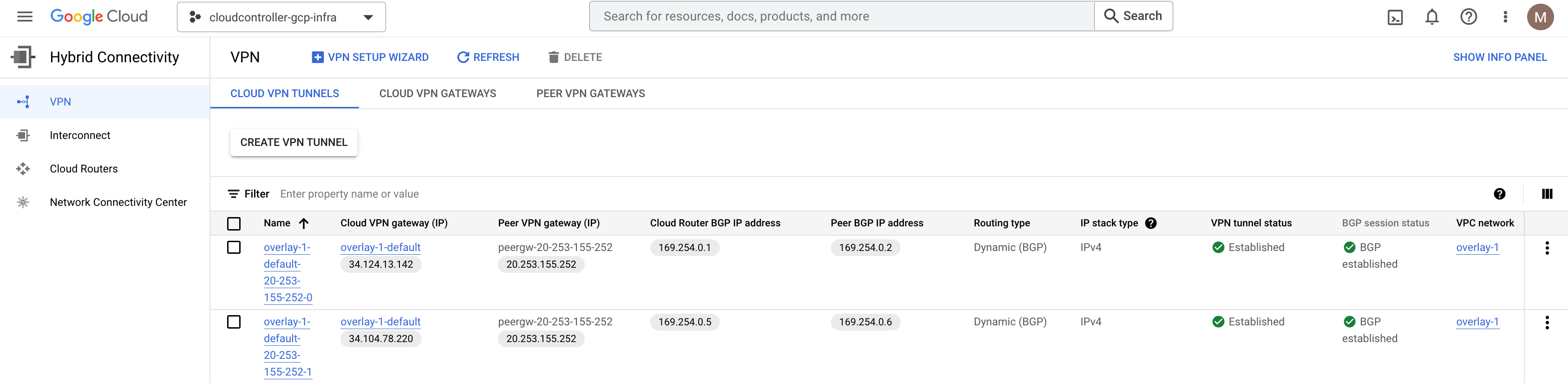
In the GCP console (infra undertaking), underneath Hybrid Connectivity, it exhibits each the IPSec and BGP periods are established accordingly by the mix of a Cloud Router and an HA Cloud VPN gateway automated by Cisco CNC, upon definition of the External Network. Note that the infra VPC community is called as overlay-1 by default as a part of the Cisco CNC deployment from {the marketplace}.
Route Leaking Between External and VPC Networks
Now that BGP IPSec tunnels are established, let’s configure inter-VRF routing between exterior networks and current person VPC networks from earlier sections. This works by enabling VPC peering between the person VPCs and the infra VPC internet hosting VPN connections, which is able to share these VPN connections to exterior websites. Routes obtained on the VPN connections are leaked to person VPCs, and person VPC routes are marketed on the VPN connections.
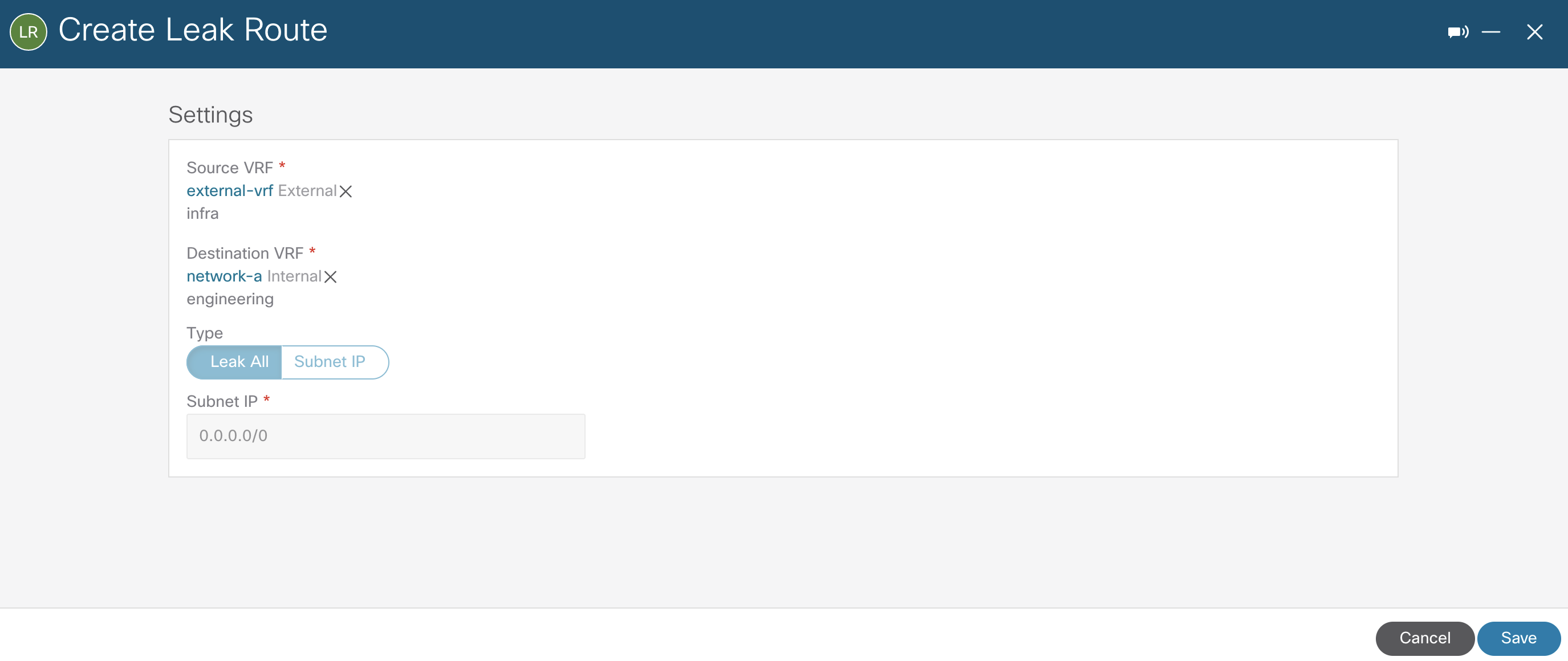
Using inter-VRF routing, the route is leaked between the exterior VRF of the VPN connections and the cloud native person VRFs. The configuration beneath illustrates route leaking from external-vrf to network-a.
The reverse route leaking configuration from network-a to external-vrf is filtered with Subnet IP to point out granularity. Also, the identical steps have been carried out for network-b however not depicted for brevity.
In addition to the present peering between network-a and network-b VPCs, now each person VPCs are additionally peered with the infra VPC (overlay-1) as depicted on the high-level topology.
By exploring one of many peering connection particulars, it’s potential to see the exterior subnet 41.41.41.41/32 within the imported routes desk.
On the distant IPSec system, the subnets from network-a and network-b VPCs are realized over BGP peering as anticipated.
remote-site#sh bgp vpnv4 unicast vrf external-vrf <<<output omitted for brevity>>> Network Next Hop Metric LocPrf Weight Path Route Distinguisher: 100:1 (default for vrf external-vrf) *> 41.41.41.41/32 0.0.0.0 0 32768 i * 172.16.1.0/24 169.254.0.5 100 0 65534 ? *> 169.254.0.1 100 0 65534 ? * 172.16.128.0/24 169.254.0.5 100 0 65534 ? *> 169.254.0.1 100 0 65534 ? remote-site#
Defining External EPG for the External Network
Up up to now, all routing insurance policies have been automated by Cisco CNC to permit exterior connectivity to and from GCP. However, firewall guidelines are additionally required for end-to-end connectivity. This is achieved by creating an exterior EPG utilizing subnet choice because the endpoint selector to characterize exterior networks. Note that this exterior EPG can be created inside the infra tenant and related to the external-vrf created beforehand.
The subsequent step is to use contracts between the exterior EPG and the beforehand created cloud EPGs to permit communication between endpoints in GCP and exterior networks, which on this state of affairs is represented by 41.41.41.41/32 (loopback0 on distant IPSec system). As that is occurring throughout totally different tenants, the contract scope is about to world and exported from the engineering tenant to the infra tenant and vice-versa, if permitting visitors to be initiated from each side.


On the backend, the mix of contracts and filters interprets into correct GCP firewall guidelines, as lined in particulars on Part 2 of this collection. For brevity, solely the end result is supplied beneath.
remote-site#ping vrf external-vrf 172.16.1.2 supply lo0
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.16.1.2, timeout is 2 seconds:
Packet despatched with a supply handle of 41.41.41.41 !!!!!
Success price is one hundred pc (5/5), round-trip min/avg/max = 84/84/86 ms
remote-site#ping vrf external-vrf 172.16.128.2 supply lo0
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 172.16.128.2, timeout is 2 seconds:
Packet despatched with a supply handle of 41.41.41.41 !!!!!
Success price is one hundred pc (5/5), round-trip min/avg/max = 132/133/138 ms
root@web-server:/house/marinfer# ping 41.41.41.41 PING 41.41.41.41 (41.41.41.41) 56(84) bytes of knowledge. 64 bytes from 41.41.41.41: icmp_seq=1 ttl=254 time=87.0 ms 64 bytes from 41.41.41.41: icmp_seq=2 ttl=254 time=84.9 ms 64 bytes from 41.41.41.41: icmp_seq=3 ttl=254 time=83.7 ms 64 bytes from 41.41.41.41: icmp_seq=4 ttl=254 time=83.8 ms root@web-server:/house/marinfer# root@app-server:/house/marinfer# ping 41.41.41.41 PING 41.41.41.41 (41.41.41.41) 56(84) bytes of knowledge. 64 bytes from 41.41.41.41: icmp_seq=1 ttl=254 time=134 ms 64 bytes from 41.41.41.41: icmp_seq=2 ttl=254 time=132 ms 64 bytes from 41.41.41.41: icmp_seq=3 ttl=254 time=131 ms 64 bytes from 41.41.41.41: icmp_seq=4 ttl=254 time=136 ms root@app-server:/house/marinfer#
Advanced Routing Capabilities with Cisco Cloud Router
Leveraging native routing capabilities as demonstrated could suffice for some particular use circumstances and be restricted for others. Therefore, for extra superior routing capabilities, Cisco Cloud Routers will be deployed as an alternative. The provisioning course of is comparatively the identical with CCRs additionally instantiated inside the infra VPC in a hub and spoke structure. Besides being able to handle the whole lifecycle of the CCRs from the Cisco CNC, prospects may also select totally different tier-based throughput choices primarily based on necessities.
One of the principle use circumstances for leveraging Cisco Cloud Routers is the BGP EVPN help throughout totally different cloud websites working Cisco CNC, or for hybrid cloud connectivity with on-prem websites when coverage extension is fascinating. The totally different inter-site makes use of circumstances are being documented on particular white papers, and beneath is a high-level topology illustrating the structure.
Summary
There are a number of methods of enabling exterior entry and hybrid cloud connectivity for cloud sources. Cisco CNC offers flexibility to prospects by giving choices to leverage native routing capabilities or extra superior options with CCR. Additionally, though not lined as a part of this collection, skill to import and handle connectivity to brownfield VPCs can be supported to deal with use circumstances with current VPC networks.
In conclusion, this weblog collection introduces Cisco CNC for patrons to discover and perceive the advantages of leveraging a cloud networking software program to automate and construct their cloud environments on GCP. Moreover, Cisco CNC makes it straightforward to combine with current cloud automation instruments corresponding to Terraform by publishing steady supplier updates.
Resources
Guides
Cisco Cloud Network Controller for Google Cloud Installation Guides
Cisco Cloud Network Controller for Google Cloud User Guides
Blog Series: Introducing Cisco Cloud Network Controller on Google Cloud Platform
Part 1: Native Cloud Networking Automation
Part 2: Contract-based Routing and Firewall Rules Automation
Share:
[ad_2]